Microsoft have recently announced the availability of Azure Log analytics for Azure AD sign-in and audit logging. This is a really cool feature, especially for large organizations where there will be a lot of traffic to audit. In this post I will go through the basic setup.
Prerequisites:
- Azure AD Global Admin
- Azure Subscription
Log onto the Azure portal page and select Azure Active Directory > Diagnostic settings -> Add diagnostic setting
Select the option to “Turn on diagnostics” if it is not already turned on and configure Azure AD Diagnostics. Select the option to “Send to Log analytics” and click “Configure” to create a new OMS workspace. Choose to send either Audit logs, Sign-In Logs or both to Log analytics.


Click ‘Save’ to finalize the setup.
Wait for 15 minutes or so for the data to begin sending to Log Analytics. (Time to grab some tea)
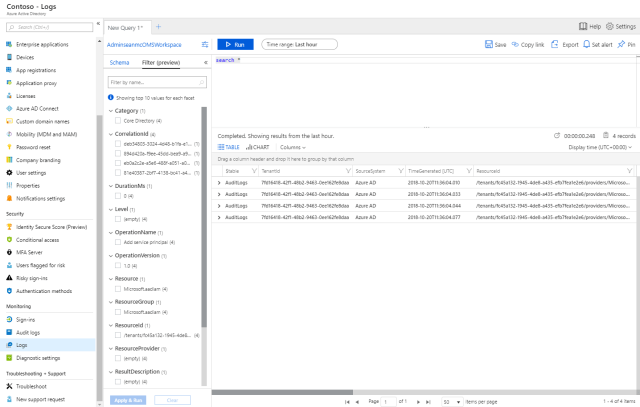
When you’ve finished your tea, select Azure Active Directory > Monitoring > Logs to view your new Log analytics workspace.
We can see in the default query that the configuration itself is showing up in the logs:
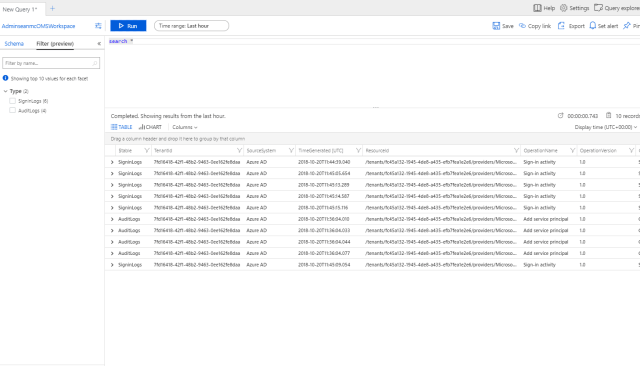
Now lets generate some sign in traffic by logging in as a user. After logging in, wait for 5 or so minutes for the log to show up.
After a couple of minutes, we can see sign in logs in our default query.
Using Log analytics, we can configure custom queries and set alerts and actions on pretty much anything that happens in Azure AD. This is an extremely powerful tool for organizations to leverage to enhance security, governance and automation across the platform.

