This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
Like Active Directory Domain Services, Azure AD does not just hold user and group data. We can also register or join devices to our Azure AD instance. Having a connection between our devices and Azure AD allows us to benefit from some great features such as Microsoft Endpoint Manager (Intune), Windows Defender for Endpoint and also provides some useful authentication capabilities which can streamline user access to tenant resources.
When connecting devices to Azure AD, we have three options based on the device we are working with:
- Azure AD Register
- The device is registered with Azure AD, the users corporate account is linked in the Operating System under “Accounts” and SSO to cloud resources is provided
- Limited management of the device using Microsoft Endpoint Manager (Intune) from the corporate context is available to the organization
- Authentication to the device remains local, Windows Hello can be used for device authentication
- Perfect for BYOD scenarios
- Self-Service Registration is available
- Azure AD Join
- The device is fully joined to Azure AD, the users corporate account is used to authenticate to the device and SSO to cloud resources is provided
- Full device management is available via Microsoft Endpoint Manager
- Authentication is provided by Azure AD, Windows Hello for Business can be used for both device and corporate authentication
- Perfect for managed devices with no local Active Directory instance
- Self-Service Join can be enabled in Azure AD
- Hybrid Azure AD Join
- The device is joined to both local Active Directory and to Azure AD. The users corporate account is used to authenticate to the device and SSO to cloud resources is provided
- Full device management is available via Microsoft Endpoint Manager or on-premises GPO
- Authentication is provided by Azure AD, Windows Hello for Business can be used for both device and corporate authentication, including on-premises resources
- Perfect for managed devices which are already joined to an on-premises AD domain
- Join is managed by the on-premises AD environment

Device Authentication with Windows Hello for Business
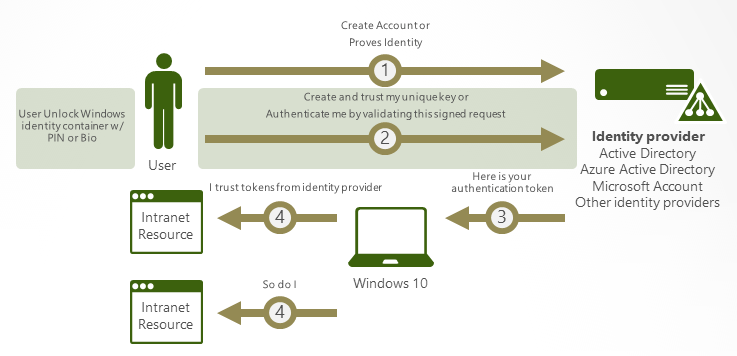
When we join a device to Azure AD, we can take advantage of Windows Hello for Business. Windows Hello for Business allows us to remove the requirement for user passwords during the authentication flow by using the trusted device and data which is specific to both the user and device itself, to authenticate. Windows Hello for Business can be used in cloud only, on-premises and Hybrid on-premises scenarios. We won’t go into detail on the on-prem only deployment for the exam but more information can be found on that here.

In a cloud or hybrid environment with Azure AD Premium, Windows Hello for Business can be used from Windows 10 1511 onwards. It can be provisioned at device registration and is enabled via Microsoft Endpoint Manager (Intune or SCCM) or GPO. There are various settings which can be enabled to tailor the behaviour of Windows Hello for your organization, these settings are listed here. Some key configuration items that should be noted are:
- Use Windows Hello for Business – This enables Windows Hello for Business, setting to disabled or not configured will prevent Windows Hello provisioning
- Use a hardware security device – Enabling this setting will force the provisioning to use the devices Trusted Platform Module (TPM), it is strongly recommended to use TPM for Windows Hello for Business. Not enabling this setting will allow devices that do not support TPM to store the private key in software which opens up vulnerability to potential attack. More information on this here
- Use certificate for on-premises authentication – This setting tells Windows Hello if it should use certificate or Key for on-premises authentication
For Cloud only environments, the above settings are all that are needed to configure Windows Hello. Authentication is performed using the device private key verified by the user data and access is granted. To the user this is a biometric/pin and MFA to gain access to their device, then SSO for all applications.
For hybrid environments, it is a bit more complex. As mentioned above, there are two approaches to hybrid deployments of Windows Hello for Business, Key Trust and Certificate based. At a high level, the characteristics of a Key Trust Deployment are:
- A minimum number of Windows Server 2016 or Later Domain Controllers Required
- Windows 10, version 1703 or later
- Minimum Domain and Forest functional level of Windows Server 2008 R2
- An Enterprise PKI (Windows Server 2012 or higher) is required for Domain Controller trust
- Requires ADFS federation, Password Hash or Pass Through Authentication
- Requires Azure AD Connect
For Certificate Trust deployments, the high-level characteristics are:
- Windows Server 2016 or later Directory Schema is required
- Windows 10, version 1703 or later
- Minimum Domain and Forest functional level of Windows Server 2008 R2
- An Enterprise PKI (Windows Server 2012 or higher) is required for Domain Controller trust and to issue user certificates for use with on-premises authentication
- Only supports a federated environment using ADFS 2016 or higher
- Requires Azure AD Connect
Summary
There is quite a bit of planning required for Windows Hello for Business. Luckily each deployment type is well documented so the biggest challenge is planning. As this topic can get very detailed I have included below a lot of links which provide more information on each concept. For the exam itself, I recommend knowing the concepts and steps to configure.
What are Azure AD registered devices? | Microsoft Docs
What is an Azure AD joined device? | Microsoft Docs
What is a hybrid Azure AD joined device? | Microsoft Docs
Plan your Azure Active Directory device deployment | Microsoft Docs
How to plan your Azure Active Directory join implementation | Microsoft Docs
Plan hybrid Azure Active Directory join – Azure Active Directory | Microsoft Docs
How Windows Hello for Business works – Microsoft 365 Security | Microsoft Docs
How Windows Hello for Business works – Authentication – Microsoft 365 Security | Microsoft Docs
Windows Hello biometrics in the enterprise (Windows 10) – Microsoft 365 Security | Microsoft Docs
How SSO to on-premises resources works on Azure AD joined devices | Microsoft Docs
Primary Refresh Token (PRT) and Azure AD – Azure Active Directory | Microsoft Docs

Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue