This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and Manage Microsoft Cloud App Security” section:
- Plan Cloud App Security implementation
- Configure Microsoft Cloud App Security
Plan Cloud App Security Implementation
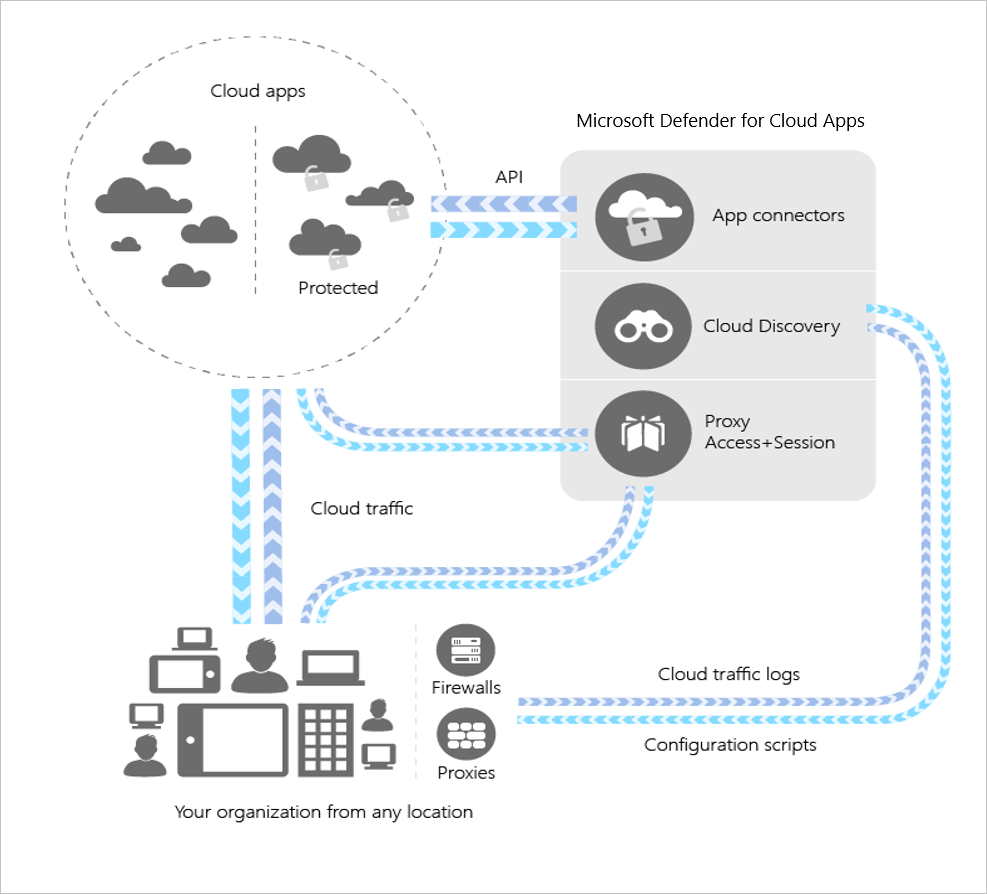
Microsoft Cloud App Security (MCAS) is a Cloud Access Security Broker (CASB). A CASB generally sits between your users and any cloud services they access, allowing for real-time monitoring, protection and management of how users interact with SaaS applications.
When we are planning a deployment of MCAS there are a number of aspects we need to be aware of:
- Cloud Discovery can allow us to monitor what shadow IT services our users are currently using
- Connected Apps allow us to integrate apps with MCAS to add protection functionality
- Conditional Access App and Session Control allows control and protect access to our connected apps
- Integration with Microsoft Cloud services allows us to extend native logging, reporting and incident management
- Protect sensitive files using Information Protection and Session Control
- Holistically monitor and manage security incidents across all cloud apps
- Automate processes by integrating with Power Automate
This is just a short list of some of the use cases that MCAS can assist with. In the posts on this topic, we will go through each of the aspects of MCAS to provide a detailed view of how it can help us manage and secure cloud application access.
Configure Microsoft Cloud App Security
To get started with configuration of MCAS, open up the MCAS portal by navigating to https://portal.cloudappsecurity.com. This will land us on the Dashboard section of the portal, where we get a top level view of the activity in the environment. In addition to this, the other sections we see available are:
Discover – This is where we can get a view of the entities (users, IP addresses, apps etc.) that have been discovered in our environment. We can configure Cloud discovery to ingest data from Microsoft Defender for Endpoint, log ingestion from network devices such as firewalls/proxies and native integration of supported proxies such as ZScaler.

Investigate – Here we can search through all of the information contained in MCAS to monitor activity in our environment. We can view activity, files, users, configuration and connected apps

Control – Here we can configure policies allowing us to monitor and alert on activity in our discovered and connected apps, adding automation if required. We can also configure session and app control policies to control how users interact with cloud apps.

Alerts – Here we can view and manage all of the alerts that have been risen in MCAS. We can view the details of each alert and monitor associated activities directly from the alert page.

Basic Configuration
To get started with the basic configuration of MCAS, select the cog icon in the top bar and click “settings”.
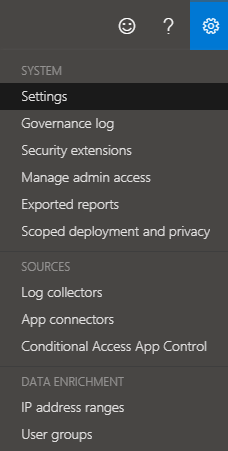
There are tonnes of settings we can configure here, below is a brief outline of each section:
- Organization Details – This is the basic details of our environment such as name, logo and domains
- Mail Settings – Customize the email notifications by adding a template or changing the source addresses
- Export Settings – Export the configuration of MCAS
- Automatic Sign Out – Here we can configure the timeout before a user/admin is logged out of the MCAS portal
- Activity Privacy – Modify permissions and hide specific activities from reports and dashboards
Cloud Discovery
- Score Metrics – Configure the priorities of the metrics used in generating app scores
- Snapshot Reports – Create and view snapshots from on-premises firewall/proxy etc.
- Continuous Reports – Configure continuous reports from log collectors
- Automatic Log upload – Configure automatic log upload and log collectors
- App Tags – Create and Modify tags to assign to apps
- Exclude Entities – Exclude users and IP addresses from Cloud discovery
- Microsoft Defender for Endpoint – Configure integration with Defender for Endpoint
- User Enrichment – Match user entities with profiles discovered from Azure AD
- Anonymization – Anonymize usernames / devices in reports and dashboards
- Delete Data – Delete all Cloud Discovery data
Threat Protection
- Microsoft Defender for Identity – Integrate with Defender for Identity
- Azure AD Identity Protection – Integrate with Azure AD Identity Protection
Information Protection
- Admin Quarantine – Configure a location and notification for when files are moved to quarantine by MCAS
- Azure Information Protection – Configure Azure Information Protection integration and grant MCAS permission to inspect protected files
- Azure Security – Integrate with associated Azure Subscriptions where Azure Security Center is enabled
- Files – Enable / Disable MCAS file monitoring
Conditional Access App Control
- Default Behaviour – Define if access should be allowed in the event of an outage or where a policy cannot be enforced
- User Monitoring – Configure or disable notification to users that MCAS is monitoring activity
- Device Identification – Configure how different device types are identified by MCAS such as using Microsoft Endpoint Manager and Azure AD
- App onboarding/maintenance – Add users to allow them to onboard apps to MCAS
Summary
There is a lot to take in initially with MCAS. Over the next few posts we will be diving deep into the configuration of different aspects so don’t worry too much if there seems to be a lot here. I recommend exploring the MCAS portal to check out some of the features and settings before we start configuration in the next post. There is also a lot of information available at the below links:
What is Cloud App Security? | Microsoft Docs
Deploy Cloud App Security | Microsoft Docs
Set up your organization’s settings in Cloud App Security | Microsoft Docs
Set up your organization’s settings in Cloud App Security | Microsoft Docs


Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue