This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
Note: Microsoft Defender ATP has recently been renamed Microsoft Defender for Endpoint. This post will refer to it using the new name but the exam may contain references to the older name. For any topics referencing Microsoft Defender ATP, read as Microsoft Defender for Endpoint.
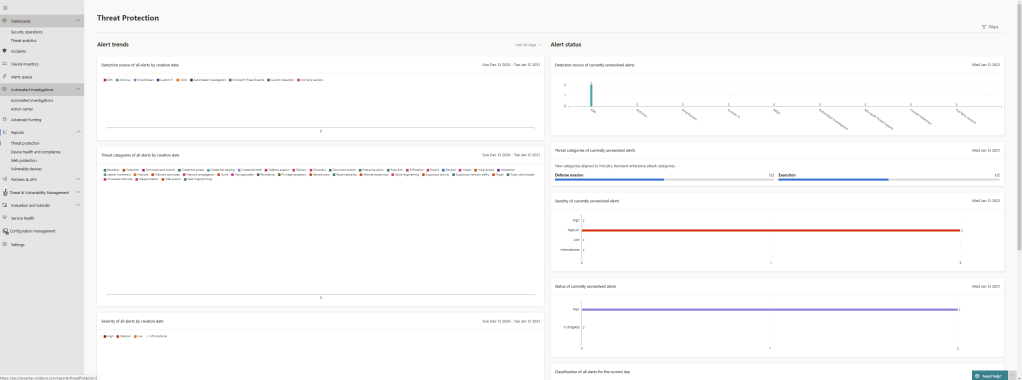
With Microsoft Defender for Endpoint configured in our last post, we’ll now look at how we can Manage and Monitor our new implementation. I’ve run some of the attack simulations which are available in the Evaluations & Tutorials page of the Security Center on the machine we enrolled so we can see how the information is presented to us. If you are following along in a lab environment I recommend running some of these simulations so you have data to work with.
Dashboards
The first thing we will see in the Security Center is our Security Operations Dashboard, here we get a nice overview of the state of our environment. In the screenshot below we can see we have two active alerts which relate to one device at risk:

We can also see that an automated investigation was carried out against one of our alerts. We’ll see that in more depth as we go.
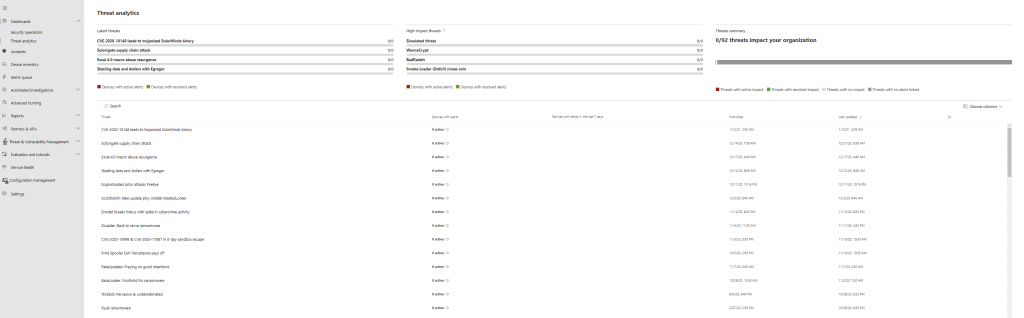
Under the Security Operations Dashboard on the navigation pane we have our Threat Analytics dashboard. This is where we will find known threats, information about each. We can also track any of our devices which have been flagged as affected by a specific known threat.

Incidents
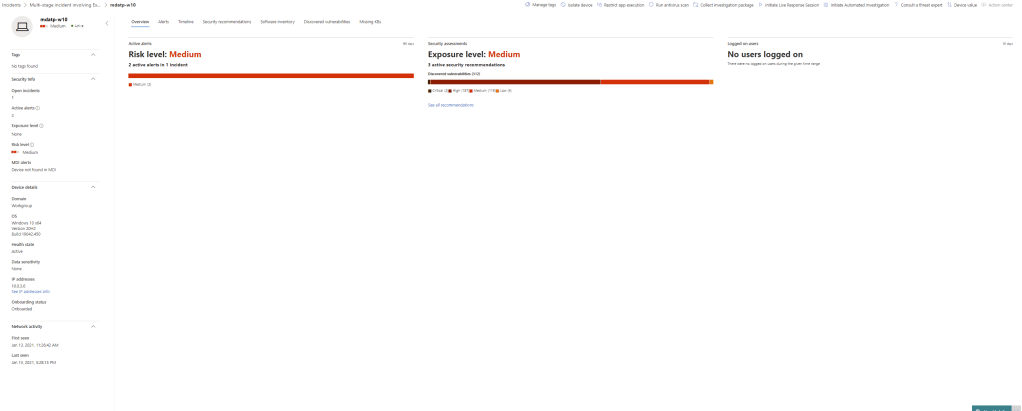
Next we have our Incidents page, this is where we can track incidents raised by Defender against our machines. We can see in the below screenshot that a Multi-stage incident has been raised against out test machine. Both alerts that were raised are associated with the single incident.

By opening our incident we can drill down into the specific Alerts, Devices, Investigations and Evidence:

Device Inventory
Next, we have our device inventory:

Here we can see each device we have onboarded and it’s current risk level and status. We can click on an individual device for more information. On the Device page, we can see a massive amount of information about the device and it’s current health state. We can also initiate such as isolating devices, restring apps from running, run Antivirus scans, collect diagnostics and even remotely connect to the device to perform some manual diagnostics.
Alerts Queue
Our alerts are displayed here, similar to incidents, we can open the alert by clicking on it and see a lot of context around the specific issue.
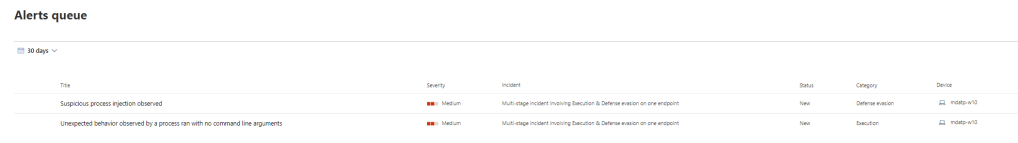
We can see a complete timeline complete with individual process names along with a ton of useful information on the potential threat.

In the right pane, we can also perform tasks such as assign the alert to an incident, assign to an admin to investigate, create a rule to suppress the alert, classify and resolve the alert.

Automated Investigations
When an automated investigation is triggered, it will appear on this page. Here we can see an investigation was kicked off as a result of one of our alerts.

Opening the investigation shows us a massive amount of information gathered by the investigation. We can see for instance that as a response to the alert, Defender automatically analysed a large set of entities (2333 files, 106 processes, 273 Services, 401 divers and 11 IP Addresses)
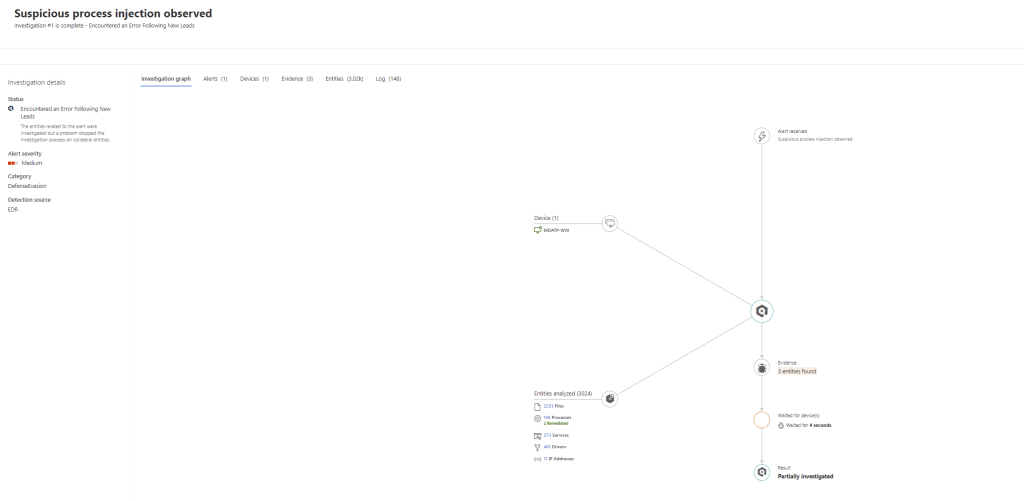
We can then navigate the investigation to see the results. In the below screenshot we can see the processes that were analysed as part of the investigation and we can also see the action taken to terminate the Notpad.exe process which was delivering the malicious payload.

Advanced Hunting
As Defender for Endpoint gathers a massive amount of data from our devices, we have an incredible amount of information available to us.
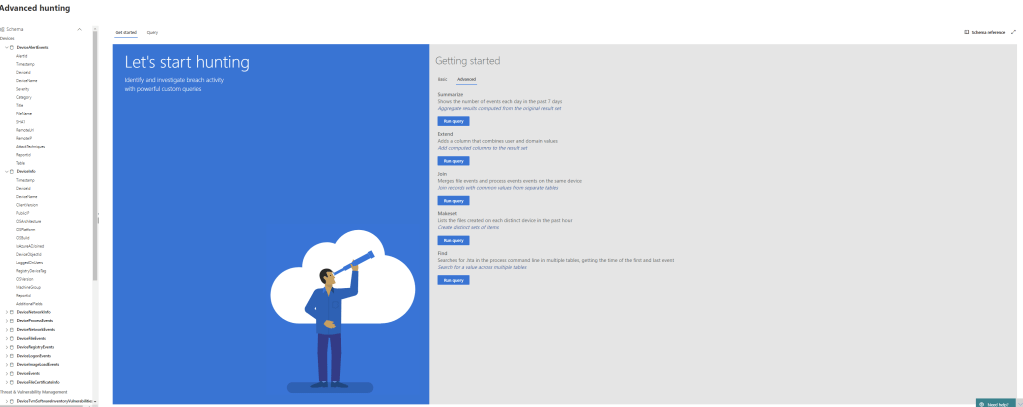
With advanced hunting, we can directly query all of this data. For instance, we can query events on our client devices such as new file or process creation centrally. Allowing us to detect potential threats on a massive scale. Along the left of the page, we can see the Schema we use when using Advanced Hunting to build queries. We can also run some sample queries from the home page to get used to using Advanced hunting and syntax of queries.

Microsoft have extensive documentation to help you get to grips with using advanced hunting. I don’t think you will need to go too in depth for the exam but it is good to test and get experience using advanced hunting.
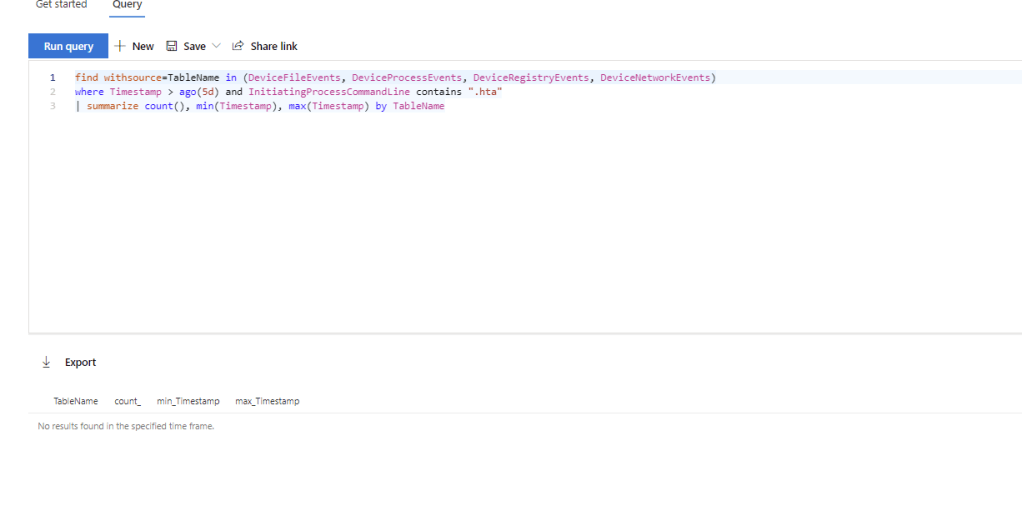
Reports
In the reports section we can view detailed reports on Threat Protection, Device Health, Web Protection and Device Vulnerabilities.
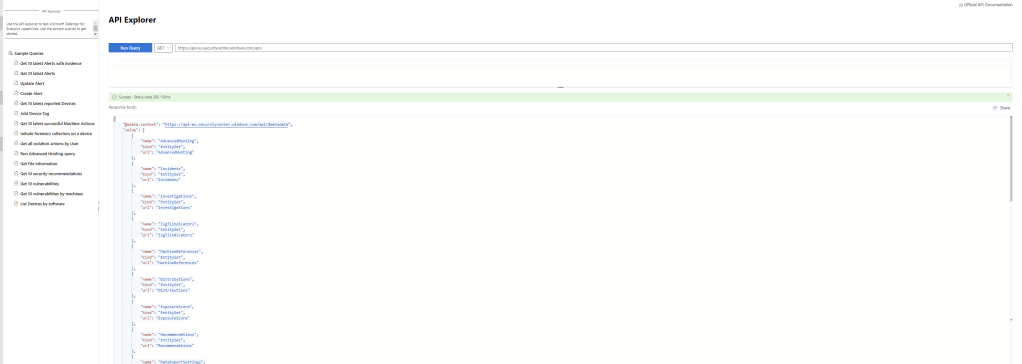
Partners & APIs
From the Partners & APIs we can view available partner application to integrate with our Defender for Endpoint.

We can view any existing partner applications we have attached and configure data export settings for forwarding events. We can also test out the Defender for Endpoint API using the API explorer.
Threat & Vulnerability Management
Under Threat & Vulnerability Management we can track known threats and vulnerabilities against our devices, allowing us to focus on recommendations to reduce exposure and improve the security posture of or device estate.

Summary
There is a massive amount of power in Defender for Endpoint and with that is a lot of knowledge required to use it effectively. Over the last few posts we’ve looked at planning, implementing and managing Defender for Endpoint. I’ve touched on the aspects I believe will be required for the exam but it is definitely an area worth exploring further. I’ve included some links below that are worth reading for more information about configuring and using Defender for Endpoint to security your environment.
Microsoft Defender for Endpoint – Windows security | Microsoft Docs
What’s new in Microsoft Defender ATP – Windows security | Microsoft Docs
Microsoft Defender ATP data storage and privacy – Windows security | Microsoft Docs
Overview of Microsoft Defender Security Center – Windows security | Microsoft Docs
Ensure your devices are configured properly – Windows security | Microsoft Docs
Get devices onboarded to Microsoft Defender ATP – Windows security | Microsoft Docs
Optimize ASR rule deployment and detections – Windows security | Microsoft Docs
Verify data storage location and update data retention settings – Windows security | Microsoft Docs


Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue