This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and Manage Microsoft Cloud App Security” section:
- Manage cloud app discovery
- Manage entries in the Cloud app catalog
In the previous post we looked at some of the basics of Microsoft Cloud App Security (MCAS), we will continue here by getting into some of the configuration of the different aspects of MCAS.
Manage Cloud App Discovery
Cloud Discovery allows us to analyse traffic logs from various sources using the MCAS app catalog to classify traffic by app, giving insight into shadow IT usage in the organization. Logs can come in via various sources:
- Snapshot Reports allow us to manually upload firewall and proxy logs to get a point-in-time report
- Continuous Reports allow us to automate the upload of logs using one of the following methods:
- Integration with Microsoft Defender for Endpoint
- Installing a Log Collector to ingest logs using Syslog of FTP and ingest into MCAS
- Direct Integration with Zscaler, iboss, Corrata or Menlo Secure Web Gateways
- Direct log upload using the Cloud Discovery API
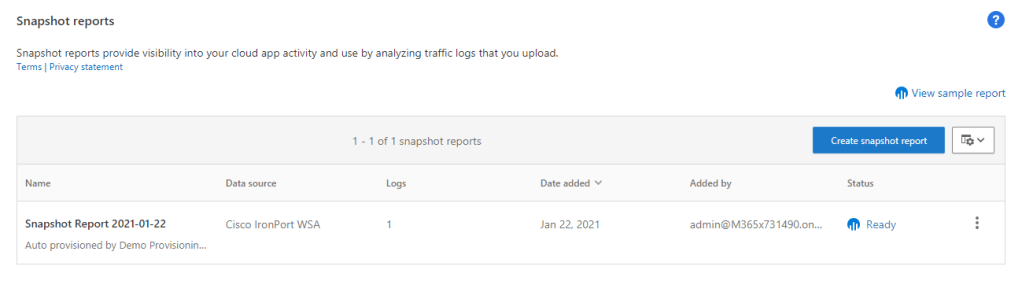
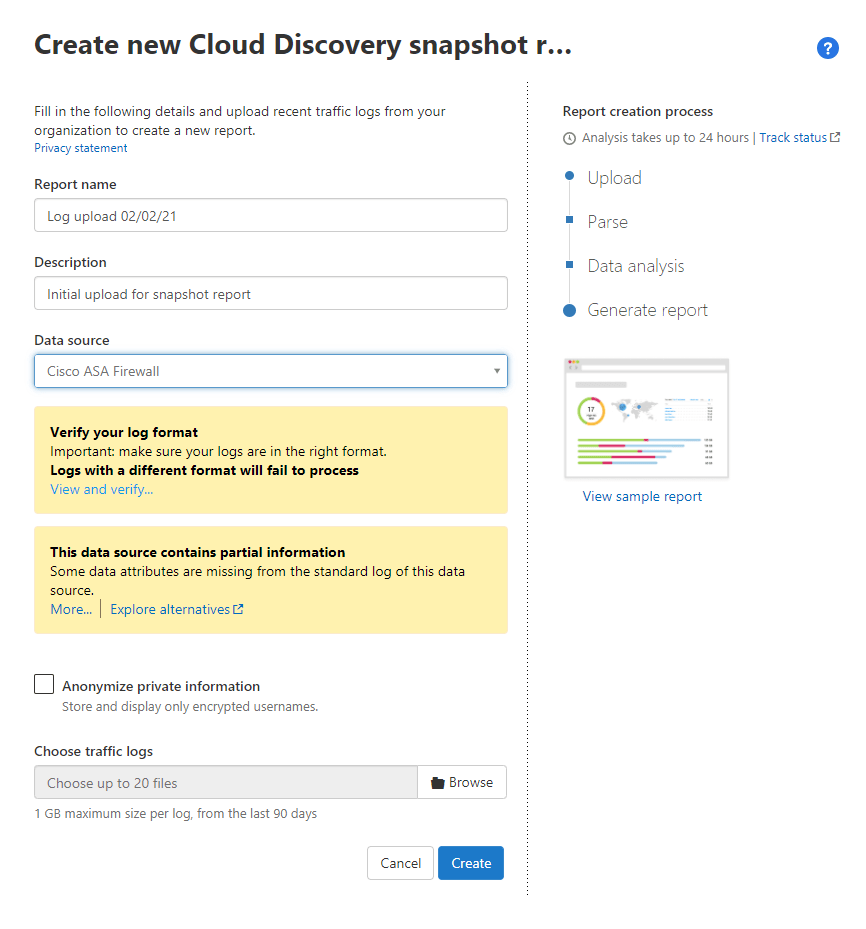
Uploading Snapshot Reports
To configure log uploads for snapshot reports, open the settings page of the MCAS portal and select the “Snapshot reports” section. From here we can use the “Create snapshot reports” button to upload our logs.
Integrate with Microsoft Defender for Endpoint
To configure Microsoft Defender for Endpoint Integration, we first need to enable it in the Microsoft Defender settings, under “Advanced Features” as per the below screenshot.
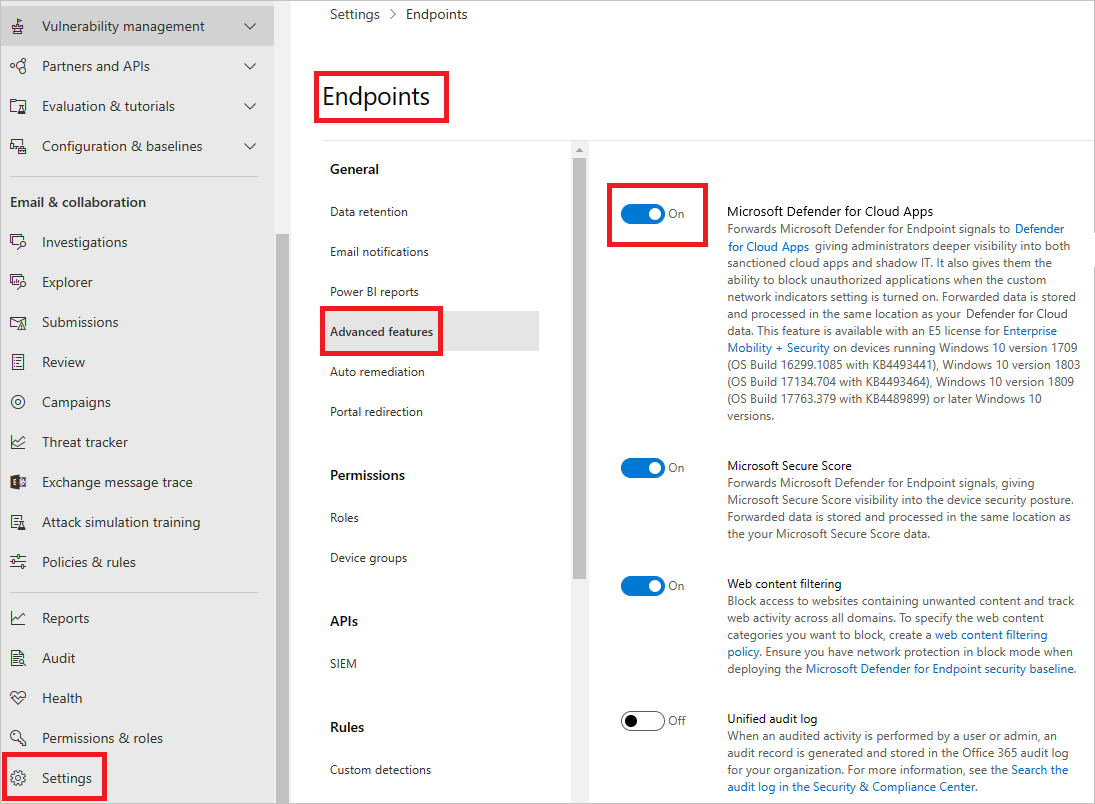
Then enable it in MCAS settings under the “Microsoft Defender for Endpoint” section.

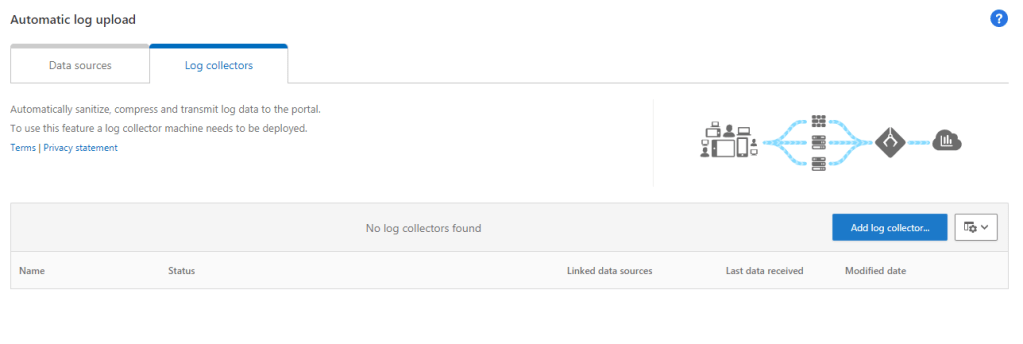
Configure Automatic Log Upload and Log Collectors
Automatic upload and log collectors can be configured from the “Automatic log upload” section of the settings page. To deploy the log collector, download it from the Microsoft site below:
Configure automatic log upload for continuous reports in Cloud App Security | Microsoft Docs
Then configure via the setting page.
Using Cloud Discovery
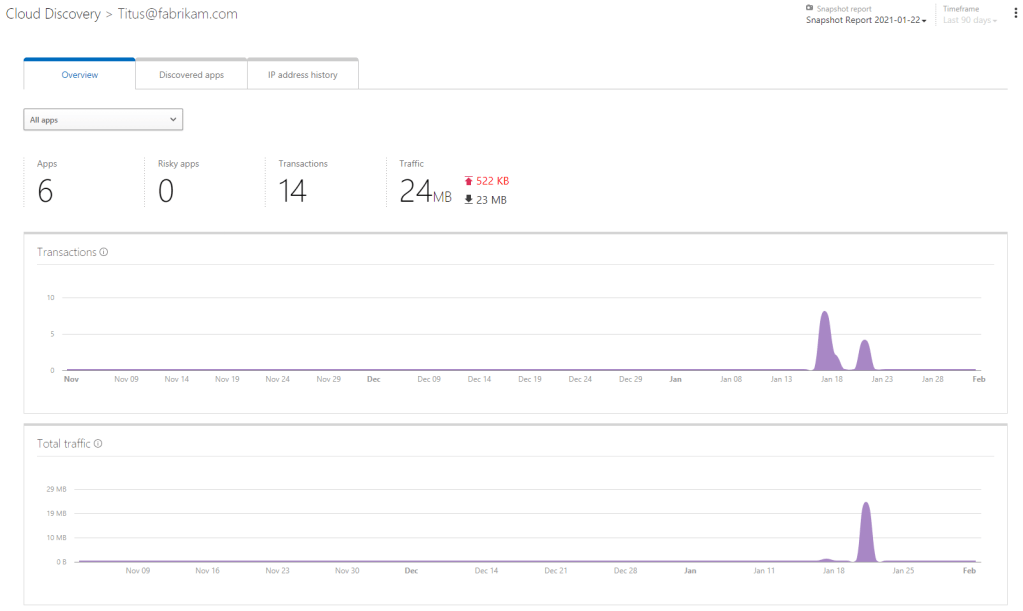
To get started with Cloud Discovery, open up the MCAS portal and expand the “Discover” section. Here we will see a list of tabs we can view. We looked at these pages briefly in the previous post but let go a bit deeper now.
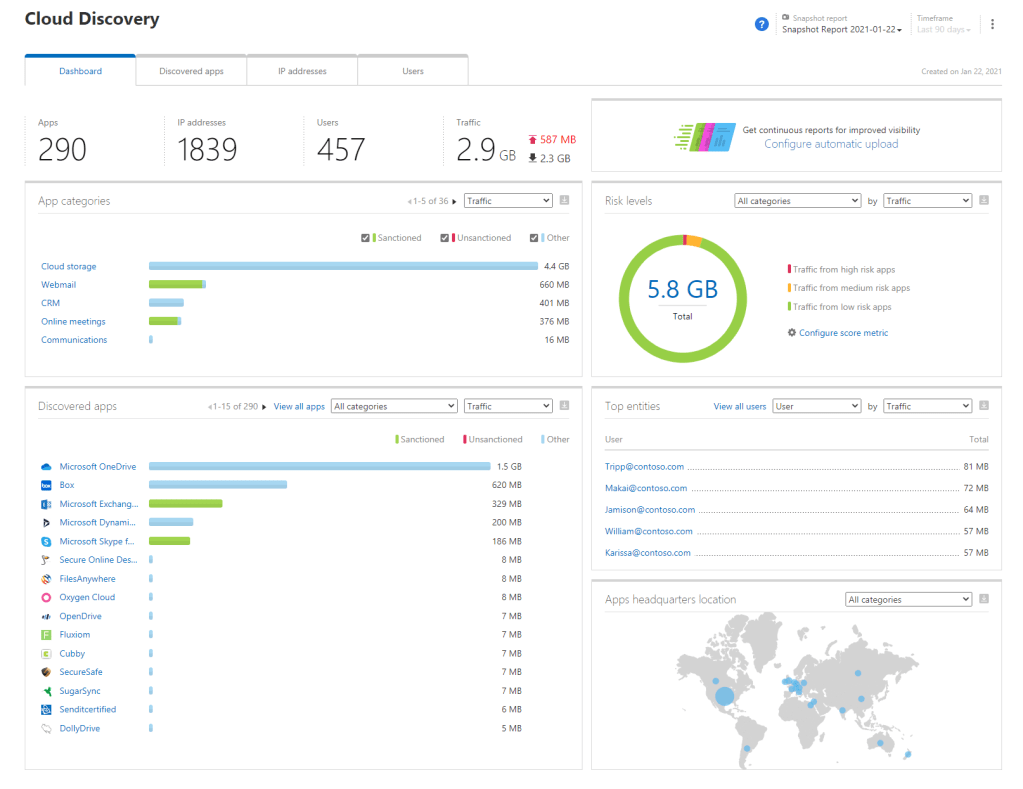
Cloud Discovery Dashboard
On the Cloud Discovery Dashboard, we will see the high level statistics of our Cloud Discovery. We will see the metrics of entities such as apps, IP Addresses, Users and Traffic. We will also see a high-level breakdown of the app discovery and any associated risks etc. At the top right of the page we can change which report we are looking at. Clicking on any of the items on this page will bring us to the relevent tab for that item, for instance, clicking on an app will bring us to the “Discovered Apps” tab.
Discovered Apps
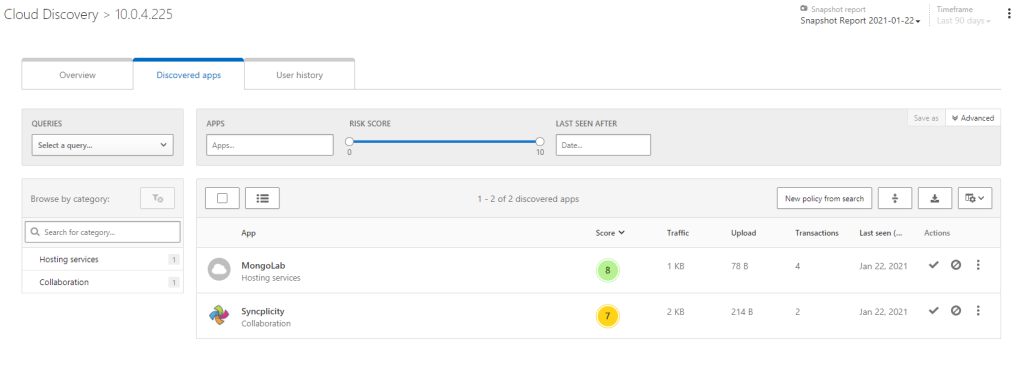
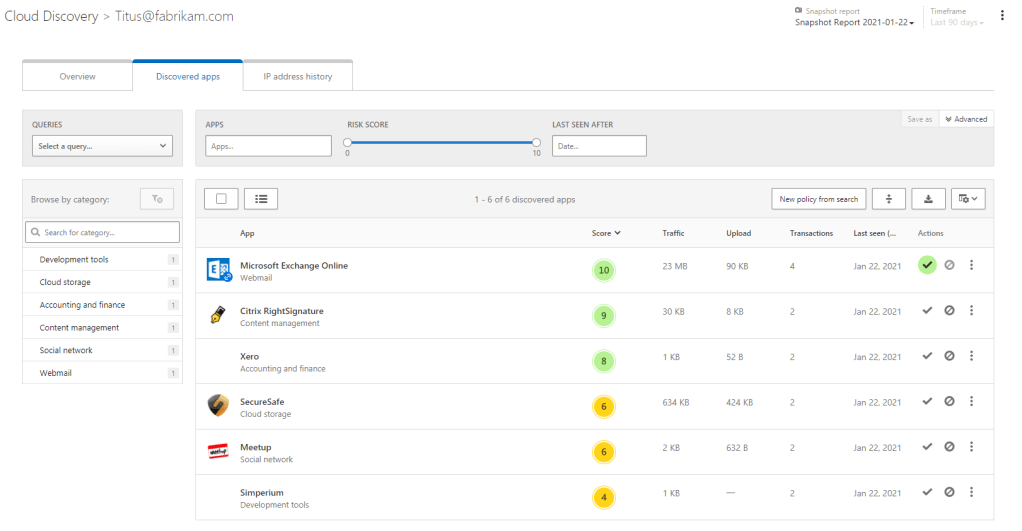
The “Discovered Apps” tab shows us the apps that have been detected in the report and details of each. Each app entry will show the app name, category, risk score, traffic size, upload size, abount of transactions and users and last time accessed. We can click on any app to see a breakdown of the scores associated with the app. We also have a lot of filters we can work with to identify specific apps or specific risk levels.
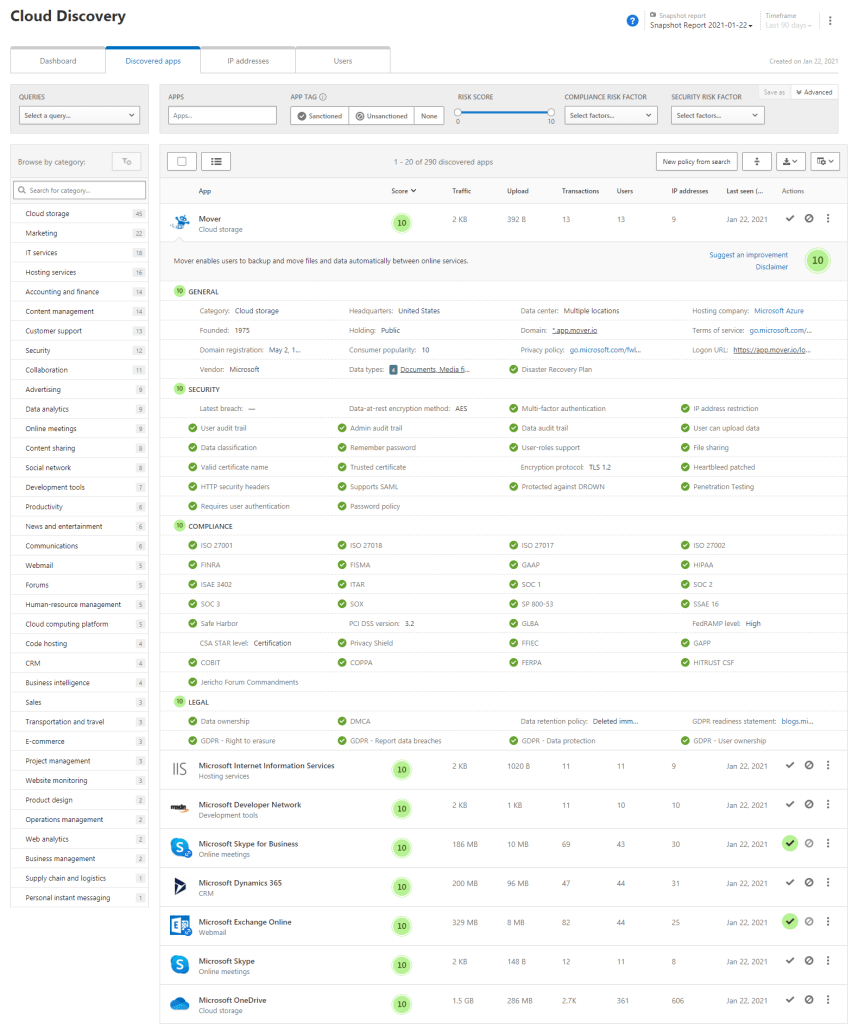
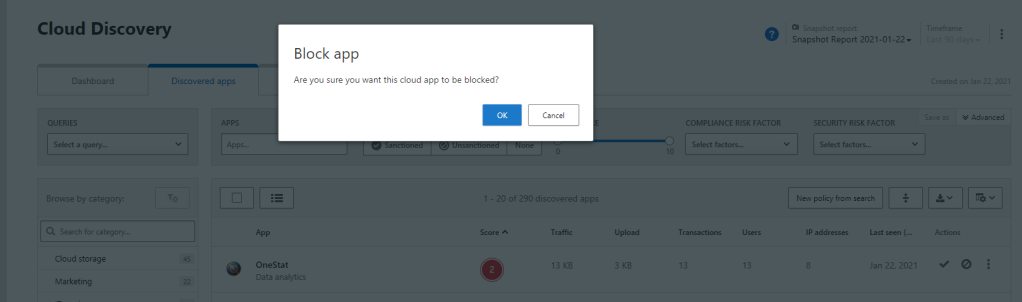
If we have Microsoft Defender for Endpoint or another directly integrated app such as Zscaler, we can mark an app as “unsanctioned” which will block all access to the app through the platform we have integrated.
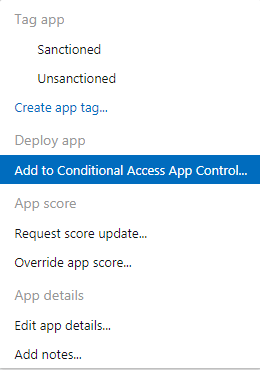
If we have an app integrated with our Azure AD directory, we can configure the app for Conditional Access App Control (We’ll detail this further in a future post).
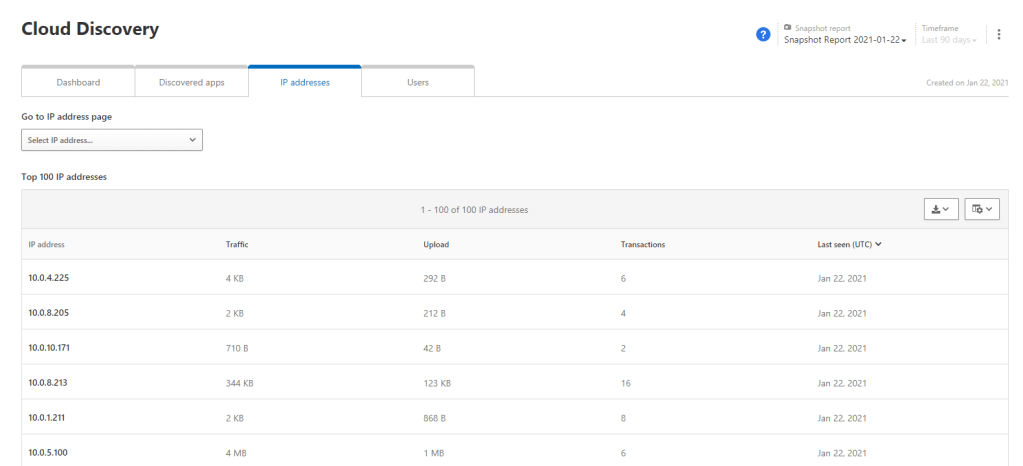
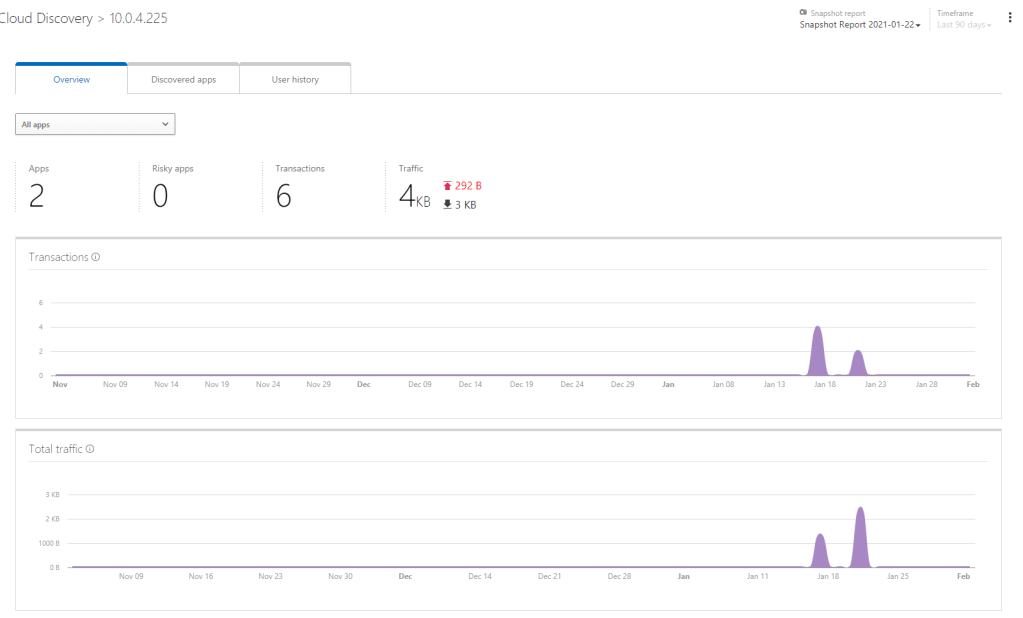
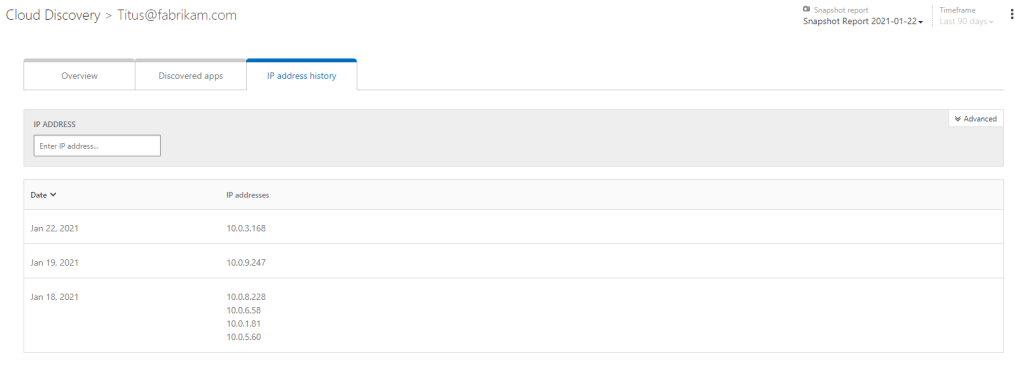
IP Addresses
On the IP Addresses tab we get a breakdown of the IP Addresses in our uploaded logs, we can then click on a specific address to get an overview of the activity coming from that source.
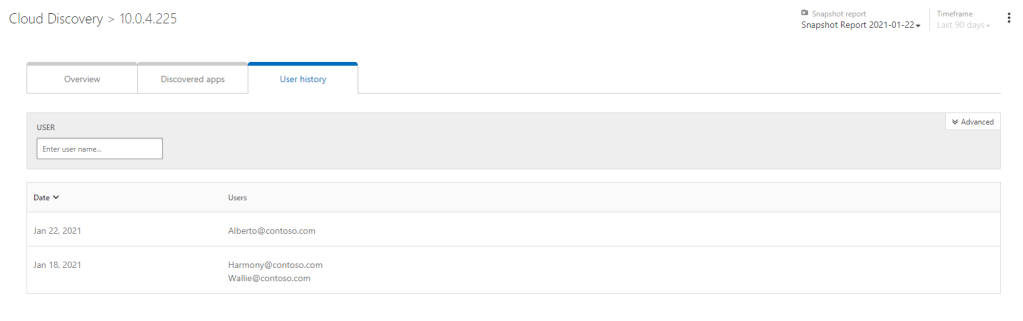
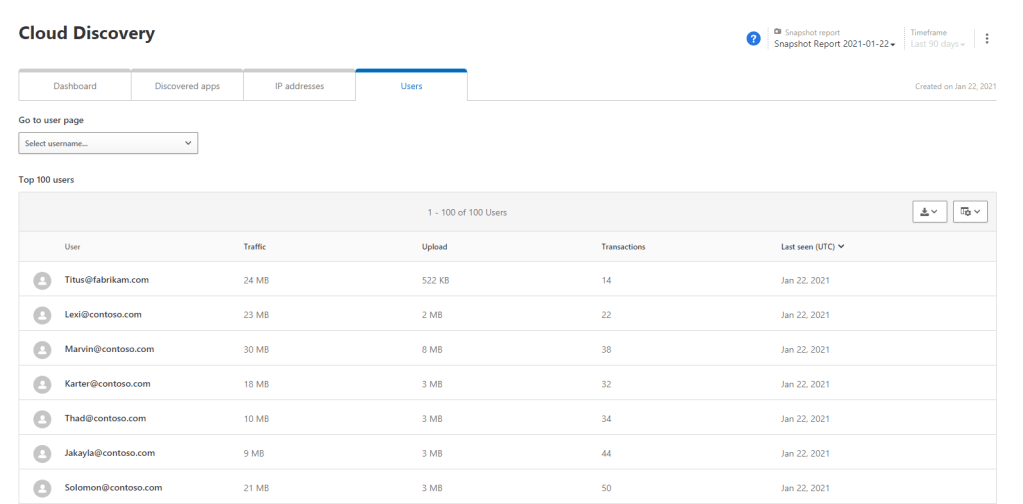
Users
The users tab gives us a similar breakdown as the IP Addresses tab but breaks down by user.
Manage Entries in the Cloud App Catalog
As we’ve seen already, the Cloud App Catalog from Microsoft contains a huge number of apps that our users may connect to. This catalog is used to define the apps when we are using Cloud Discovery.
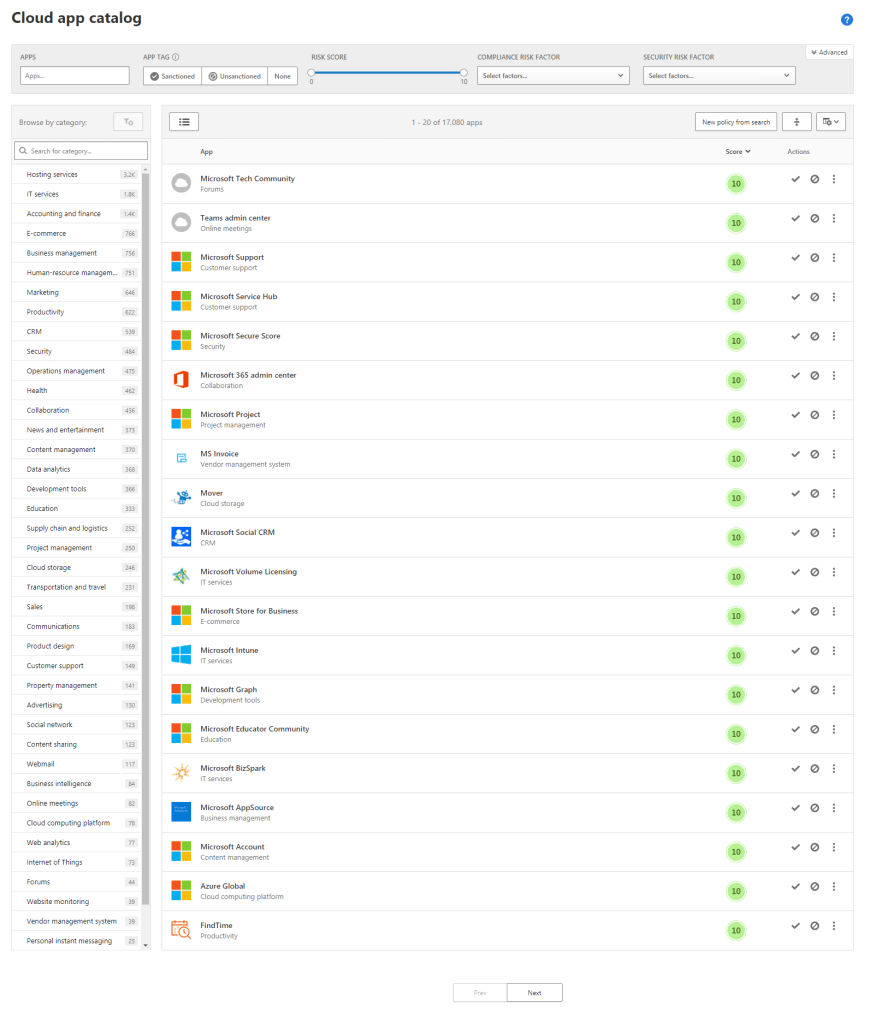
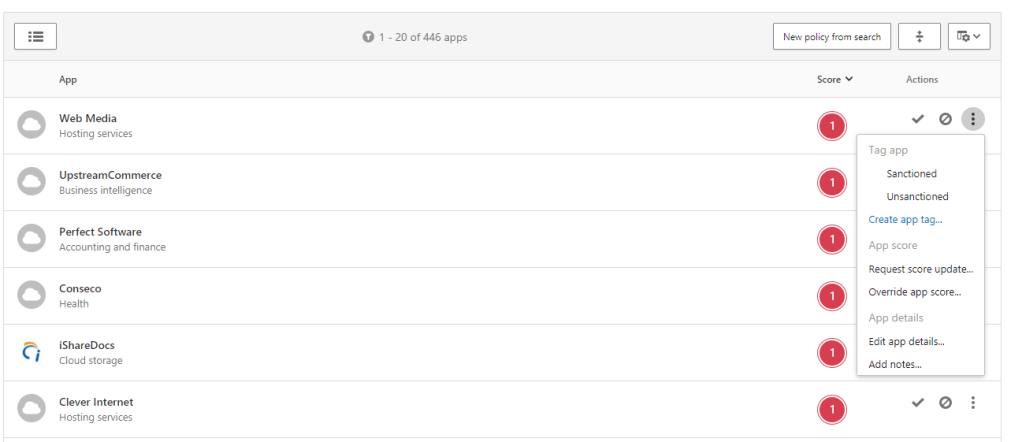
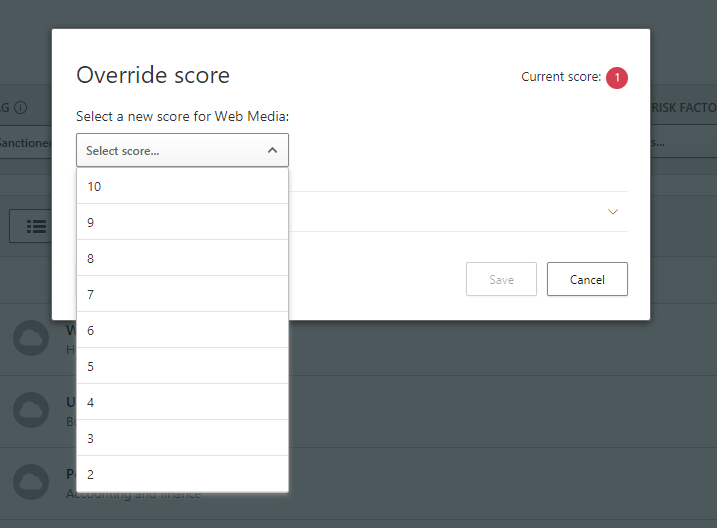
We can perform the actions discussed above such as Sanctioning and Unsanctioning the apps directly on the catlog itself. We can also add notes and details to the apps if we like and even override the Microsoft provided scores.
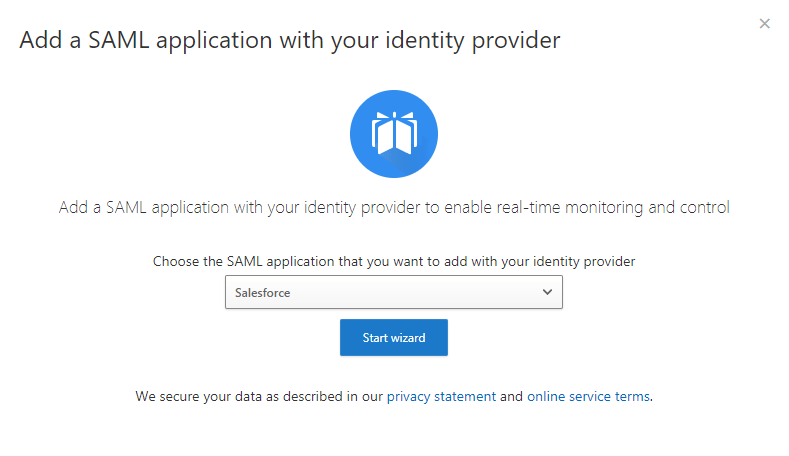
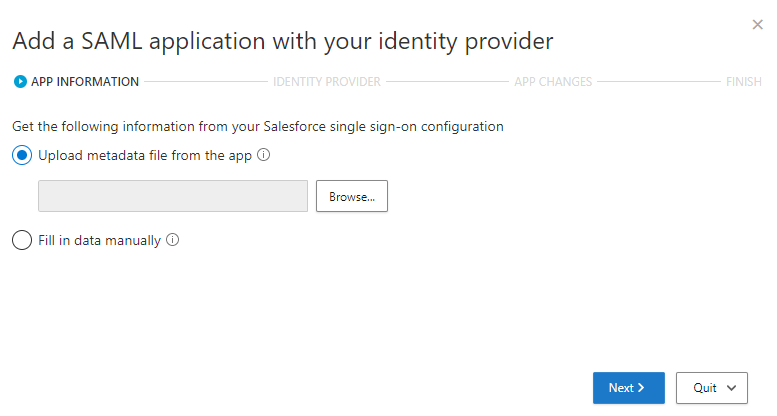
If we choose to add an app to Conditional Access App Control, we get a nice wizard with steps to show us how to integrate the app with Azure AD.
The App Catalog is always expanding and provides the core of the Cloud discovery function. It’s worth going through what is available and viewing the details and breakdown of the different standards that each app is rated against.
Summary
In this post we went a bit deeper into MCAS and looked specifically at Cloud Discovery and how to get started with it as well as touching on some of the other concepts such as Conditional Access App Control which we will look at in a separate post. For now, there’s a lot more information available on cloud discovery at the below links:
Discover and manage Shadow IT | Microsoft Docs
Deploy Cloud Discovery | Microsoft Docs
Integrate Microsoft Defender for Endpoint with Cloud App Security | Microsoft Docs
Integrate Cloud App Security with Zscaler | Microsoft Docs
Roll out continuous reports for Cloud App Security using a Docker on Windows | Microsoft Docs


Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue