This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and Manage Microsoft Cloud App Security” section:
- Configure Cloud App Security policies and templates (Continued..)
- Review, interpret and respond to Cloud App Security alerts, reports, dashboards and logs
in the previous post, we looked at configuring connected and Oauth apps and started looking at how to configure MCAS policies. Here, we will pick up where we left off to close out our focus on MCAS.
Configure Cloud App Security Policies and Templates
So far, in the last post we configured out Conditional Access App Control policy to make our app available for MCAS session and access policies. We will pick up from there by creating our first policy.
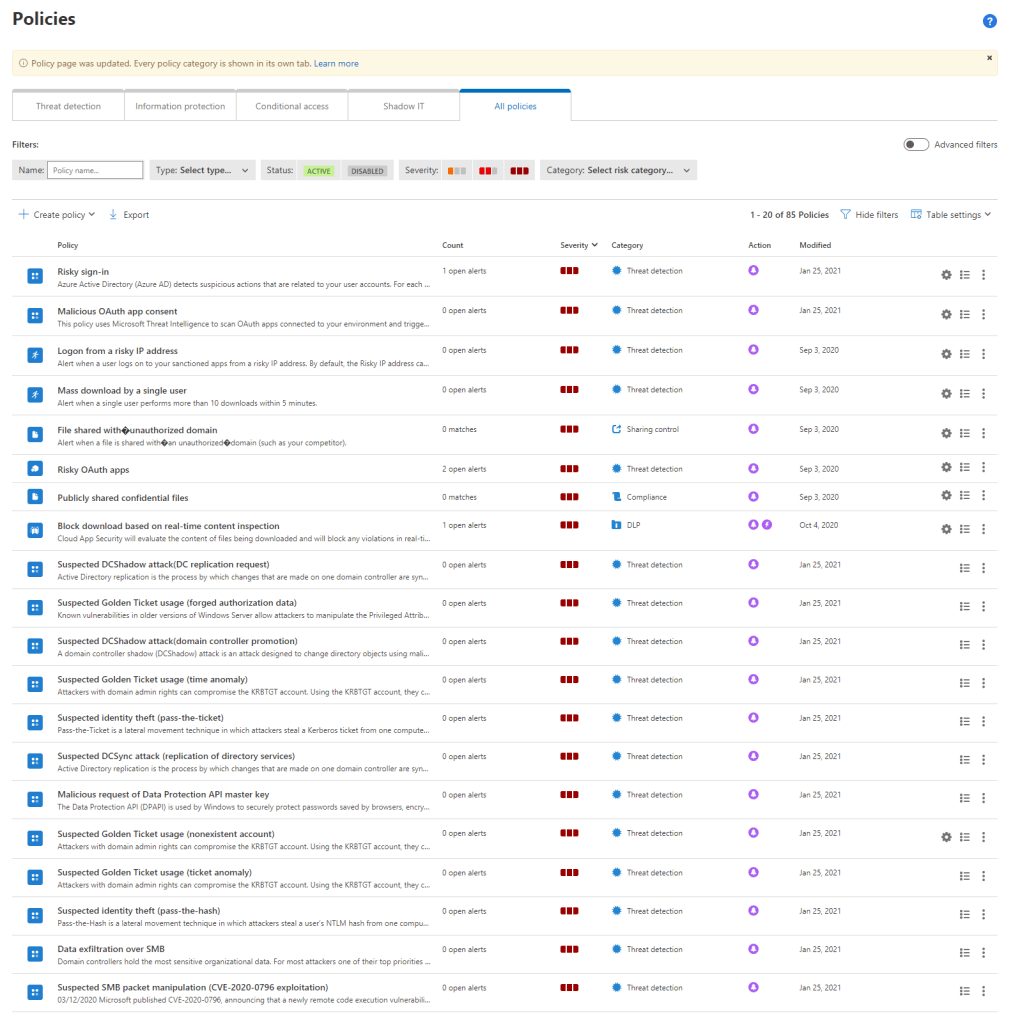
To create a policy, open the “Policies” page in the “Control” section of the MCAS portal. Here we can create policies such as activity and Cloud Discovery which we can use to alert on behaviour in our environment. We can also create Access and Session policies to control how our users access the cloud app and what they can do in that session. Under the templates section we can view and create policies based on predefined templates to get us started, or we can create a policy from screatch in the “Policies” section.
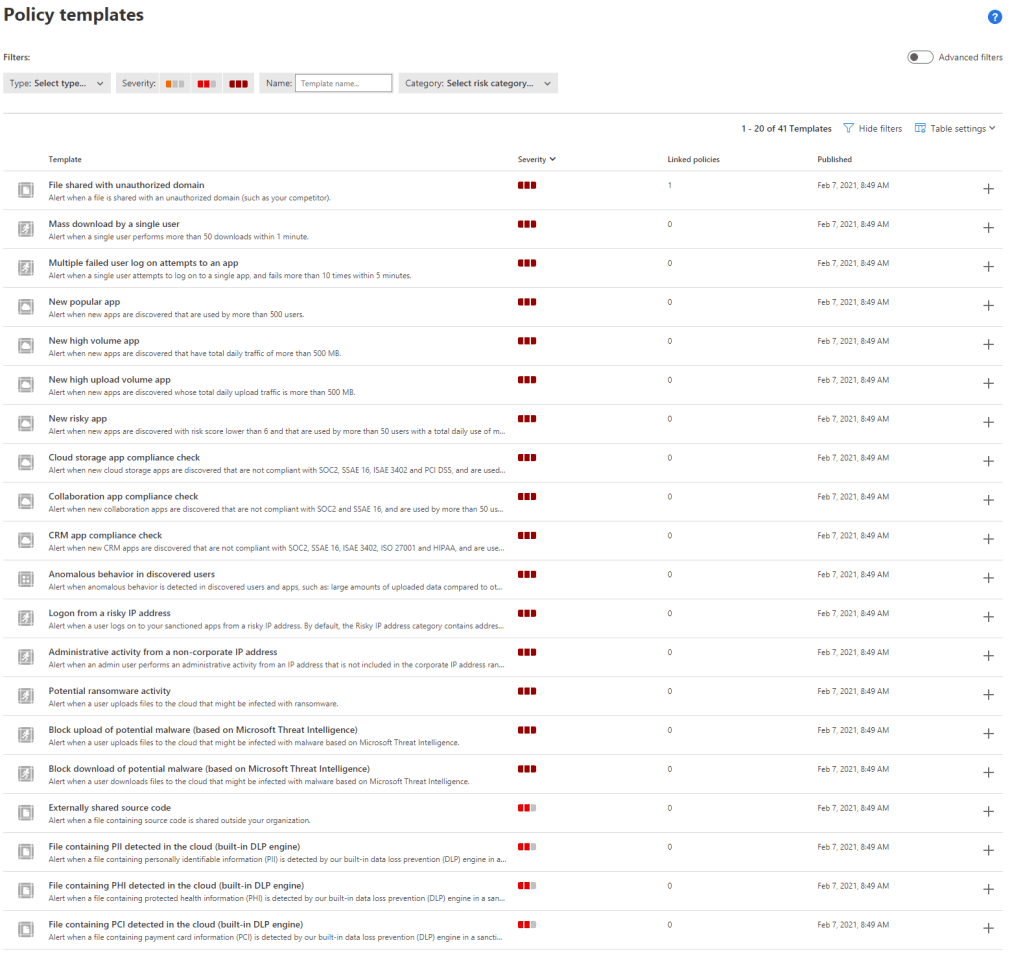
To get started, let’s select the session control policy template “Block upload based on real-time content inspection” from the templates page and click the “+” icon to create a new policy from this template.
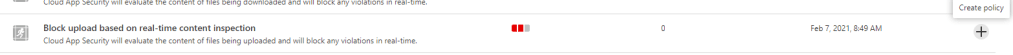
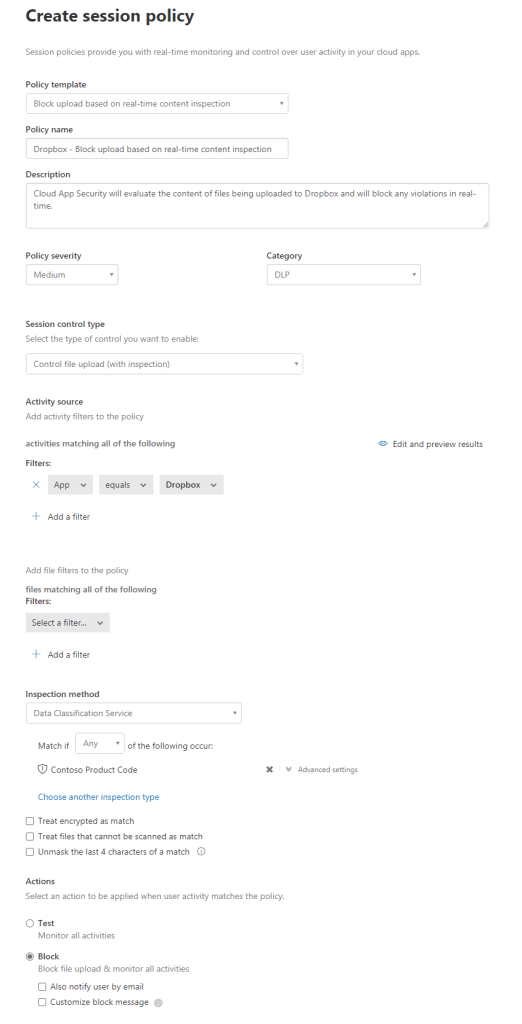
On the “Create session policy” page, we need to configure our policy to achieve the protection we require. Note that depending on the policy and settings we use, the options available to us can vary, for this policy, we want to block files with sensitive data (based on our previously set up sensitive information type for product code) from being uploaded to Dropbox. We’ll configure the following settings here to achieve this:
- Policy Template – The template we are using to base the policy on
- Policy Name – A name for the policy
- Description – A description for the policy
- Policy severity – The associated severity with matches for this policy
- Category – The type of policy this is
- Session control type – What are we controlling
- Activity source – Rules to match the activity the user is performing to trigger this policy
- Inspection method – The type of Content Inspection we are using
- Inspection Type – Content Type we are looking for
- Actions – What to do when the policy finds a match
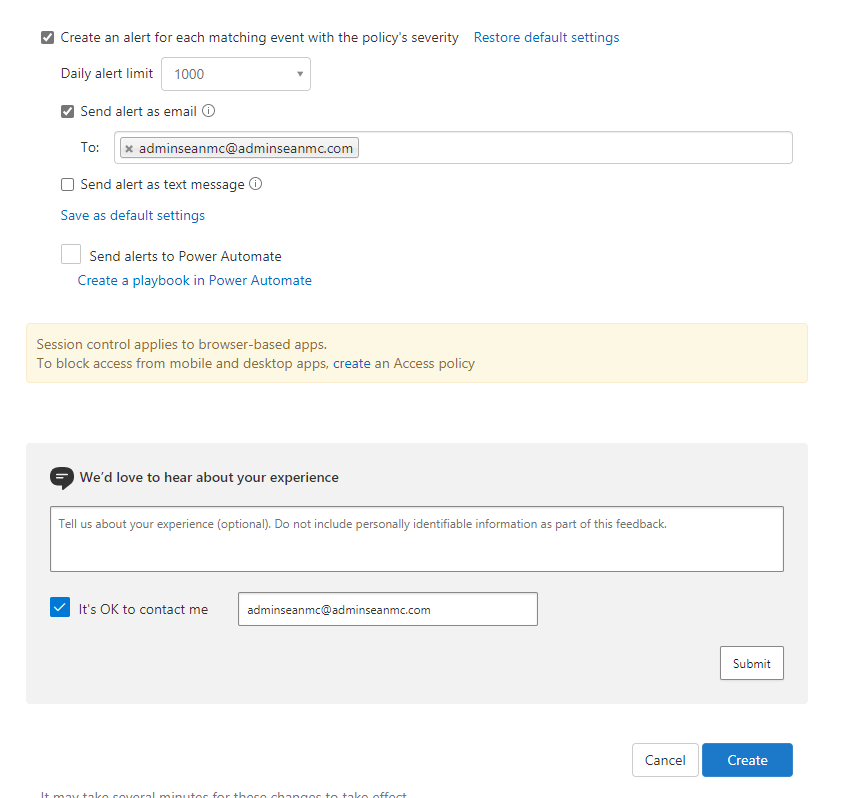
- Create an alert for each matching event with the policy’s severity – Should this policy trigger an alert in MCAS
- Daily alert limit – limit to the amount of alerts this policy will trigger per day
- Send alert as email – Address to send the alert to
| Setting Name | Setting Value |
| Policy Template | Block upload based on real-time content inspection |
| Policy Name | Dropbox – Block upload based on real-time content inspection |
| Description | Cloud App Security will evaluate the content of files being uploaded to Dropbox and will block any violations in real-time. |
| Policy Severity | Medium |
| Category | DLP |
| Session Control Type | Control file upload (with inspection) |
| Activity Source | App -equals Dropbox |
| Inspection Method | Data Classification Service |
| Match if | Any of the following occur |
| Inspection Type | Contoso Product Code |
| Actions | Block |
| Create an alert for each matching event with the policy’s severity | Yes |
| Daily alert limit | 1000 |
| Send alert as email | Yes |
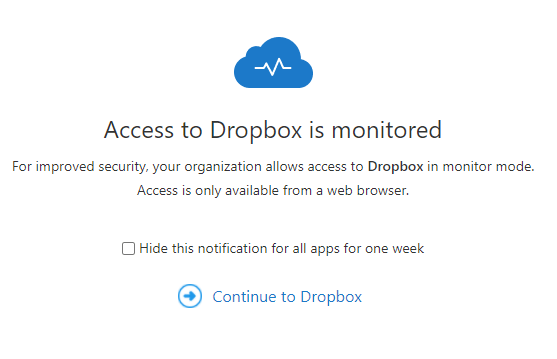
With the policy created, we can now test it. We can navigate to Dropbox and sign in with SSO, with Conditional Access App Control, we are routed via the MCAS proxy and if we haven’t turned off the notification, will see the standard notification:
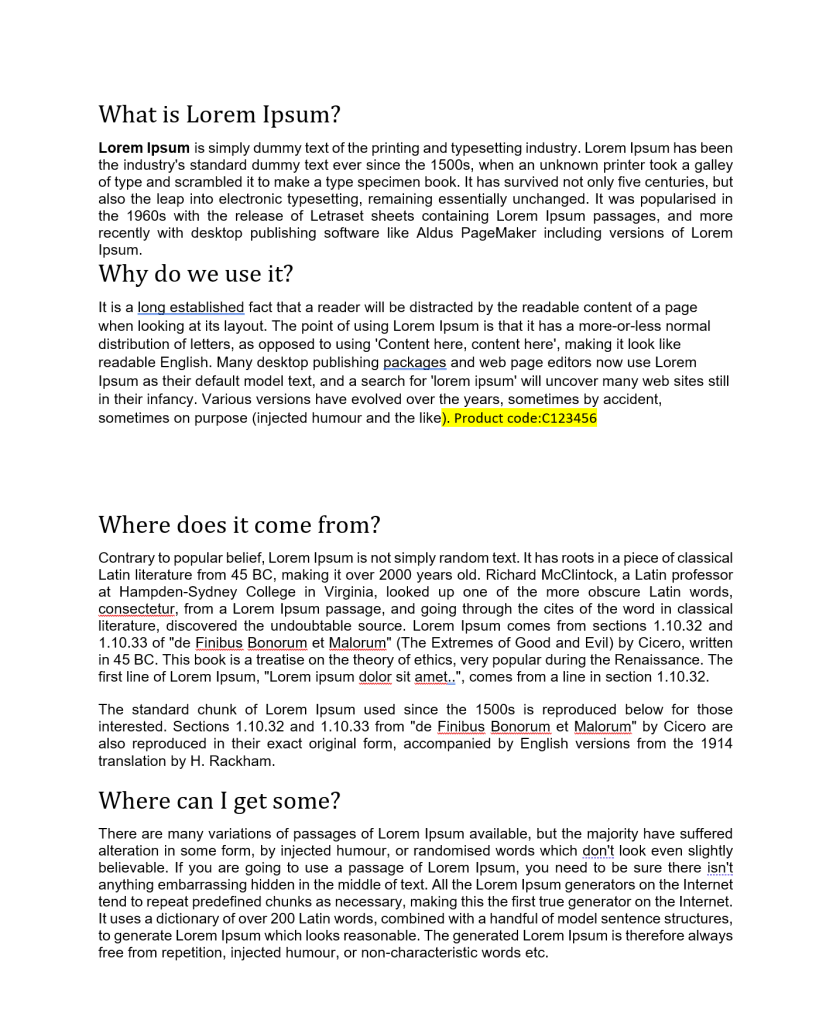
When we hit continue, we will try to upload a word document that contains a match for the Product Code sensitive information type to dropbox. Below is a sample file I created with some generic text and a product code in the contents.
When we try to upload this file to Dropbox we see the following:
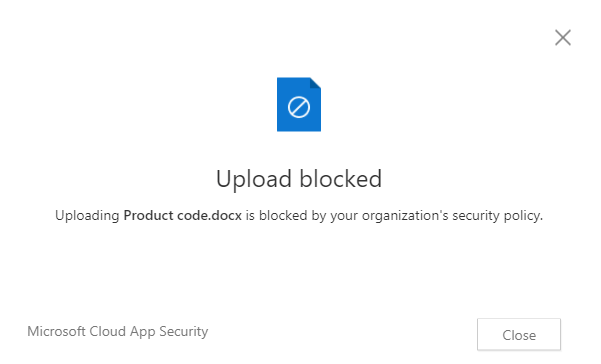
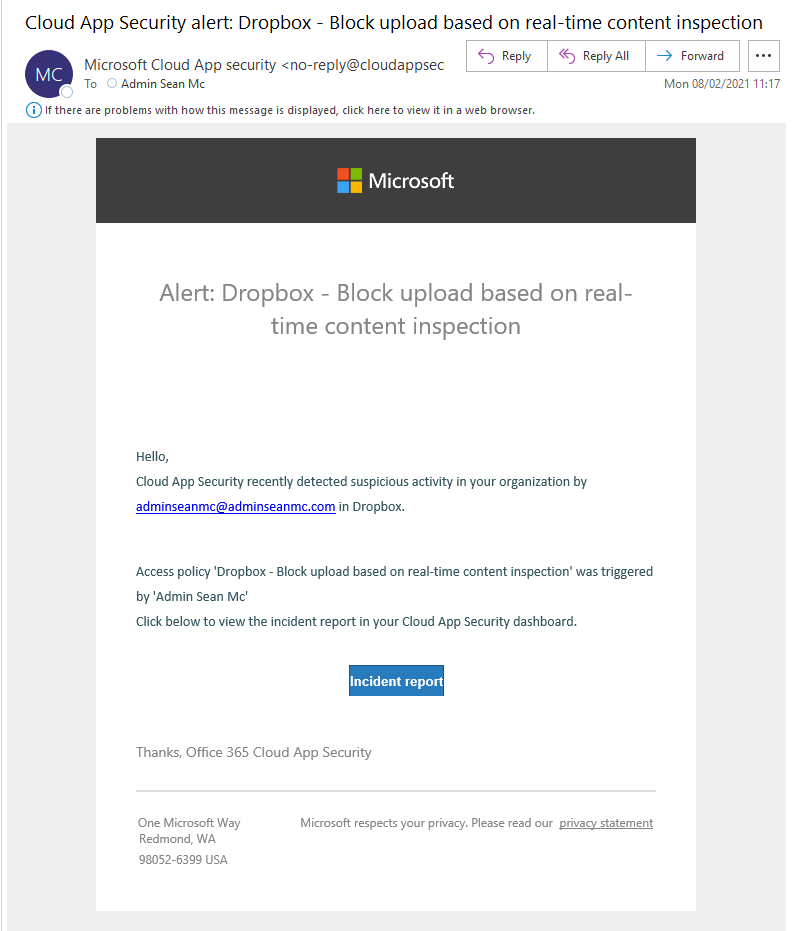
Our policy has prevented the upload of sensitive content! We also see the following alert in our email:
This is just one use case for policies in MCAS, w2e would limit upload or download to specific user groups, locations, device types etc. One useful policy I have used in the past was preventing upload / download of any data that was not assigned a sensitivity label. I recommend playing around with the different policy types and settings to see the full extent of what is available as there are a lot of permutations to meet our exact requirements. If looked at some other use cases for Power BI previously here.
Review, Interpret and Respond to Cloud App Security Alerts, Reports, Dashboards and Logs
Now that we’ve looked at most of the aspects of MCAS, we will finish our dive into the functionality by looking at how we can use it to monitor and respond to activity in our environment.
With every source we integrate into MCAS, we gather a lot of information on activity. This information is used to provide a lot of visibility into the different cloud apps we use. To view and search all of this information, we can open the “Activity Log” in the “Investigate” section of the portal. Here we can view, filter and search log entries across the platform.
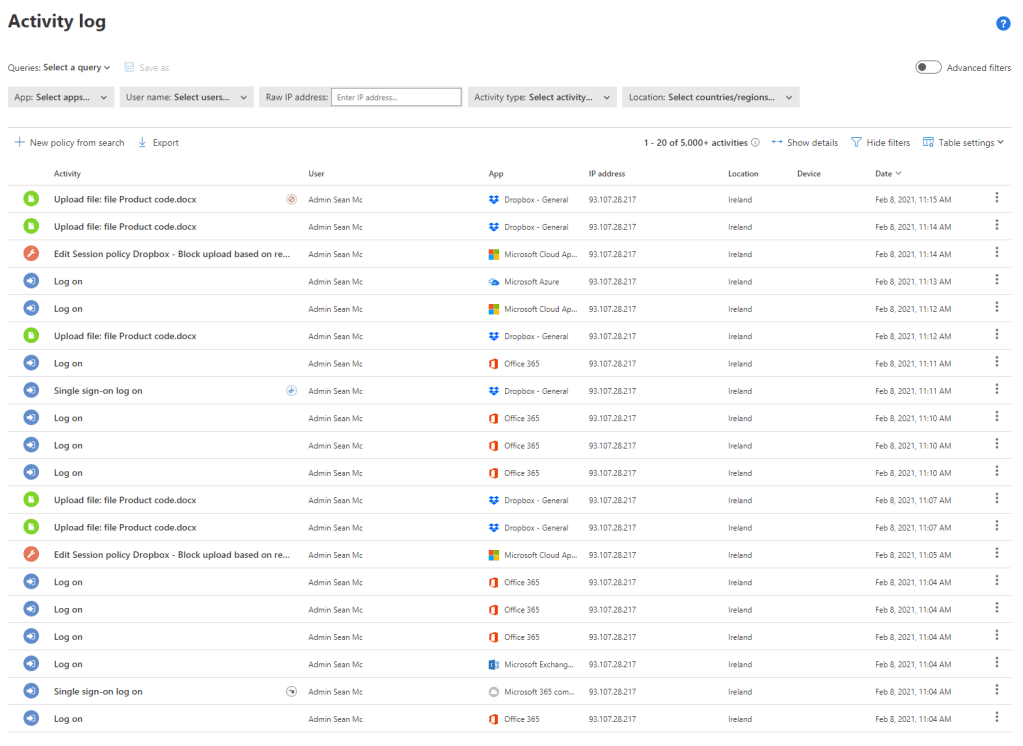
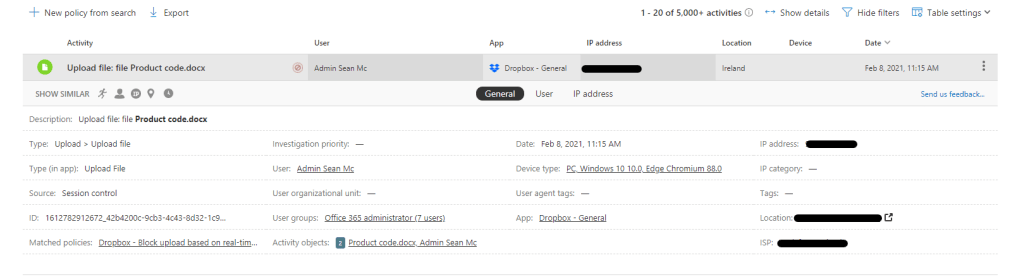
We can expand out an entry to view the details of the entry, for instance we can see full details of the attempt to upload a document during the previous step.
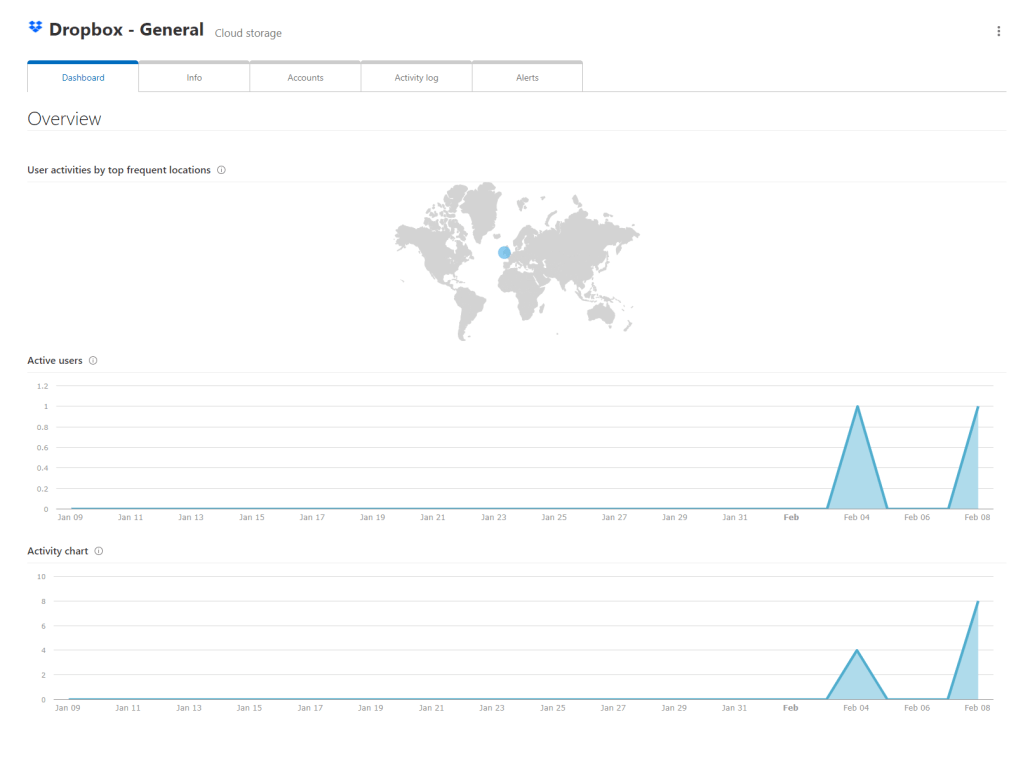
From here we can very easily create a new policy from our search results, or select any of the entities listed in a log entry to basde our search on them. For example selecting the “Dropbox” app will show us all activity relating to that app.
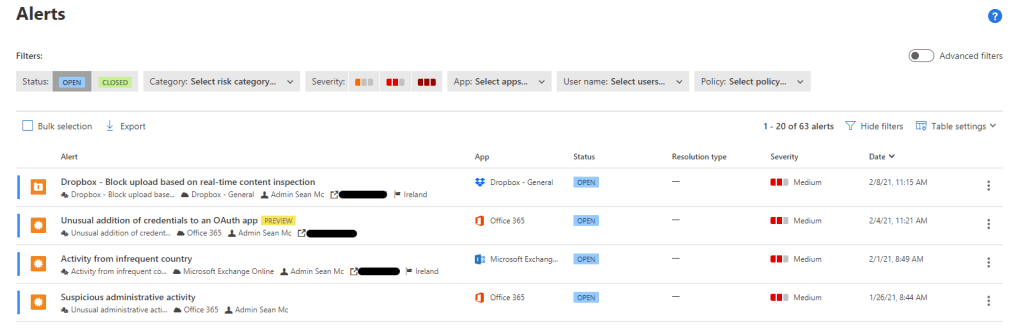
Based on the preconfigured policies and any custom policies we will also have alerts to manage under the “Alerts” section. This section shows us all of the alerts in our environment and allows us to manage them.
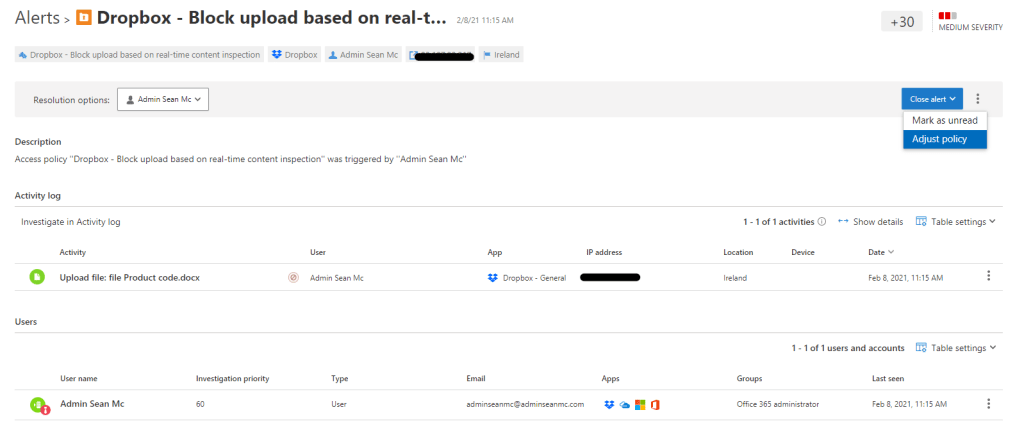
If we open up the alert for our earlier Dropbox activity, we can investigate all of the entities associated with the alert, including each activity that led to the alert being triggered. We can also close out the alert when we have either resolved it or proven it a false positive.
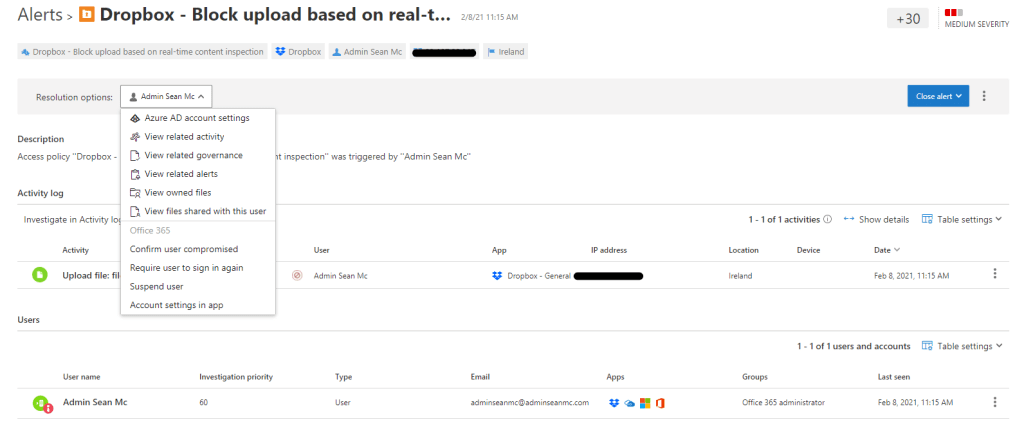
When we detect a false positive we can also optionally adjust the policy that triggered the alert to reduce the amount of false positives we see.
Summary
Over the last five posts, we’ve gone through a huge amount of functionality in MCAS. It is an extremely flexible tool with a lot of possibilities and while I believe we have covered what will be needed for the exam in these posts, I really do recommend playing with the different options and policies available to really see how flexible and powerful MCAS can be in your environment. There is also a huge amount of documentation available at the below link to help maximise the benifit of MCAS:

Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue