This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and Manage Microsoft Cloud App Security” section:
- Manage apps in Cloud App Security
- Manage Microsoft Cloud App Security
In the previous post we looked a bit deeper into the Cloud Discovery functionality of MCAS, looking at how we ingest and interoperate data using the available dashboards and reports. We will now move on to how we can manage and configure apps to work with MCAS and the benefits we see through integration.
Manage Apps in Cloud Apps Security
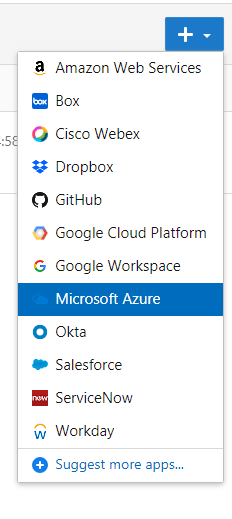
Through MCAS, we have the ability to integrate a list of supported apps directly. This allows us to manage apps directly through Cloud app security using app connectors and leverage the APIs of the specific app we are connecting. The list of apps we can integrate using app connectors is detailed here. For this example we will use Microsoft Azure.
To get started, open up the “Connected Apps” page under the “Investigate” section of the MCAS portal. From here we can select the app we want to add, each app will have it’s own steps to configure the connector.
For Azure, click on “Connect Microsoft Azure” to connect the app and MCAS will begin pulling data immediately.
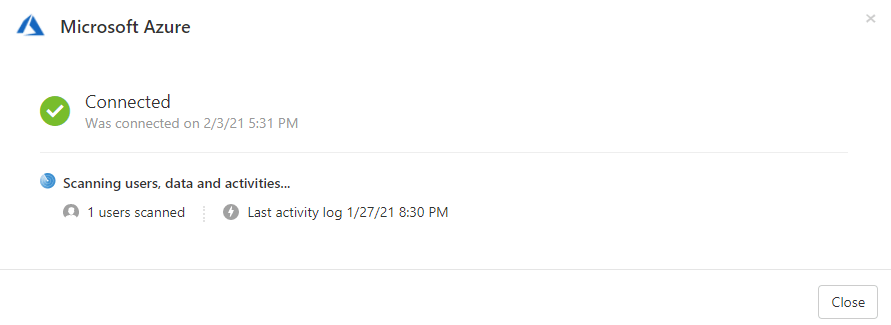
Once the connection is established we can see and manage policies for the connected apps from MCAS as we would with apps connected through other means. The below table lists the functionality available for each app.
AWS | Box | Dropbox | GitHub | GCP | Google Workspace | Office 365 | Okta | Service Now | Salesforce | Webex | Workday | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| List accounts | ✔ | ✔ | ✔ | ✔ | Subject Google Workspace connection | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| List groups | ✔ | ✔ | ✔ | ✔ | Subject Google Workspace connection | ✔ | ✔ | ✔ | ✔ | ✔ | Not supported by provider | |
| List privileges | ✔ | ✔ | ✔ | Subject Google Workspace connection | ✔ | ✔ | Not supported by provider | ✔ | ✔ | ✔ | Not supported by provider | |
| User governance | ✔ | Coming soon | Subject Google Workspace connection | ✔ | ✔ | ✔ | Not supported by provider | |||||
| Log on activity | ✔ | ✔ | ✔ | Subject Google Workspace connection | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| User activity | Not applicable | ✔ | ✔ | ✔ | ✔ | ✔ – requires Google Business or Enterprise | ✔ | ✔ | Partial | Supported with Salesforce Shield | ✔ | ✔ |
| Administrative activity | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | Partial | ✔ | ✔ | Not supported by provider |
| DLP – Periodic scan | ✔ | ✔ | Not applicable | ✔ | ✔ | Not applicable | ✔ | ✔ | ✔ | Not supported by provider | ||
| DLP – Near real-time scan | ✔ | Not applicable | ✔ – requires Google Business Enterprise | ✔ | Not applicable | ✔ | Not supported by provider | |||||
| Sharing control | ✔ | ✔ | ✔ | Not applicable | ✔ | ✔ | Not applicable | Not applicable | ✔ | Not supported by provider | ||
| File governance | ✔ | ✔ | ✔ | Not applicable | ✔ | ✔ | Not applicable | ✔ | Not supported by provider | |||
| View app permissions | Not applicable | Not supported by provider | Coming soon | ✔ | Not applicable | ✔ | ✔ | Not applicable | ✔ | Not applicable | Not applicable | |
| Revoke app permissions | Not applicable | Not supported by provider | Coming soon | Not applicable | ✔ | ✔ | Not applicable | ✔ | Not applicable | Not applicable | ||
| Apply Azure Information Protection labels | Not applicable | ✔ | Not applicable | ✔ | ✔ | Not applicable | Not applicable | Not applicable |
Manage Microsoft Cloud App Security
To be honest this section title is very generic, I have to assume it relates to managing access to MCAS as the other functionality and basic set up is covered elsewhere.
There are a few layers to admin access in MCAS. There are roles which are inherited from Azure AD and there are directly assigned MCAS roles. To start, the following Azure AD roles (from this page) will provide some level of access to MCAS:
- Global administrator and Security administrator: Administrators with Full access have full permissions in Cloud App Security. They can add admins, add policies and settings, upload logs and perform governance actions, access and manage SIEM agents.
- Compliance administrator: Has read-only permissions and can manage alerts. Cannot access Security recommendations for cloud platforms. Can create and modify file policies, allow file governance actions, and view all the built-in reports under Data Management.
- Compliance data administrator: Has read-only permissions, can create and modify file policies, allow file governance actions, and view all discovery reports. Cannot access Security recommendations for cloud platforms.
- Security operator and Security reader: Have read-only permissions and can manage alerts. These admins are restricted from doing the following actions:
- Create policies or edit and change existing ones
- Performing any governance actions
- Uploading discovery logs
- Banning or approving third-party apps
- Accessing and viewing the IP address range settings page
- Accessing and viewing any system settings pages
- Accessing and viewing the Discovery settings
- Accessing and viewing the App connectors page
- Accessing and viewing the Governance log
- Accessing and viewing the Manage snapshot reports page
- Accessing and viewing SIEM agents
- Global reader: Has full read-only access to all aspects of Cloud App Security. Cannot change any settings or take any actions.
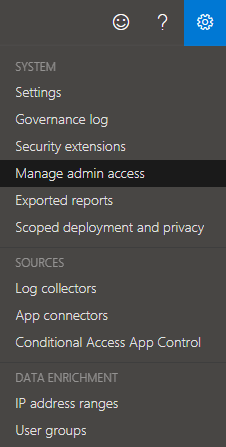
We can also use the built in roles detailed here to provide more granular access. to assign these roles, open up “Manage admin access” under the settings dropdown at the top of the page.
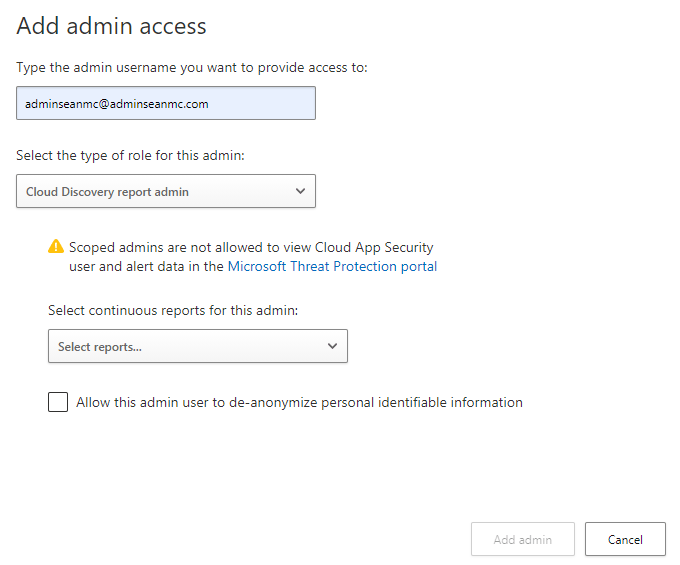
From here, we can add our users and select the role to assign from the provided list:

With some of the roles we can grant granular permissions such as to specific reports.
Summary
In this post we’ve gone another level into the massive array of functionality available in MCAS. In the next post we will continue by looking at OAUTH apps and policies and see some of the cool controls we can put in place. For now, more information on these topics is available at the below links.
Connect apps to get visibility and control | Microsoft Docs
Connect Azure to Cloud App Security | Microsoft Docs
Manage admin access to the Cloud App Security portal | Microsoft Docs


Pingback: Study Guide Series: Exam MS-500 – Implement and Manage Microsoft Cloud App Security (Part 4) – Sean McAvinue
Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue