This post is part of the overall MS-700 Exam Study Guide. Links to each topic as they are posted can be found here.
In this section I will go through the following topics relating to Governance and Lifecycle Management for Microsoft Teams.
- Restore or troubleshoot deletion of one or more Microsoft 365 Groups
- Manage Azure AD access review for members and guests
- Perform bulk user operations with PowerShell
In the final section of the Governance and Lifecycle Management topic, I look at some more cool features and things you should know for managing Microsoft Teams.
Restore or troubleshoot deletion of one or more Microsoft 365 Groups
When a Team is deleted, so too is the underlying Microsoft 365 group object. This group will move to the Deleted Groups contained in Azure AD for 30 days before it is purged completely. Within this 30 day window the group can be restored from the Azure AD Portal by opening the Groups -> Deleted Groups page, selecting the group and clicking the Restore Group button (Figure 1).
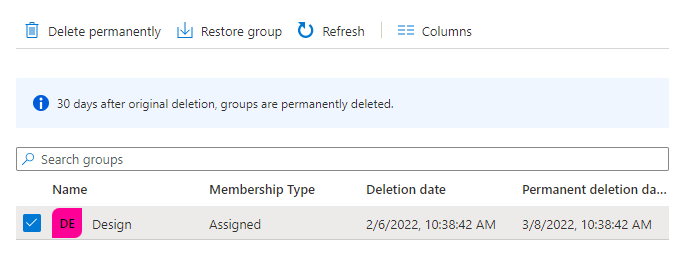
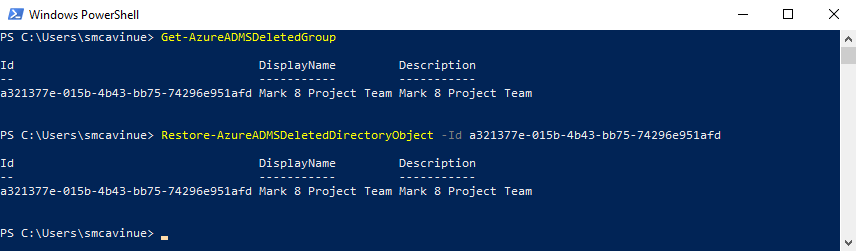
This page also shows the details of the deletion such as when the group was originally deleted and when it will be permanently removed. When the group is restored, the Team will also become available again with all members and files intact. Restoring a group can also be done with PowerShell using the Restore-AzureADMSDeletedDirectoryObject cmdlet in the AzureADPreview PowerShell module as shown in Figure 2.
Manage Azure AD access review for members and guests
I have detailed the configuration of Access Reviews previously in this post and not much has changed overall since then. In this section I will look at access reviews specifically from a Teams perspective but I recommend reading my previous post for a more detailed look.
Over time users and guests are added to different resources in the tenant for things like projects but this access is often not time limited and stale access persists for much longer than it should. Access reviews are designed to ensure that this legacy access is removed for both internal users and guests. Access reviews are configured to periodically verify that the access to a particular Application or Group / Team is still valid.
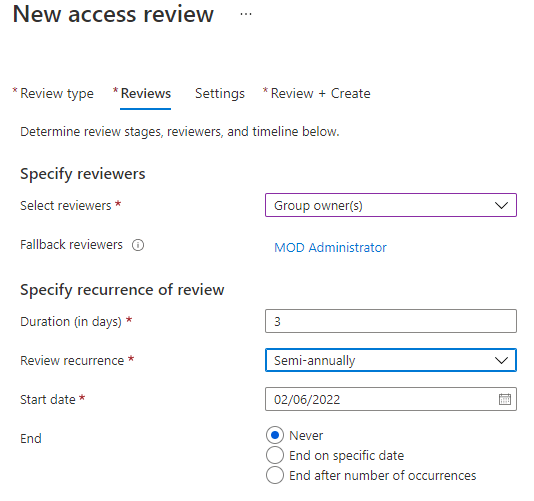
Access Reviews work by configuring a new review in the Azure Portal under Identity Governance and specifying what you would like reviewed. For example, in Figure 3, I have configured the review for select Microsoft 365 Groups / Teams and specified I want to review all users. There is also the option to only review guest access which may reduce noise and only target external members.

Next, the review process is configured by choosing who should carry out the review from the following options:
- Group Owner(s)
- Selected Users or groups
- Users review their own access
- Managers of users
I recommend Group Owners as reviewers as they generally have the most knowledge of the group and ownership over the data. Fallback reviewers can be selected in the event the chosen reviewers don’t exist and the duration of the review is configured (Figure 4). The duration of the review specifies how long reviewers have to respond.
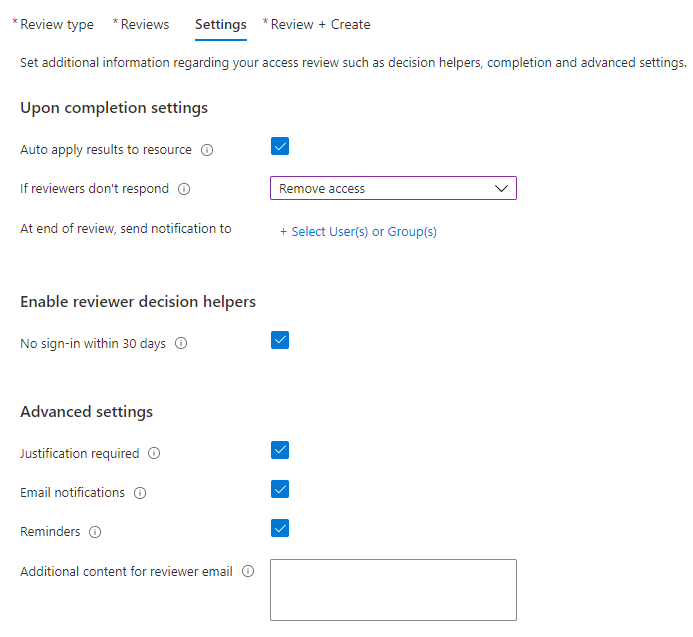
Next, the settings of the review (Figure 5) are configured:
- Auto apply results to resource – Should users be automatically removed if they are denied in the review
- If reviewers don’t respond – What action should be taken if reviewers don’t respond
- At end of review, send notification to – Who should get a review summary when the review is complete
- No sign-in within 30 days – Let reviewers know if a user hasn’t signed in over the past 30 days
- Justification required – Should the reviewer be asked for a justification
- Email Notifications – Should reviewers be notified of the review by email
- Reminders – Should users be sent a reminder mid-way through the review
- Additional Content for reviewer email – Any extra text to include in the email
When an Access Review is created users receive notifications (If configured in the settings) to review Group membership as shown in Figure 6.
Access reviews can be processed by clicking the link in the email or by navigating to Access Reviews at https://myaccess.microsoft.com/
Users can then respond to the review for each member or accept the recommendations based on the last access date as shown in Figure 7.
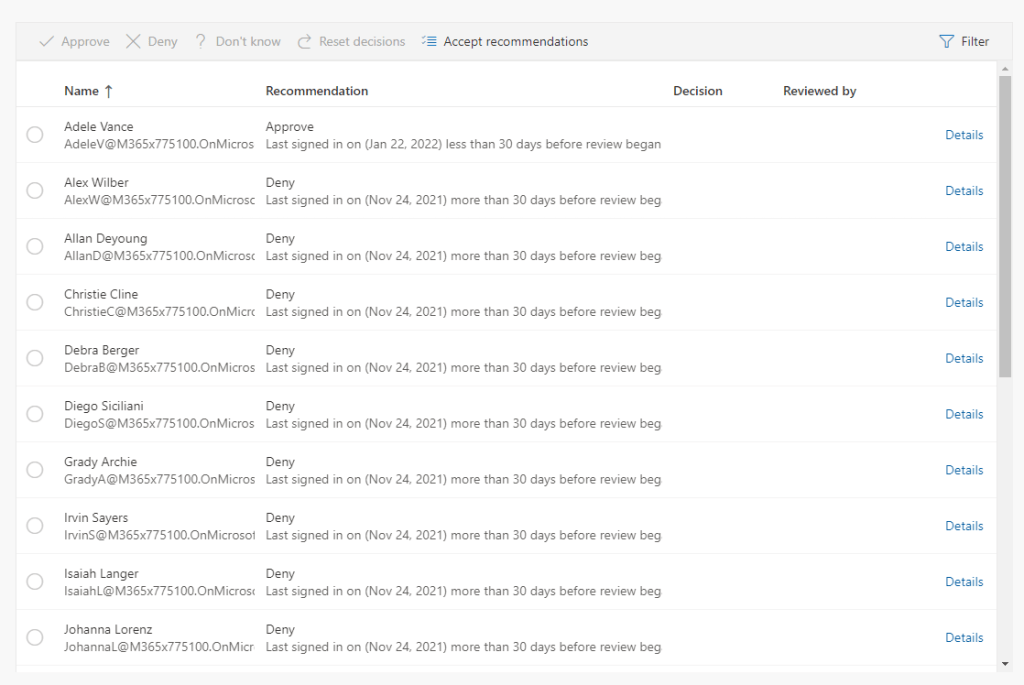
Figure 7: Processing an Access Review as a reviewer
Depending on the settings the results of the access review can automatically remove users who are denied in the review or report to an admin to remove.
Perform bulk user operations with PowerShell
When Teams environments contain very large numbers of users, manually assigning policies can take a very long time. I detailed how to user Group Policy Assignments in part 1 of this section which supports assigning policies to up to 50,000 users using the New-CsGroupPolicyAssignment cmdlet as shown below:
New-CsGroupPolicyAssignment -GroupId staff-faculty@contoso.com -PolicyType TeamsMeetingPolicy -PolicyName "EducatorMeetingPolicy" -Rank 1
I highly recommend using Group Policy Assignments for large assignments but if you can’t use this for any reason, you can also user batch policy assignments through PowerShell.
Batch Policy Assignments essentially queue up a batch of users to be assigned a change. The users are provided as an array and run using the New-CsBatchPolicyAssignmentOperation cmdlet. For example, to update the meeting policy for a group of users first create the group of users as an array:
$userArray = @('admin@M365x775100.onmicrosoft.com','adelev@M365x775100.onmicrosoft.com','meganb@M365x775100.onmicrosoft.com')
The creating the batch job using the below example shown in Figure 8:
New-CsBatchPolicyAssignmentOperation -PolicyType TeamsMeetingPolicy -PolicyName Kiosk -Identity $userArray -OperationName "Batch update Meeting Policy"
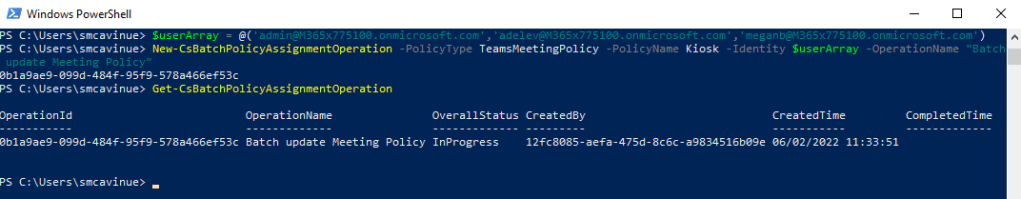
This creates the batch for processing. Batch processing supports up to 5,000 users at a time, I don’t really recommend it over Group Policy Assignments but I have detailed it here in case it comes up on the exam.
Summary
This post rounds out the Teams Governance and Lifecycle Management topic. In the next post we will move on to managing external users in Teams!


Pingback: Study Guide Series – Exam MS-700: Managing Microsoft Teams – Sean McAvinue
Pingback: Study Guide Series: Exam MS-700 – Configure and Manage External and Guest Users (Part 2) – Sean McAvinue