This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
Note: Azure Advanced Threat Protection has recently been renamed Microsoft Defender for Identity. This post will refer to it using the new name but the exam may contain references to the older name. For any topics referencing Azure ATP, read as Microsoft Defender for Identity.
This post will cover the following exam topics listed under the “Implement an Enterprise Hybrid Threat Protection Solution” section:
- Plan an Azure Advanced Threat Protection (ATP) solution
- Install and configure Azure ATP
Plan an Azure Advanced Threat Protection (ATP) Solution
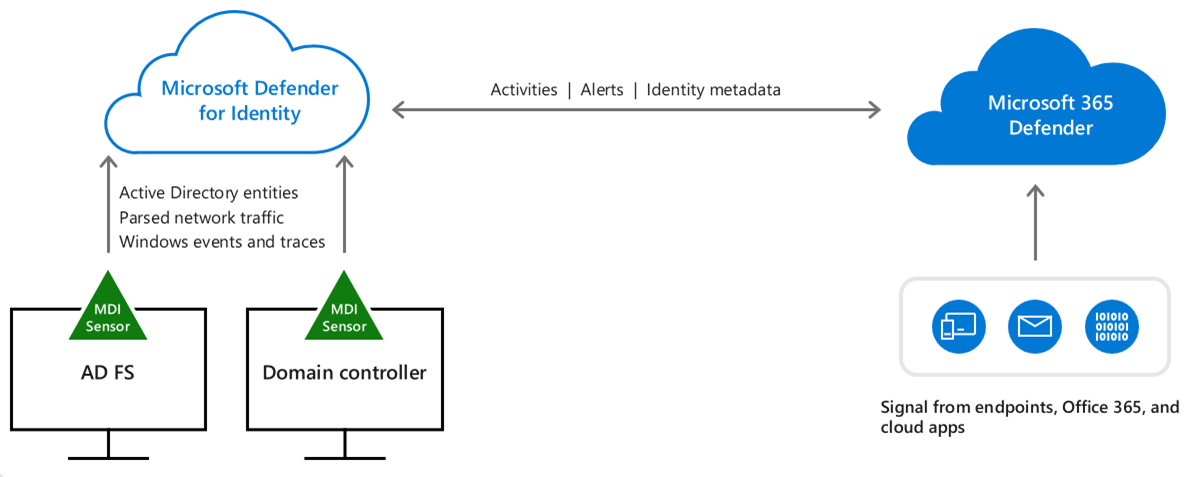
Microsoft Defender for Identity (MDI) is a cloud based solution which enables the advanced monitoring, investigation and threat protection functionality available through Azure, to apply within your on-premises Active Directory implementation. It achieves this by installing “Sensors”, which are essentially Microsoft Defender agents on your on-premises Domain Controllers (and optionally, ADFS servers). These sensors send logging and analytics data to the Microsoft Defender service where they are parsed and monitored for anomalous behaviour.
Data gathered by the MDI sensor contains:
- Local network traffic
- Windows Events
- RADIUS accounting information
- AD DS user data
Prerequisites
The following prerequisites are required to use MDI:
- Minimum EMS E5 or M365 E5 licensing for your tenancy
- Internet Access from Domain Controllers (and ADFS Servers is applicable)
- Minimum Windows Server 2008 R2 when using a standard service user account for sensors on Domain Controllers
- Minimum Windows Server 2012 when using a group managed service account for sensors on Domain Controllers
- Minimum Windows Server 2016 for sensors on ADFS servers
- Server requirements can be estimated using the Sizing Tool
For more specific prerequisites for your use case, check out this article.
Planning Sensors
When deploying sensors, it’s highly recommended to deploy to all Domain Controllers to get the optimum results from the service however it is possible to deploy only to a subset. Sensors can be deployed remotely via your usual deployment tools (SCCM etc.) using the silent installation option. To validate resources on the servers we can use the Sizing Tool mentioned above.
Install and Configure Azure ATP
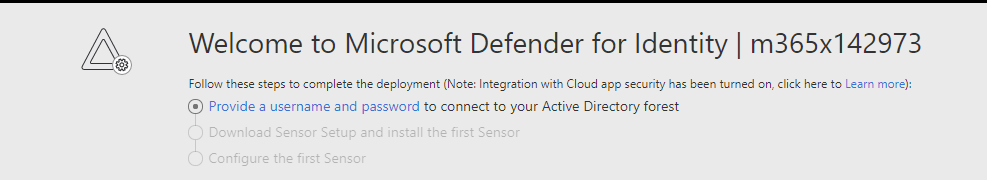
The first step in configuring MDI, is to enable the MDI instance for your tenant. The MDI portal is located at https://portal.atp.azure.com
Prepare the Defender for Identity Instance
Once the portal is enabled, our first step is to provide our domain credentials, We mentioned above that we can use a standalone user account or a group managed service account (gMSA), for our installation, we’ll use a gMSA as our Domain Controllers all meet the Windows Server 2012 or higher prerequisites. The process of creating a gMSA is not in scope for the exam but I will detail it in a future post. For now, more information can be found here.
If you are using a standard user account or if you have set up your gMSA, click on the “Provide a username and password” link in the MDI portal. and enter the account details.

Download and Install the First Sensor
Once the credentials are in place, the next step is to install our first sensor. Navigate to “Sensors” in the menu and download the Sensor setup files. Also take note of the Access key on the download page, we’ll need that in a minute.
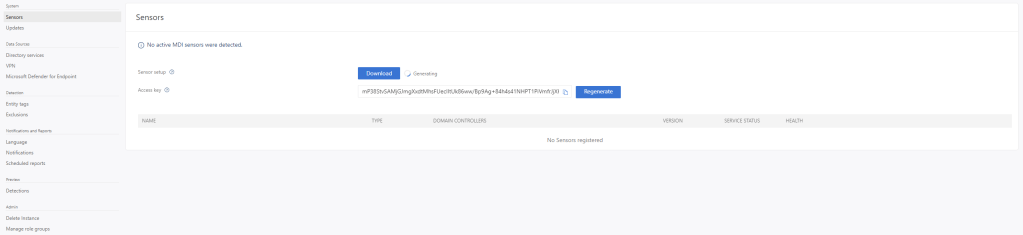
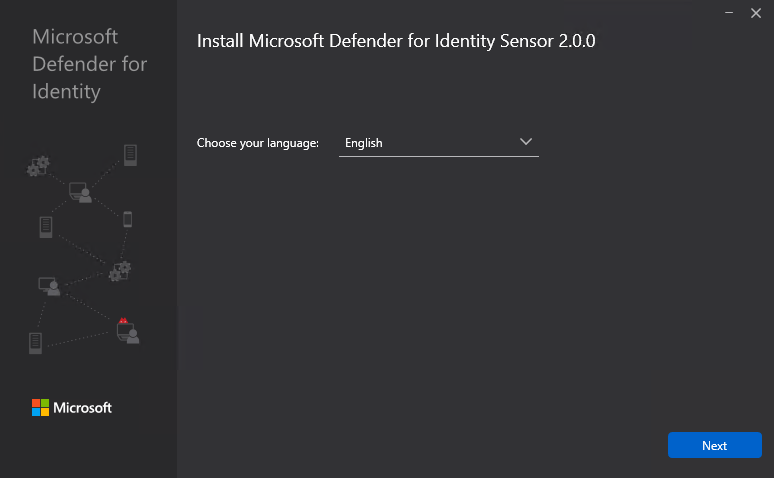
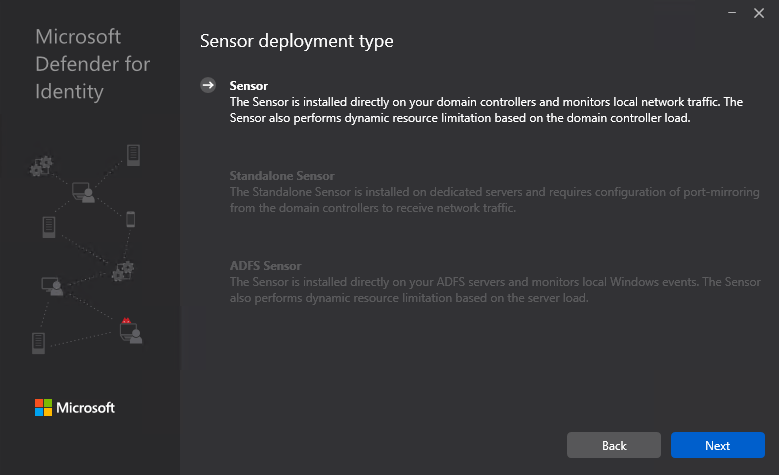
Once the download finished, copy the files to your target Domain Controller and extract the ZIP file to a folder. Run the Azure ATP Sensor Setup and step through the installation.
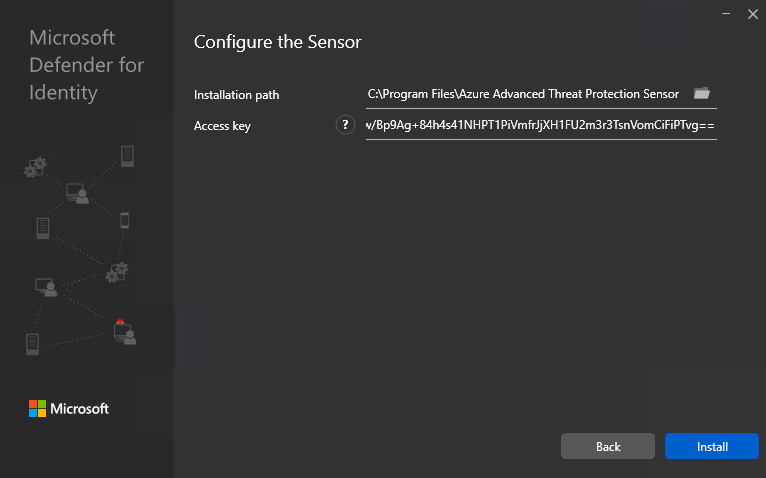
At the next page we paste in the Access key we noted from the portal earlier and hit install.
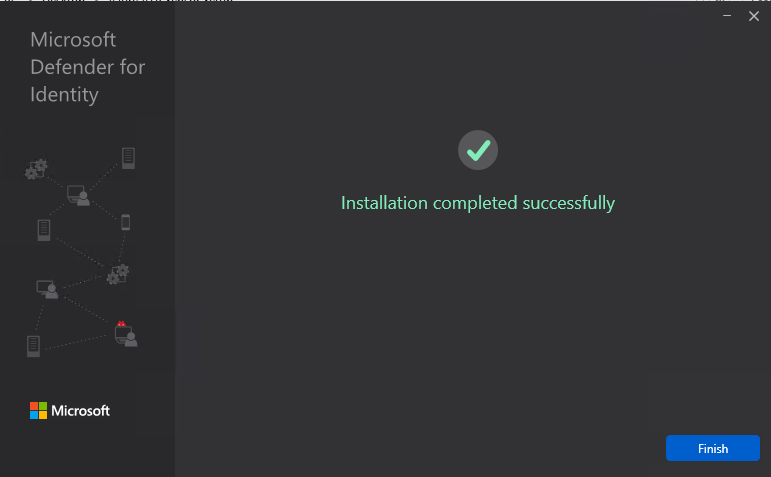
Grab a coffee while the installation finishes and when complete, we can finish the wizard.
Pop back to the MDI portal and we will see our DC registered and healthy.

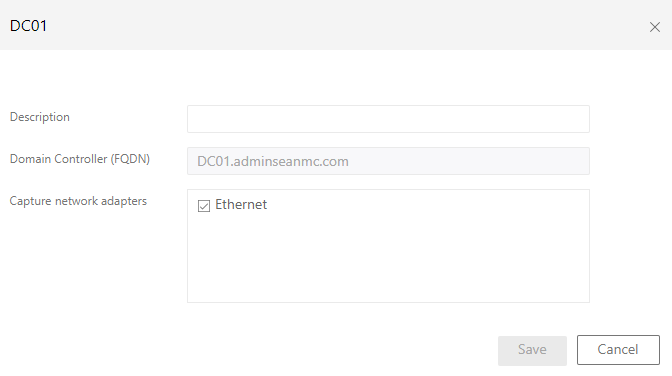
We can also click on the sensor to configure the monitored network adaptors, we may want to exclude things like a backup VLAN for instance.
Summary
That’s it, we’ve configured our MDI service, and installed our first sensor. Finish installing the rest of the sensor as needed and in the next post we will look at how we can use Defender for Identity to monitor our Domain Services environment.
Below are some handy links to the Microsoft documentation for MDI:
What is Microsoft Defender for Identity? | Microsoft Docs
Microsoft Defender for Identity architecture | Microsoft Docs
Planning your Microsoft Defender for Identity deployment | Microsoft Docs


Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Study Guide Series: Exam MS-500 – Monitor and Manage Azure ATP – Sean McAvinue