This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement role-based access control (RBAC)” section:
- Plan for roles
- Configure roles
- Audit roles
Admin Best Practices
Before we look at RBAC, here are some high level best practices around admin roles first:
- There should be more than one Global Admin account for the tenancy but ideally less than 5
- Admin roles should not be assigned to any users regular account, i.e. the one they use daily for email or Teams etc.
- There should never be a generic admin account created, this goes for regular accounts also, named individual accounts should be used for full traceability
- Privileged Identity Management should be used to provide Just in time (JIT) role assignments. We will go through PIM in detail in a future post
- MFA should be enforced on all admin role accounts, this can be achieved through Conditional Access, this should not be bypassed by any other factor such as location as we would with regular user accounts
- A single, “Break Glass” Admin account should be preserved for emergencies such as an MFA outage. This account should have a complex password and alerting should be configured for every sign-in attempt. The password for this account should ideally be rotated at regular intervals
- It’s worth checking out a previous post I did about Azure AD Administrative Units which allow segregation of administration across logical business units
Plan for Roles
Role-Based Access as a concept has been around a long time, the idea of assigning appropriate permission levels to role groups to simplify management and ensure the principal of least privilege is followed isn’t new. As with on-premises systems, this concept can be applied to Microsoft 365 Administration, ensuring that our admins have the right level of permissions to carry out their job, without overexposing our tenancy by granting Global Admin rights to everyone.
To plan for role assignments, first let’s look at the roles available, there are a wide variety of Azure AD roles we can assign and Microsoft have documented them very well here. I highly recommend getting familiar with the roles and inherent access associated with each. For a more tailored list of roles, Microsoft have also published the below table here. This table represents the subset of Azure AD roles which are available in the Microsoft 365 Admin Center. You will need to know each of these roles for the exam.
| Admin role | Description |
|---|---|
| Application admin | Full access to enterprise applications, application registrations, and application proxy settings. |
| Application developer | Create application registrations and consent to app access on their own behalf. |
| Authentication admin | Can require users to re-register authentication for non-password credentials, like MFA. |
| Azure Information Protection admin | Manages labels for the Azure Information Protection policy, manages protection templates, and activates protection. |
| Billing admin | Makes purchases, manages subscriptions, manages service requests, and monitors service health. |
| Cloud application admin | Full access to enterprise applications and application registrations. No application proxy. |
| Cloud device admin | Enables, disables, and deletes devices and can read Windows 10 BitLocker keys. |
| Compliance admin | Manages regulatory requirements and eDiscovery cases, maintains data governance for locations, identities, and apps. |
| Compliance data admin | Keeps track of data, makes sure it’s protected, gets insights into issues, and helps mitigate risk. |
| Conditional Access admin | Manages Azure Active Directory conditional access settings, but not Exchange ActiveSync conditional access policy. |
| Customer Lockbox access approver | Manages Customer Lockbox requests, can turn Customer Lockbox on or off. |
| Desktop Analytics admin | Can access and manage Desktop management tools and services. |
| Dynamics 365 admin | Full access to Microsoft Dynamics 365 Online, manages service requests, monitors service health. |
| Exchange admin | Full access to Exchange Online, creates and manages groups, manages service requests, and monitors service health. |
| External identity provider admin | Configure identity providers for use in direct federation. |
| Global admin | Has unlimited access to all management features and most data in all admin centers. |
| Global reader | Has read-only access to all management features and most data in admin centers. For a detailed description of access rights and limitations of this role, please see Administrator role permissions in Azure Active Directory. |
| Groups admin | Creates groups and manages all groups settings across admin centers. |
| Guest inviter | Manages Azure Active Directory B2B guest user invitations. |
| Helpdesk admin | Resets passwords and re-authenticates for all non-admins and some admin roles, manages service requests, and monitors service health. |
| Insights admin | Manages all aspects of the Microsoft 365 Insights application, reads Azure Active Directory information, can monitor service health and create and manage service requests. |
| Insights business admin | Read reports and insights in the Microsoft 365 Insights application. |
| Intune admin | Full access to Intune, manages users and devices to associate policies, creates and manages groups. |
| Kaizala admin | Full access to all Kaizala management features and data, manages service requests. |
