This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Secure Data Access Within Office 365” section:
- Implement and manage Customer Lockbox
- Configure data access in Office 365 collaboration workloads
- Configure B2B sharing for external users
Implement and Manage Customer Lockbox
Customer Lockbox allows you to protect your environment by enforcing an approval process to any Microsoft access. This is typically in the case of a service request that is raised with Microsoft, Microsoft engineers may need to gain access to the environment to perform troubleshooting / diagnostics. With Customer Lockbox enabled, the following is the typical process that is implemented prior to any troubleshooting which requires access to the environment as defined in the Microsoft Documentation:
- Someone at an organization experiences an issue with their Microsoft 365 mailbox.
- After the user troubleshoots the issue, but can’t fix it, they open a support request with Microsoft Support.
- A Microsoft support engineer reviews the service request and determines a need to access the organization’s tenant to repair the issue in Exchange Online.
- The Microsoft support engineer logs into the Customer Lockbox request tool and makes a data access request that includes the organization’s tenant name, service request number, and the estimated time the engineer needs access to the data.
- After a Microsoft Support manager approves the request, Customer Lockbox sends the designated approver at the organization an email notification about the pending access request from Microsoft.
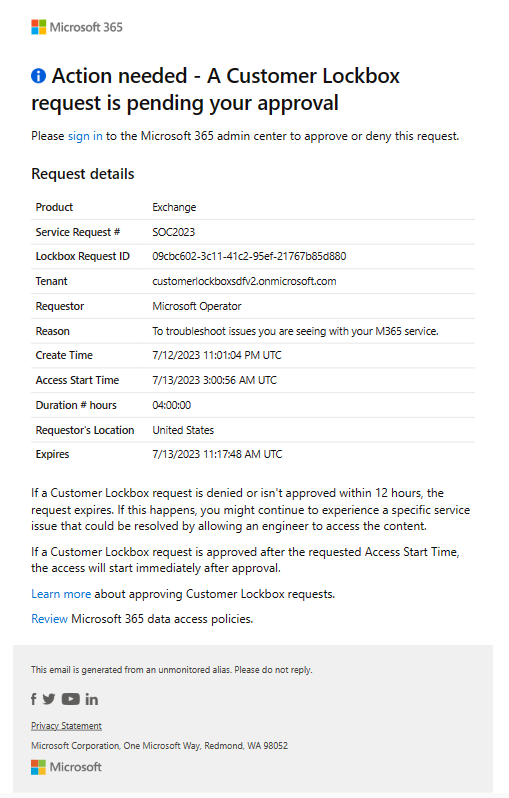 Anyone who is assigned the Customer Lockbox access approver admin role in Microsoft 365 admin center can approve Customer Lockbox requests.
Anyone who is assigned the Customer Lockbox access approver admin role in Microsoft 365 admin center can approve Customer Lockbox requests. - The approver signs in to the Microsoft 365 admin center and approves the request. This step triggers the creation of an audit record available by searching the audit log. For more information, see Auditing Customer Lockbox requests.If the customer rejects the request or doesn’t approve the request within 12 hours, the request expires and no access is granted to the Microsoft engineer. ImportantMicrosoft does not include any links in Customer Lockbox email notifications requiring you to sign in to Office 365.
- After the approver from the organization approves the request, the Microsoft engineer receives the approval message, logs into the tenant in Exchange Online, and fixes the customer’s issue. Microsoft engineers have the requested duration to fix the issue after which the access is automatically revoked.
To enable Customer Lockbox in the tenancy, open up the Microsoft 365 Admin Portal and navigate to “Settings” -> “Org Settings” -> “Security & Privacy” -> “Customer Lockbox”. From here, tick the checkbox for “Require approval for all data access requests” to enable the feature.
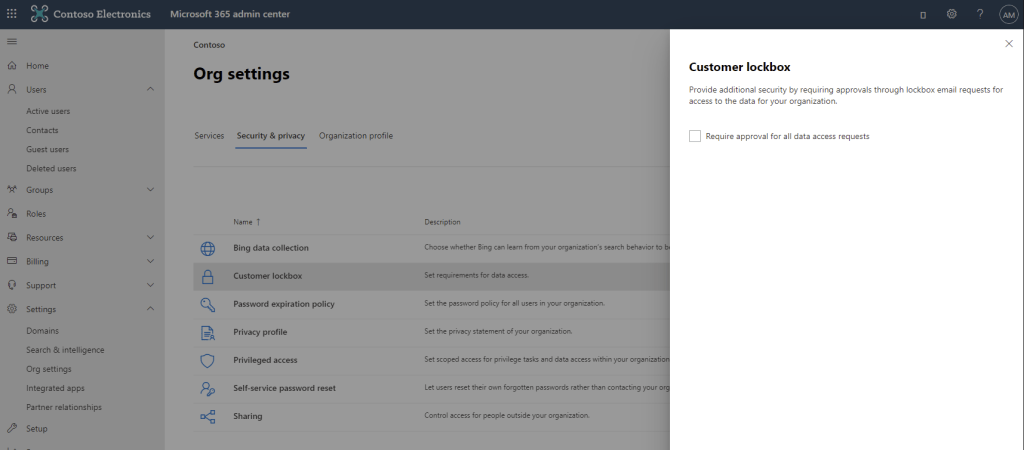
Note: All users accessed must have a valid SKU assigned for Customer Lockbox
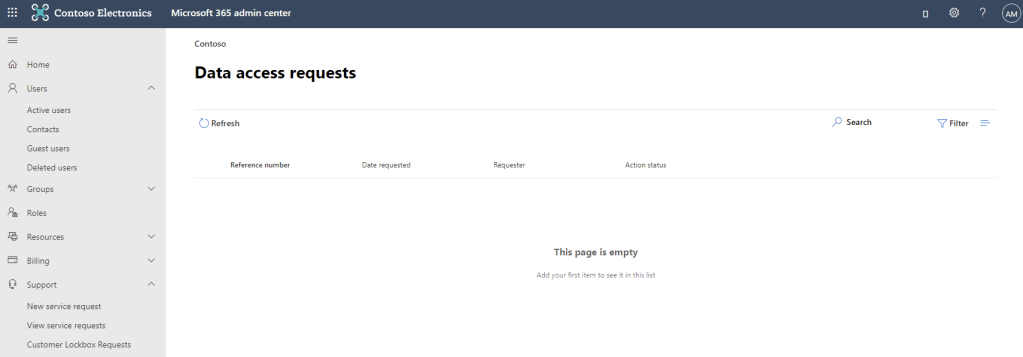
Once enabled, all data access requests will be listed in the “Support” -> “Customer Lockbox Requests” section of the admin portal.
Data access approvals can be found in the unified audit log under the activity “Set-AccessToCustomerDataRequest”
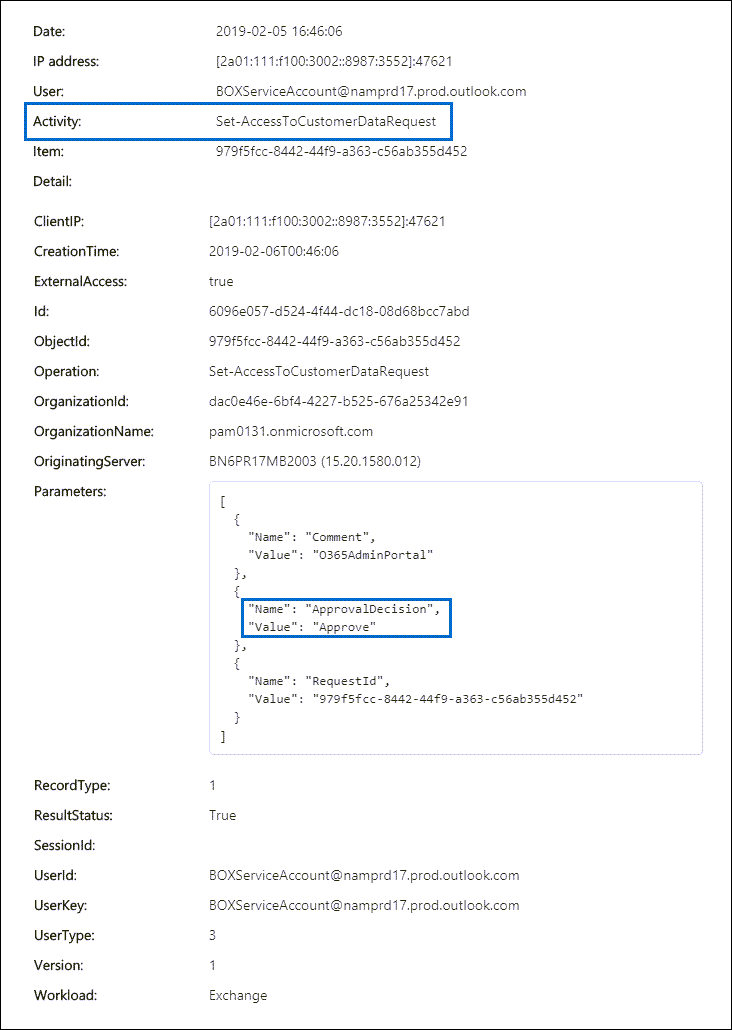
Any activity taken by Microsoft Engineers will be shown in the log as the user “Microsoft Operator”

Configure Data Access in Office 365 Collaboration Workloads
Data Access in Microsoft 365 comes down to the configuration of each collaboration component that stores or processes data. This can include a variety of technologies such as SharePoint Online, Teams etc. As such, there’s no single tool which we can use to “Configure Data Access”.
To help control access to data, we can implement identity and authentication level protections which we’ve seen while configuring Conditional Access previously. This allows us to add a layer of control around how data is accessed and by who. We can also apply Information Protection controls such as Sensitivity Labels and Data Loss Prevention to help protect our sensitive data. We will go through each of these in a future post. For this topic, we will look specifically at the configuration of the workloads themselves and how we can control the different collaboration capabilities.
SharePoint Online / OneDrive
