Sensitivity Labels have quickly become a core component of any Enterprise level Microsoft 365 tenancy. Information Governance is becoming more and more relevant in the Cloud space where we potentially have a enormous amount of disparate unstructured data in various Teams, SharePoint Sites, OneDrive etc.
Depending on the license SKU, Sensitivity labels can allow manual or automated protection of data – at an item level – based on predefined or even Machine Learning modeled classifications (Trainable Classifiers). We can even classify Office 365 Groups/Microsoft Teams for some cool features.
Another piece of the Information Governance puzzle is Data-Loss Prevention (DLP). DLP allows us to Prevent data leaving the organization via file sharing and/or Email. We typically define DLP policies to protect data based on contents such as keywords or particular patterns.
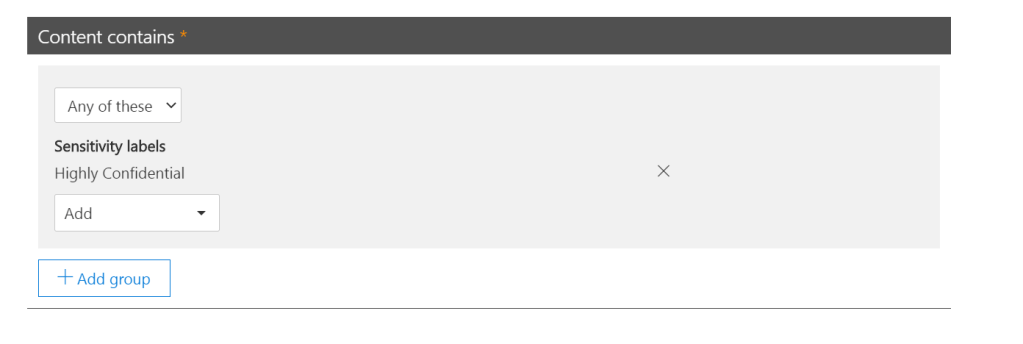
As of this month, we get access (in Preview) to the ability to use Sensitivity Labels as criteria in DLP Policies! This not only prevent double up of work aligning sensitivity and DLP policies, but allows us to protect that data that users classify themselves or even as a result of our Trainable Classifiers.
In the below example we are creating a custom DLP Policy which we will configure to detect a particular sensitivity label added to our content.

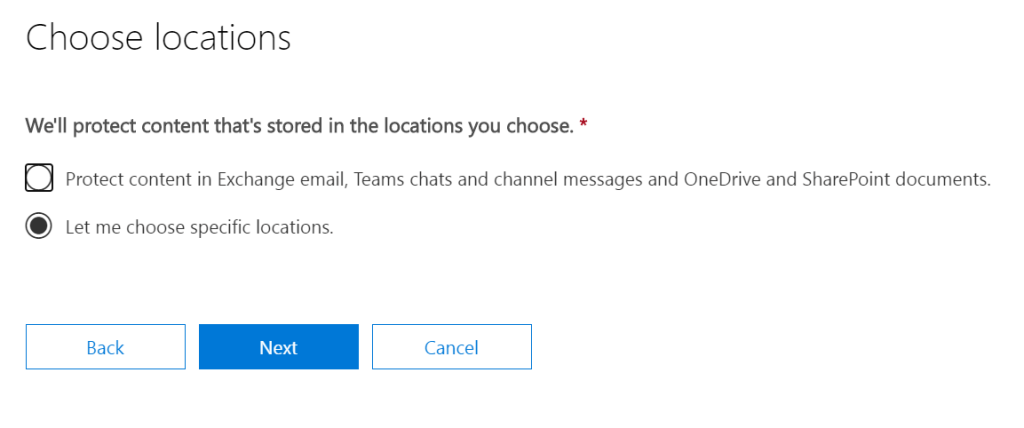
We exclude Teams Chat and Channel messages from the policy as they can’t be applied sensitivity on their own so are not supported for this policy. (Teams file sharing comes from SharePoint so we’re still covered there)


And that’s it, we’ve protected our Sensitivity Label with DLP! All that’s left is for us to assign our actions and we’re done!

This is a really nice addition to the feature set for Microsoft 365 Compliance and helps tie together some really powerful features, giving admins better control over data egress. If you haven’t already, it’s definitely worthwhile checking out some of the other Information Protection features available in the Microsoft 365.

Pingback: Study Guide Series: Exam MS-500 – Manage Sensitivity Labels (Part 1) – Sean McAvinue
Pingback: Securing External Access to Files in Teams: The Two Most Important Basic Configurations – Sean McAvinue