| License admin | Assigns and removes licenses from users and edits their usage location. |
| Message center privacy reader | Access to data privacy messages in Message center, gets email notifications. |
| Message center reader | Reads and shares regular messages in Message center, gets weekly email digests, has read-only access to users, groups, domains, and subscriptions. |
| Office Apps admin | Manages cloud-based policies for Office and the What’s New content that users see in their Office apps. |
| Password admin | Reset passwords of users who are non-administrators or members of the following roles: Directory Readers, Guest Inviter, Password Administrator. This role can’t grant the ability to manage service requests or monitor service health. |
| Power BI admin | Full access to Power Bl management tasks, manages service requests, and monitors service health. |
| Power platform admin | Full access to Microsoft Dynamics 365, PowerApps, data loss prevention policies, and Microsoft Flow. |
| Privileged role admin | Manages role assignments and all access control features of Privileged Identity Management. |
| Privileged authentication admin | Resets passwords, updates non-password credentials, forces uses to sign out and monitors service health and manages service requests. |
| Reports reader | Reads usage reporting data from the reports dashboard, PowerBI adoption content pack, sign-in reports, and Microsoft Graph reporting API. |
| Search admin | Full access to Microsoft Search, assigns the Search admin and Search editor roles, manages editorial content, monitors service health, and creates service requests. |
| Search editor | Can only create, edit, and delete content for Microsoft Search, like bookmarks, Q&A, and locations. |
| Security admin | Controls organization’s security, manages security policies, reviews security analytics and reports, monitors the threat landscape. |
| Security operator | Investigates and responds to security alerts, manages features in Identity Protection center, monitors service health. |
| Security reader | Read-only access to security features, sign-in reports, and audit logs. |
| Service support admin | Creates service requests for Azure, Microsoft 365, and Office 365 services, and monitors service health. |
| SharePoint admin | Full access to SharePoint Online, manages Microsoft 365 groups, manages service requests, and monitors service health. |
| Skype for Business admin | Full access to all Teams and Skype features, Skype user attributes, manages service requests, and monitors service health. |
| Teams admin | Full access to Teams & Skype admin center, manages Microsoft 365 groups and service requests, and monitors service health. |
| Teams communication manager | Assigns telephone numbers, creates and manages voice and meeting policies, and reads call analytics. |
| Teams communication support engineer | Reads call record details for all call participants to troubleshoot communication issues. |
| Teams communication support specialist | Reads user call details only for a specific user to troubleshoot communication issues. |
| User admin | Resets user passwords, creates and manages users and groups, including filters, manages service requests, and monitors service health. |
Planning roles is simple once you have the list available, we just need to map out our requirements and assign to the role that meets our requirements maintaining least privilege. For example, let’s take a couple of common scenarios:
Scenario 1
A level one engineer who’s role involves performing password resets and updating user data such as group membership
In this case, looking at our available roles, Global Admin meets the requirement but assigns way too much access. Helpdesk admin will allow for password resets but not Group management, similar for Password Admin. User Admin however, allows password resets and Group management, while not giving too much else.
Scenario 2
We have hired a consultant to audit the organizations security posture. They have been tasked with reviewing the Microsoft 365 configuration. They should not be able to make any configuration changes but should be able to review the configuration in place without relying on another admin.
Again, Global Admin would give the appropriate permissions but would also allow the user to make changes. Security Admin would limit access to only security configuration but still allow changes to be made. Security Reader however, limits the access and prevents changes.
Scenario 3
A member of the finance team manages all purchasing and payment of Microsoft 365 subscriptions and licensing. The receive requests for licensing when they are approved and normally need to screen share with an admin to procure licensing, this is a very slow process. The CFO has requested that they are given the ability to purchase without relying on the IT department.
The only role outside of Global Admin that will grant this ability is the Billing Admin role. This will allow the finance team member to manage purchasing of subscriptions / licensing while not giving them access to any configuration.
Configure Roles
One we have the right role selected for our account, assignment is easy. It is strongly recommended to user Privileged Identity Management (PIM) rather than assigning static roles. We will go through PIM in a future post so for now, we will look at static assignments.