When configuring SharePoint Online for collaboration, there are a few configuration items that impact collaboration which we need to be aware of:
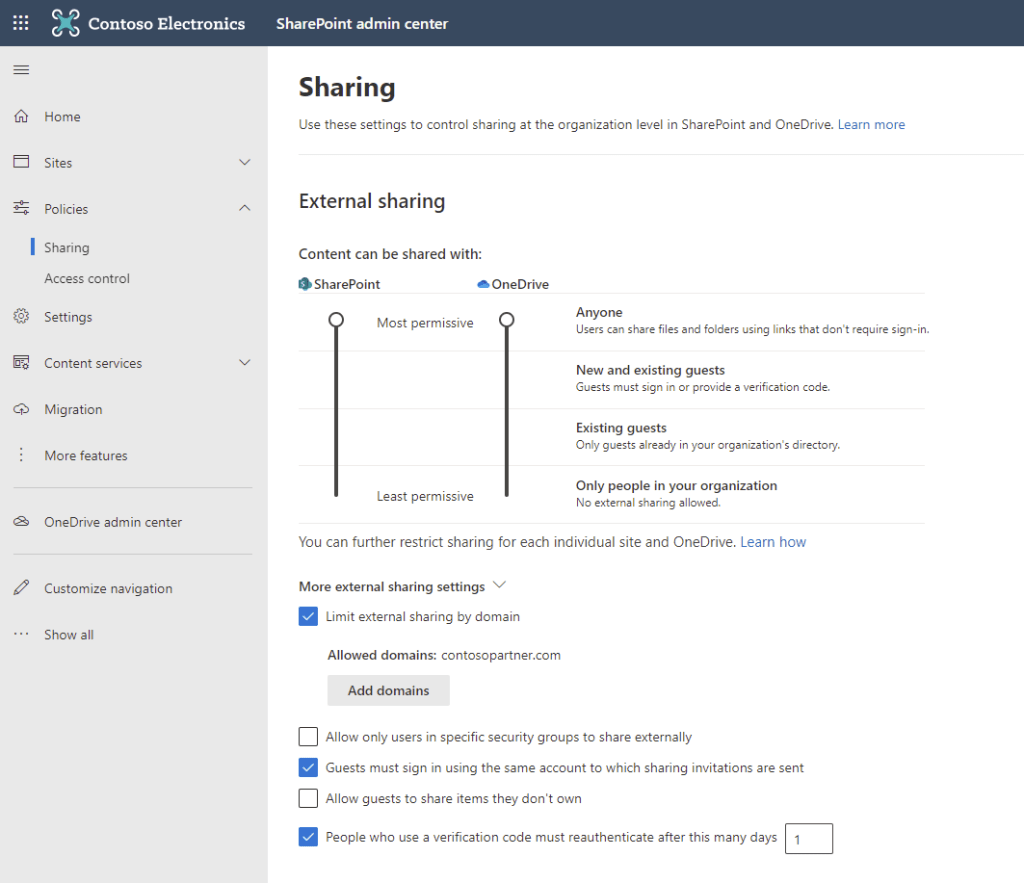
In the SharePoint Admin Center, under “Policies” -> “Sharing”:
- External Sharing Policy – This policy controls the level of sharing available to external identities. This policy can be set separately for both SharePoint Online and OneDrive however OneDrive can never be less restrictive than SharePoint. The levels available are:
- Anyone: Anonymous external sharing is allowed, users can freely share data externally
- New and existing guests: Users can provision access for any external party however external users must prove their identity by signing in or completing a one time passcode challenge
- Existing guests: Only Azure AD guests who have been provisioned in AAD can be shared with. B2B collaboration is detailed further in the next section of this post
- Only people in your organization – Users cannot share externally from SharePoint/OneDrive
- Limit External Sharing by Domain – This option allows us to define a list of external domain names to which we allow sharing. This is generally a set of trusted partner companies. This can be set to an allow list or a block list
- Allow only users in specific security groups to share externally – This setting allows us to limit external sharing to specific groups of users
- Guests must sign in using the same account to which sharing invitations are sent – This setting controls if guests who receive email invitations must use an account linked to the recipient email to redeem the invitation
- Allow guests to share items they don’t own – This setting controls if guest users can re-share items that they have been shared
- People who use a verification code must reauthentication after this many days – The number of days users who authenticate using a verification code sent to their email can access without being prompted to re-authenticate
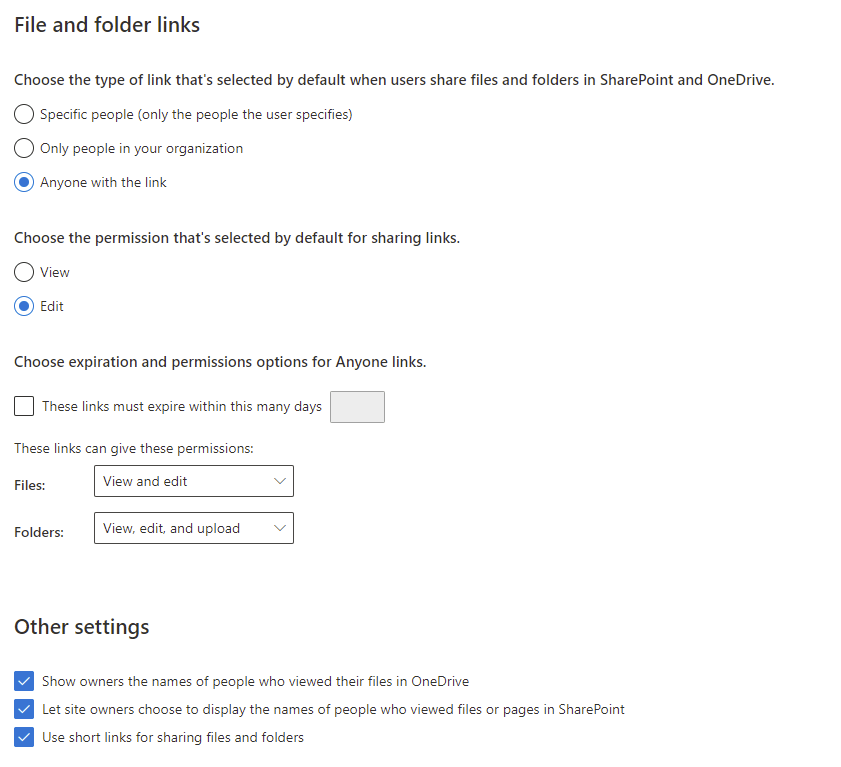
- Choose the type of link that’s selected by default when users share files and folders in SharePoint and OneDrive – This setting controls the default link that us created when users share files (Specific people, Only people in your organizations, anyone with the link)
- Choose the permission that’s selected by default for sharing links – The default link permissions that are set on files shared (Edit, View)
- Choose expiration and permissions options for Anyone links – Here we configure the expiration of links that are shared with anyone, the permission levels that can be granted to these anonymous sharing links
- Show owners the names of people who viewed their files in OneDrive – This controls if owners can track who has viewed their files
- Let site owners choose to display the names of people who viewed files or pages in SharePoint – Similar to the above but at a site level
- User short links for sharing files and folders – This will replace typical lengthy links with short links that will redirect to the content
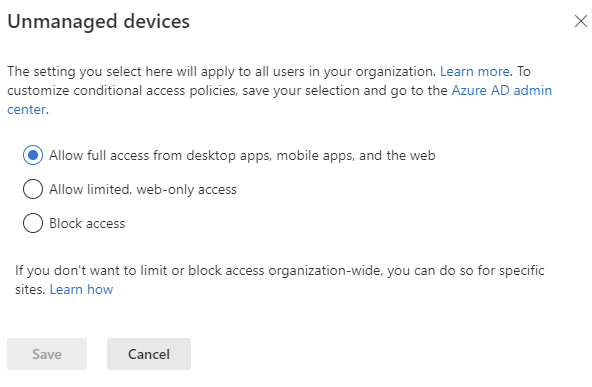
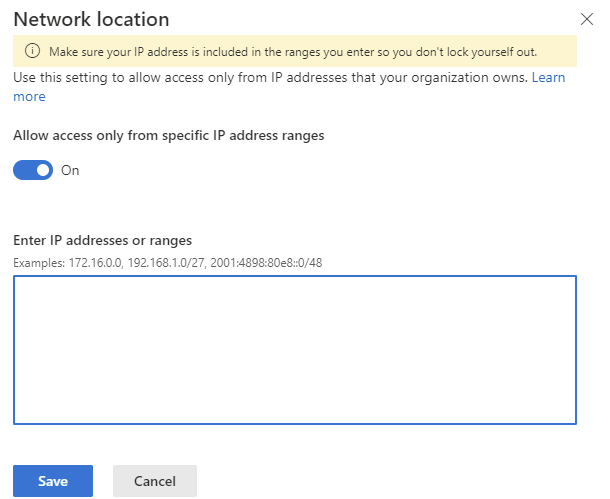
In the SharePoint Admin Center, under “Policies” -> “Access Control”
- Unmanaged Devices – Here we can limit the functionality available to users who access data from an unmanaged device. We can grant full access, Limited, web-only access or block access completely
- Idle session sign-out – We can configure automatic sign out and reauthentication of inactive sessions and also provide notice before sign out

- Network Location – We can limit our SharePoint / OneDrive access to specific IP ranges
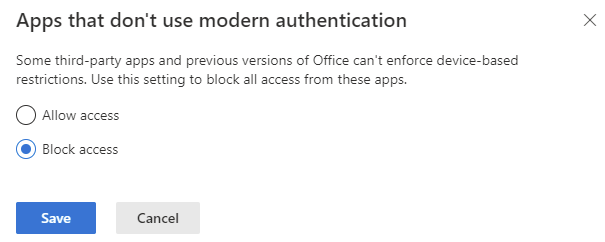
- Apps that don’t use Modern Authentication – Here we can block apps that don’t use Modern Authentication
Microsoft Teams
While Microsoft Teams documents are held in SharePoint and OneDrive and the above restrictions apply, there are a few more items to consider with Teams:
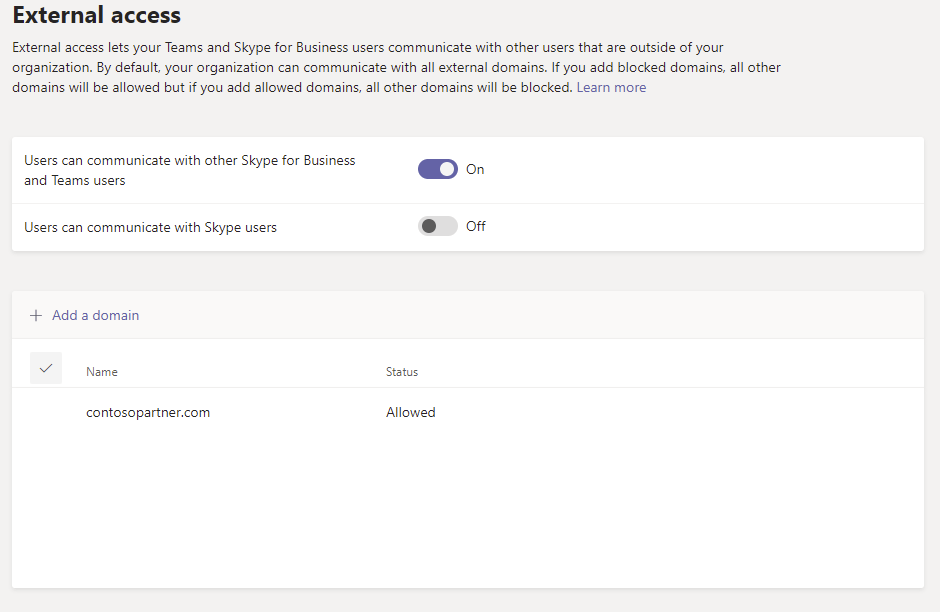
Under “Org-wide settings” -> “External Access”:
- Users can communicate with other Skype for Business and Teams users – Controls if users can communicate externally with Teams / Skype for Business users
- Users can communicate with Skype users – Controls if users can communicate with consumer Skype users
- Add a domain – Here we can define a allow or block list for external communication
Under “Org-wide settings” -> “Guest Access”:
- Allow guest access in Teams – Should guest access be allowed in Teams
- Calling – Define what calling functionality is available to guest users in Teams
- Meeting – Define what meeting functionality is available to guests users in Teams
- Messaging – Define what messaging functionality is available to guests in Teams

Configure B2B Sharing for External Users
Along with the controls specified above, we can configure how our organization can interact with external users by configuring out B2B policy. In the Azure Active Directory Portal, open up “User Settings” -> “External Collaboration Settings”. In this page we can configure how our B2B guest accounts are managed. The settings available here are:
- Guest user access – This setting defines the level of access guest accounts have available to them in the directory
- Guest invite settings – These settings control how guests can be provisioned in the directory
- Admins and users in the guest inviter role can invite – Defines if Admin users and Guest Inviters can invite guests to the organization
- Members can invite – Defines if non-admin users who don’t have the guest user inviter role can invite guests to the organization
- Guests can invite – Defines if existing guests can invite other external users to be a guest in the organization
- Enable guest self-service sign up via flows – This preview feature can allow the use of user flows through the self-service sign up functionality
- Email one-time passcode for guests – As I’ve detailed in a previous post, users who do not have an account to redeem an invitation can use the one time passcode functionality to gain access
- Collaboration restrictions – Configure allow or block lists for external domains who can be invited as guests



Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue