Segregation of admin roles in Microsoft 365 has always been a challenge. Different admin roles help to apply the principal of least privilege for admins but there was always an issue where multiple logical groupings existed in a single tenant. They are not always managed globally and not every admin should have access to every user where divisional barriers exist. Exchange Online Management Role Scopes do a good job of facilitating different groupings in Exchange Online but for user management in Azure AD or Microsoft 365, this became a challenge.
Do we give the local IT support for a particular division access to our entire userbase or do we take on the support of the M365 accounts for these users at a group level?
When we use AD Connect and local Active Directory as our identity source, we can use delegated permissions to provide a lot of the required access. Couple this with some cool features like group-based licensing and we can effectively delegate management to local or divisional IT support.
With more organizations forgoing local AD completely for cloud based Azure AD/Intune, this management delegation became trickier. Microsoft appreciate this challenge in the platform and have made available (in preview) Azure AD Administrative Units.
Administrative Units allow us to define logical groupings of users and delegate admin roles for these specific groups to our administrators.
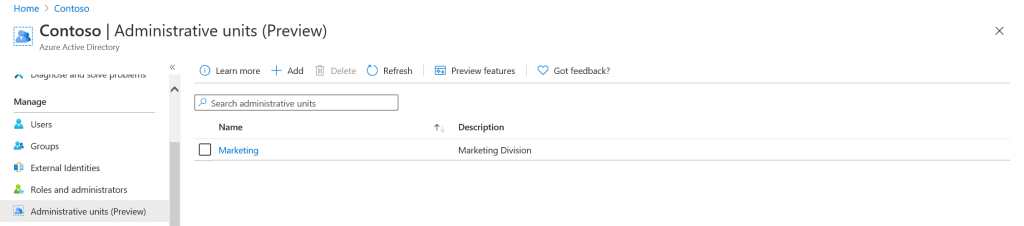
To achieve this we first create an Administrative Unit in the Azure AD Portal.
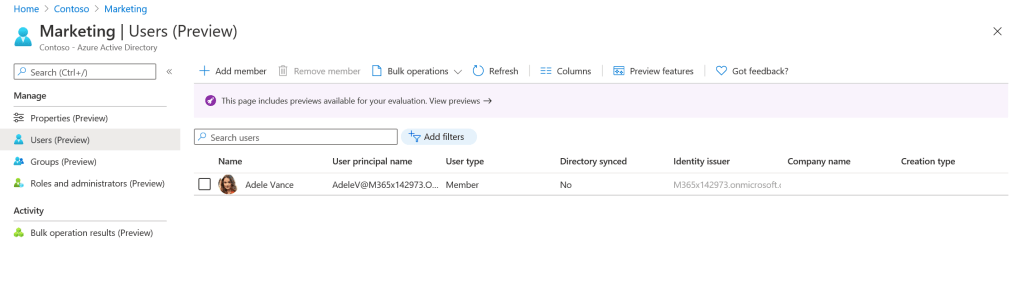
From here we can add our users / groups to the unit so they can be managed.
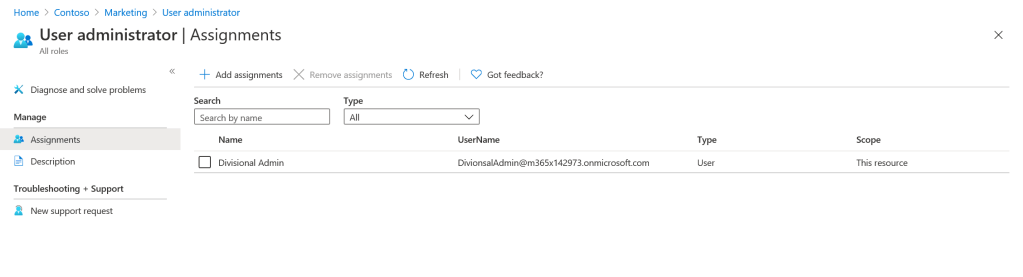
We can then assign our administrators and grant the the appropriate roles.
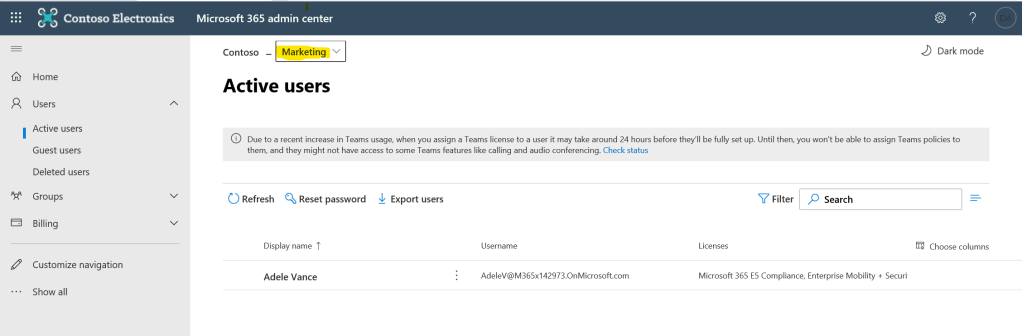
Once complete, our administrator can log in to the Admin Portal and only see the Administrative Units they have been assigned.
This feature is bound to be a blessing for large organizations who can now feel more confident to delegate day to day management to divisional or local IT, reducing the management overhead involved in new user creation, Group Membership, Licensing and password resets


Pingback: Study Guide Series: Exam MS-500 – Implement Role-Based Access Control (RBAC) – Sean McAvinue