Running regular Phishing Simulations in your environment is a great way to keep up user awareness and vigilance and help them to identify common phishing attacks and malicious email. In a previous post I have detailed the process of using the awesome Microsoft Defender for Office 365 Attack Simulation tool. If you are licensed for Defender for Office 365 Plan 2, then the tool gives you some great functionality to manage simulations within your Office 365 environment.
Of course, not everyone has licensing in place for this and a lot of organizations use other mail hygiene products such as Mimecast to provide protection to users and to run similar simulations. Running simulations from external sources can be tricky in Exchange Online, particularly if there are protections in place via Defender for Office 365.
To allow this mail to be successfully delivered, we can use Advanced Delivery in Exchange Online to bypass filtering for the source of the simulation. This process can also be used to allow delivery to particular secops mailboxes that require unfiltered mail to be delivered for review.
How Advanced Delivery Works
For third Party Phishing simulations, Advanced Delivery allows admins to specify Domain and IPs which will be used in the simulation. For each simulation source, there must be at least one domain and one IP. Specific URLs can also be added to ensure that simulated URLs do not get scanned / detonated by Defender.
When a Phishing Simulation “endpoint” is created, messages from the simulation will be assigned a system bypass to regular scanning and display on Threat Explorer as Phishing Simulations. Malware Filtering and ZAP can not be bypassed so it’s worth considering however, sending malware to users as a ‘test’ is probably not a great idea anyway…
For SecOps mailboxes, an internal mailbox is added to allow unfiltered messages to flow to this mailbox only. This means that security teams who want to analyze blocked or flagged mails can do so without Defender blocking the content.
Configuring Advanced Delivery for SecOps Mailboxes
Before specifying a mailbox, make sure a dedicated mailbox is set up for the purpose of analyzing malicious mails. I don’t recommend setting this to an active user or admin account for obvious reasons. To configure Advanced Delivery, open the Microsoft 365 Security Center and navigate to “Policies & Rules” -> “Threat Policies” -> “Advanced Delivery”. On the “SecOps Mailbox” tab, select the “Add” button shown in Figure 1.

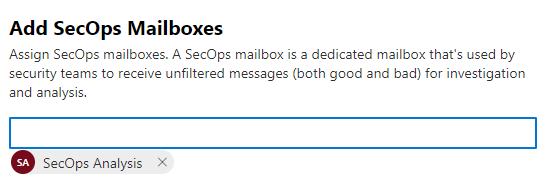
In the “Add SecOps Mailboxes” page, add in the mailbox by address as shown in Figure 2 and click “add”. Once the mailbox is added, mails sent to it will bypass the protections detailed above.
Configuring Advanced Delivery for Phishing Simulations
To configure Advanced Delivery for Phishing Simulations, open the “Phishing Simulation” tab of the “Advanced Delivery” page and click “Add”. In the pop out window, add the domains and IPs the phishing simulation will come from (Figure 3) and optionally any URLs that will need to be resolved for the simulation to work.

With the details added, Phishing Simulations from the defined source domains / IPs will bypass the protections details above.
Summary
Advanced Delivery is a great way of running external Phishing and awareness campaigns without exposing the environment to additional risk. It’s important for both SecOps mailboxes and Phishing Campaigns to ensure the details are correct and not open to a larger list of endpoints.
For anyone who hasn’t tried it, I really recommend the Microsoft Defender for Office 365 Phishing simulation functionality. This doesn’t require Advanced Delivery and for organizations with Defender for Office 365 Plan 2 licensing, provides a lot of flexibility.