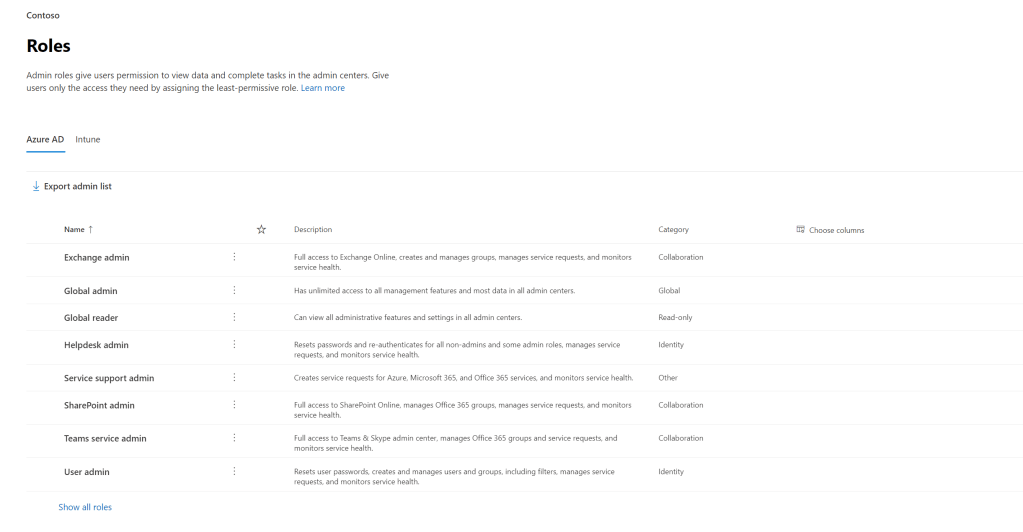
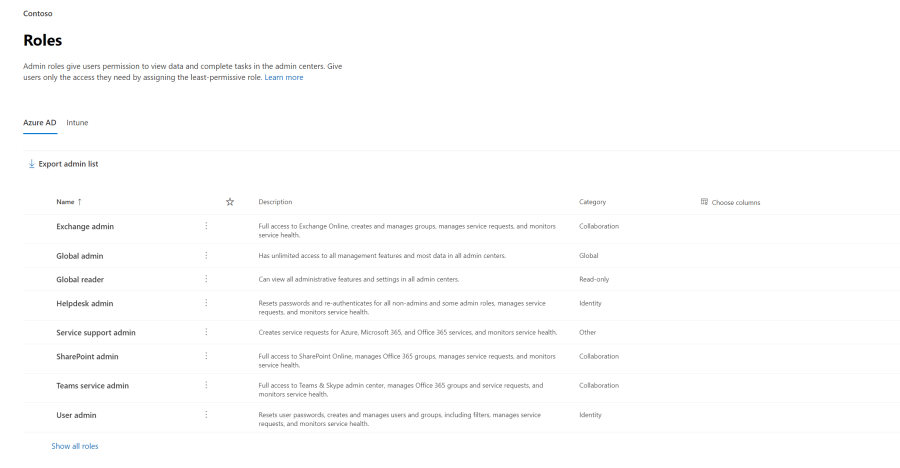
To add a user to a role, open up the Microsoft 365 admin portal and open up the Roles section. From here we can see the roles we have available for assignment along with a description and category to help us ensure we assign the appropriate role.
To assign a role to an account, simply select the role we want to assign, in the pop-out pane, select “Assigned Admins” and click “Add”.
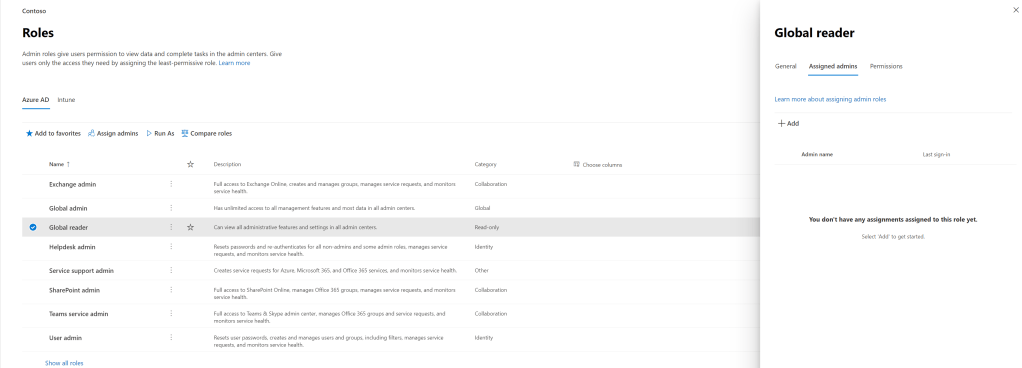
Add the account in to assign the role.

From here we can also view any permissions assigned to the role, compare two roles and even test drive the role to see what access the user should expect.
That’s all there is to assigning roles. As I mentioned, in production we should be using PIM to make roles available and we will detail that process in an upcoming post.
Audit Roles
Once Roles have been assigned to users, no matter the context, it’s extremely important that we audit the roles we have assigned. Luckily, we have some really handy tools available to us. Let’s look at some of them here.
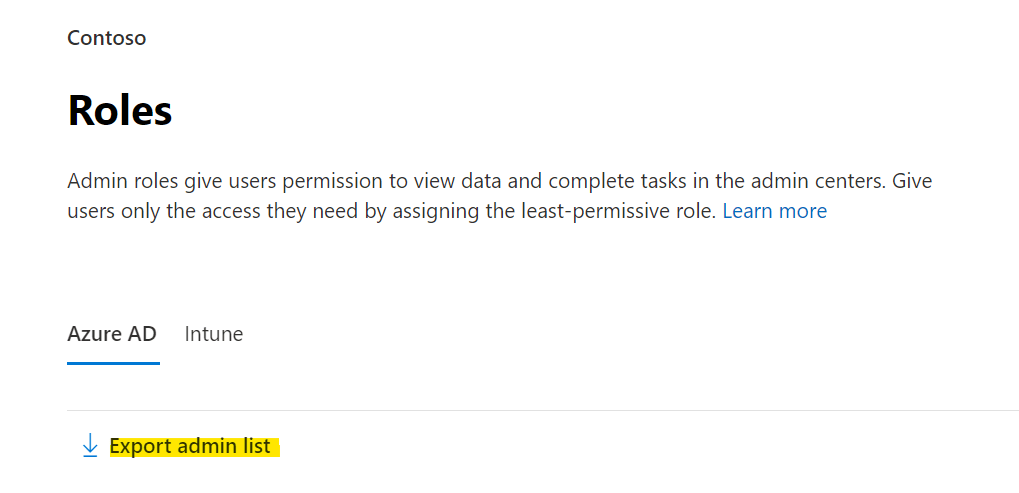
Export Admin List
The quickest and easiest way to get a list of admin role assignments is directly from the “Roles” page. We have an option near the top to “Export Admin List”. This option will export a comma-delimited CSV listing all of our users with Admin roles assigned.
Unified Audit Log Search
If we want to audit admin activities, we can search the audit log in the Compliance Center, here we can open up “Solutions” and “Audit” and filter our search for specific activities. In the below example, we are searching our Audit log for all activities related to one of our Global Admins. This functionality is also available in the legacy Security and Compliance Center however will be moved in the near future so I recommend getting to know both pages.
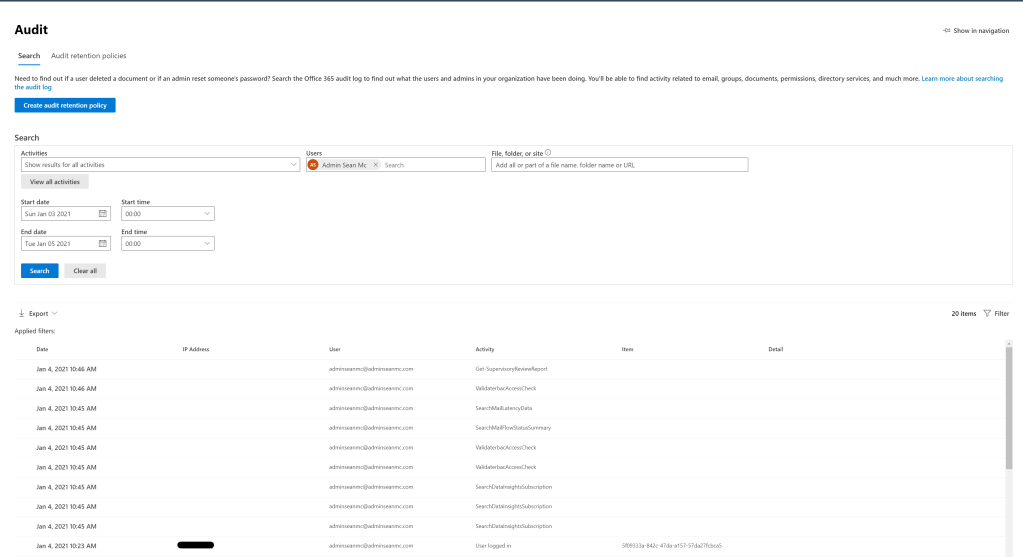
Note that we can filter by specific activities and we can also return non-admin activities. We can also user the “Export” button to export our search results to CSV. We will go through Audit Log Search in detail in a future post. It is also possible to search the Unified Audit Log through PowerShell with the Search-UnifiedAuditLog cmdlet.
Alert Policies
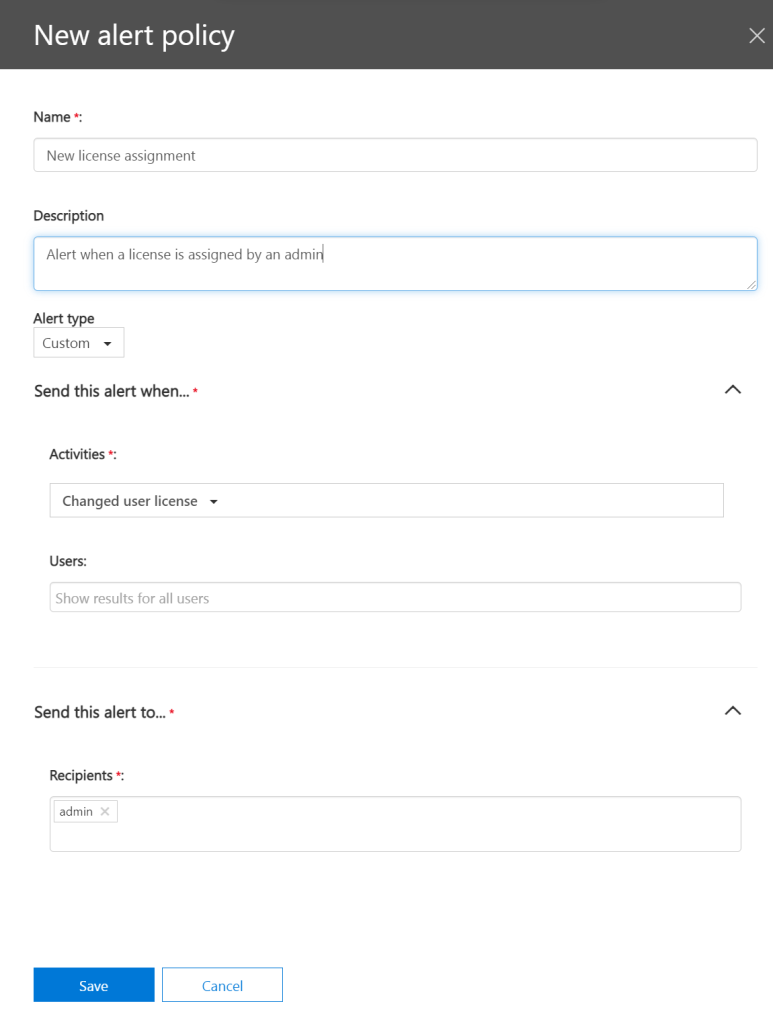
Based on our Unified Audit Log, we can also configure alerting to inform us when a specific action is taken. To do this we configure Alert Policies. Alert Policies are currently only available in the Security & Compliance Center but like the Unified Audit Log, will move to the new page in time.
We can set up a new alert by opening the Security & Compliance Center and navigating to “Search” and “Audit Log Search”. If we click “New alert policy” we can configure an alert based on our defined criteria, in the below example, we will set up an alert to trigger every time a new license is assigned.
First we classify it with a name, description, severity and alert type. The alert type will be custom but we can also use the built-in “elevation of privileges” alert type to detect when admin roles and assigned. We can filter by user and choose who to send the alert to. When we are done, hit “Save” to activate the alert.
Alert Policy functionality is extended by using Microsoft Cloud App Security (MCAS) which is a topic for a later post.
Summary
Here we have looked at assigning and auditing admin roles directly through Microsoft 365. This is great for small scale deployments with permanent Admin roles however in the next post. we will look at assigning roles through PIM which makes management and auditing of admin role assignments a lot easier and secure.
For some more information around admin roles in Microsoft 365, check out the below Microsoft links:
Assign admin roles the Microsoft 365 admin center – Microsoft 365 admin | Microsoft Docs
Search the audit log in the Security & Compliance Center – Microsoft 365 Compliance | Microsoft Docs
Turn audit log search on or off – Microsoft 365 Compliance | Microsoft Docs
Search-UnifiedAuditLog (ExchangePowerShell) | Microsoft Docs
Alert policies in the security and compliance centers – Microsoft 365 Compliance | Microsoft Docs

Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Study Guide Series: Exam MS-500 – Implement Azure AD Privileged Identity Management (PIM) – Sean McAvinue