This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
Protecting user identities during sign-on to Microsoft 365 services has never been more important. With the shift this year to working from home, many organizations have had to rethink their remote access strategy. With this massive change in how users access services, there has also been a massive increase in attempts by malicious actors to take advantage of this shift by using phishing attacks, brute force, malware etc.
Organizations need to be aware of the risks associated with any externally available or cloud service and plan security options around this. Luckily, there is a robust set of tools available through Microsoft 365 / Azure AD which can assist organizations in planning an implementing a secure sign-on process.
Sign-on Security Options
The user authentication flow for Microsoft 365 is managed by Azure AD. To understand how we plan a solution, we need to first be aware of the options available to us:
- Conditional Access allows us to control sign-on based on several factors that we know from the users sign-on attempt
- Multi-Factor Authentication can be used to provide a second layer of verification for users
- Device State for managed devices can tell us if the device is compliant with our corporate policies and make decisions based on that
- Client Device OS can be used to treat mobile devices differently to Windows or Mac
- Location can allow us to treat sign-on attempts differently depending on the users physical location (based on IP address)
- Client App can tell us the application that the user is using to access services, we can then enforce additional controls such as Mobile Application Management
- The Cloud App that the user is accessing can also be specified and treated differently, potentially allowing for tiered access based on the risk associated with a service
- Limit access via Cloud App Security e.g. Read-Only access when remote
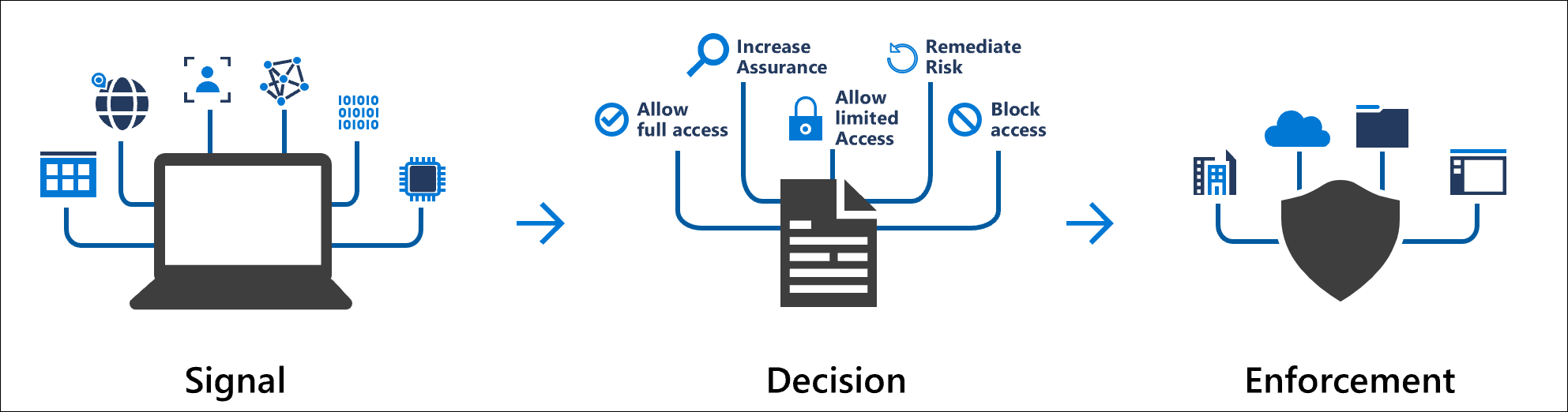
- Azure AD Identity Protection can make informed decisions on the risk associated with a given user identity or sign-on attempt based on factors such as geographical distance from the previous sign-on, frequency of sign-on, user credentials being leaked to online databases etc.
- Windows Hello for Business can provide us with alternate authentication options such as biometrics
- Cloud App Security can proxy and control user sessions to limit functionality
- Auditing and Alerting can give insight into user sign-on behaviours and identify potential risks

It’s important to build the access policy to meet our business and security requirements leveraging the wealth of functionality available to us. Over the course of this study guide, we will dive into each of these options in detail, looking at when and how we would configure each option.

Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Study Guide Series – Exam MS-500: Configure and Manage Azure AD User Authentication Options and Self-Service Password Management – Sean McAvinue