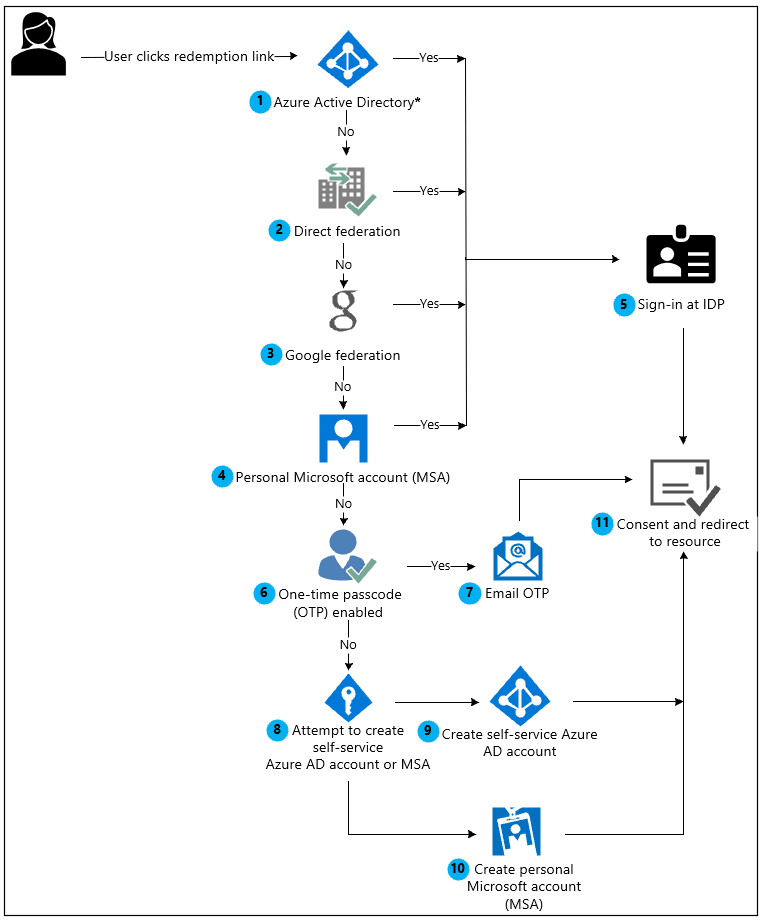
B2B Collaboration in the Microsoft Cloud is an extremely powerful feature allowing access to data and applications for almost any identity. There are multiple scenarios where a Guest invitation can be sent to external users and depending on their specific setup, the invitation is handled in a variety of ways. The below flow from Microsoft captures the decisions that are made when an external user redeems an invitation:
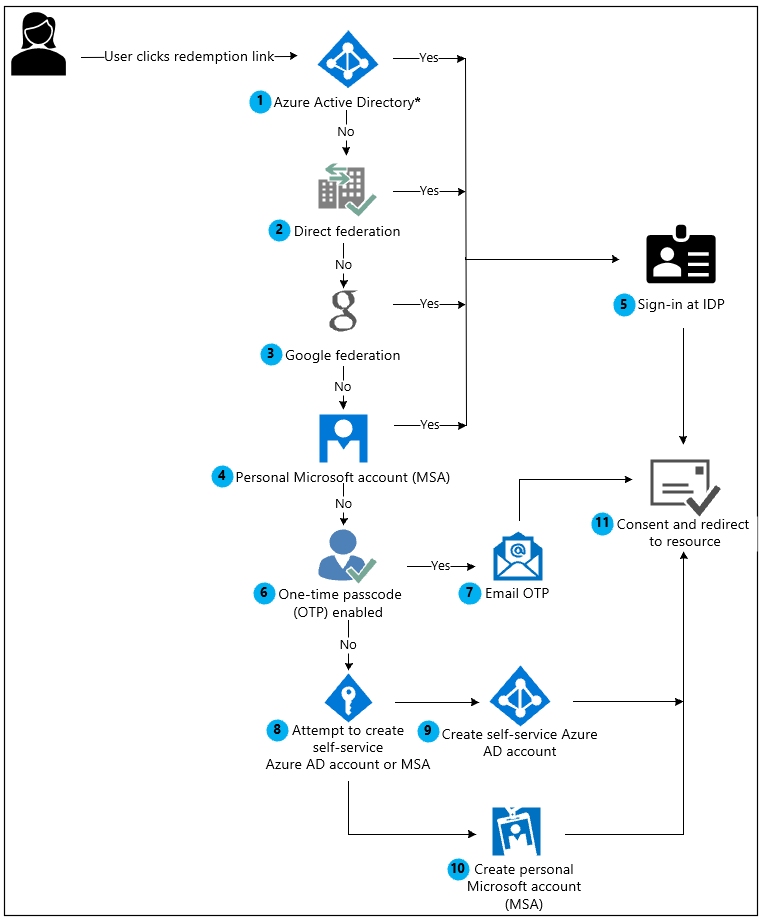
The flow above covers each scenario that an external user can experience when redeeming an invitation. With the recent announcement that Microsoft are removing support for the creation of self-service Azure AD accounts, there is obviously a change to this process. The exact announcement states:
Starting March 31, 2021, Microsoft will no longer support the redemption of invitations by creating unmanaged Azure AD accounts and tenants for B2B collaboration scenarios. In preparation, we encourage customers to opt into email one-time passcode authentication. We welcome your feedback on this public preview feature and are excited to create even more ways to collaborate.
What Does This Announcement Mean?
To understand the change, we first need to understand the flow above. This flow starts when a user clicks a redemption link and then breaks down into the below steps:
- If the user has an existing AAD account, they can sign in to AAD and redeem the invitation with their work or school credentials
- If direct federation is set up with the users IDP, they can sign in there and redeem the invitation
- If the user has a Google account, they can sign in to Google to redeem the invitation
- If the user has a personal Microsoft account, they can sign in to that to redeem the invitation
- The user signs in at the relevant IDP
- If One-Time Passcode (OTP) has been enabled in the tenancy, the user can choose to be sent a code to their email to request access to the data
- The OTP is sent to the users email account and they type it into the browser session
- The user can choose to create an unmanaged AAD account. If the users company currently has an Azure AD Tenant, this functionality can be disabled by admins
- If allowed, the user creates an unmanaged, self-service AAD account with their corporate domain to redeem the invitation
- Finally, if none of the above are applicable, the user can create a personal Microsoft Account to redeem the invitation
- The user grants consent and access the shared resource
The announcement from Microsoft essentially means that steps 8 and 9 above will be removed from this flow and if a user doesn’t have any of the relevant accounts, should use OTP to gain resource access.
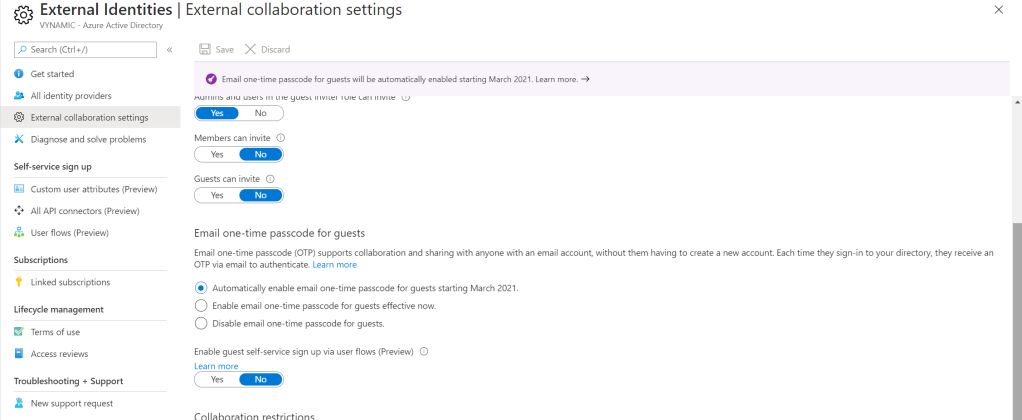
OTP is disabled by default so if this functionality is used heavily in your organization, it can be enabled from the Azure AD Portal, under “External Identities” -> “External Collaboration Settings”. This feature will be enabled by default in March, just in time for the announced change.
For more information on the B2B collaboration flow and external accounts, check out the links below:
Invitation redemption in B2B collaboration – Azure AD | Microsoft Docs
Self-service sign-up for email-verified users – Azure AD | Microsoft Docs

Pingback: Study Guide Series: Exam MS-500 – Secure Data Access Within Office 365 – Sean McAvinue