This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and Manage Device and Application Protection” section:
- Plan for device and application protection
- Configure and manage Microsoft Defender Application Guard
- Configure and manage Microsoft Defender Application Control
Plan for Device and Application Protection
In order to control devices connecting to our Microsoft 365 services, we can leverage Microsoft Endpoint Manager (Intune) to manage the devices themselves, the applications they use to connect, or both. When using Intune to manage devices, we can control the configuration on the device at a granular level, taking advantage of device configuration policies and compliance policies as well as deploying and managing applications on the devices. If we don’t want to control the entire device, for instance, a users personal phone, but still want to protect our organizational data that the phone connects to, we can use application protection to ensure that the corporate context within the applications is separated from the users own data and apps, control how a user can copy data from the apps and even secured with encryption, pin, biometrics etc.
In this post (and the next) we will look at some of the aspects of device and application protection that we can implement to secure our data while empowering users with the flexibility of Microsoft 365.
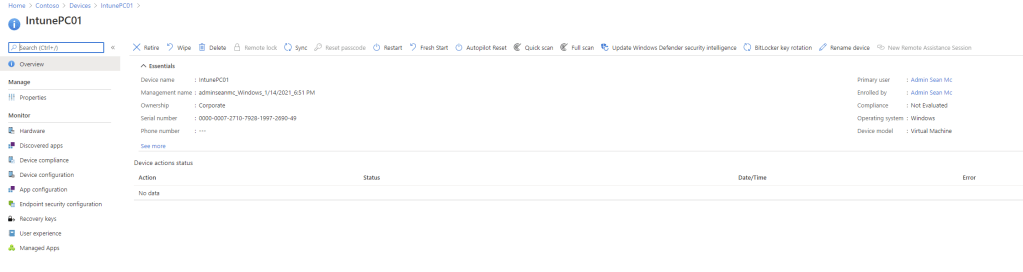
First, we will set up our lab environment with an Intune enrolled device.
Configure and manage Microsoft Defender Application Guard
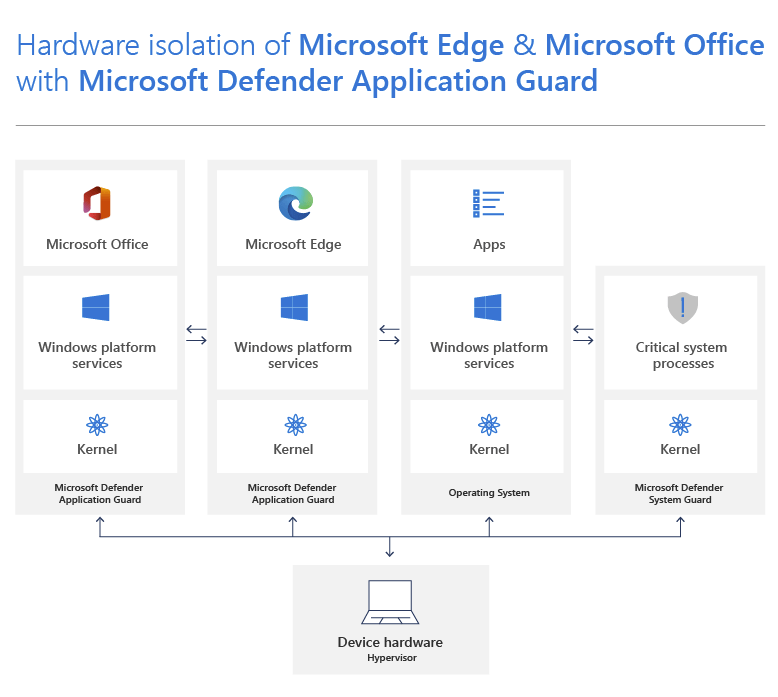
Microsoft Defender Application Guard is a technology which provides a layer of separation between Microsoft Edge (and Office in Preview currently) and the base Windows 10 operating system on the device. It does this by opening untrusted sites inside of a virtualized container on the operating system. You can still configure trusted sites to open and interact with Windows, but protect against unknown threats on the web.
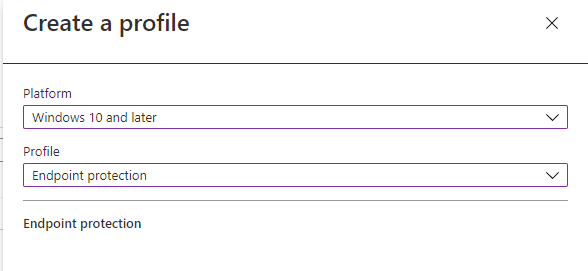
To configure application guard using Microsoft Intune, open up the Windows -> Device Configuration page and create a new, Windows 10, Endpoint Protection profile.
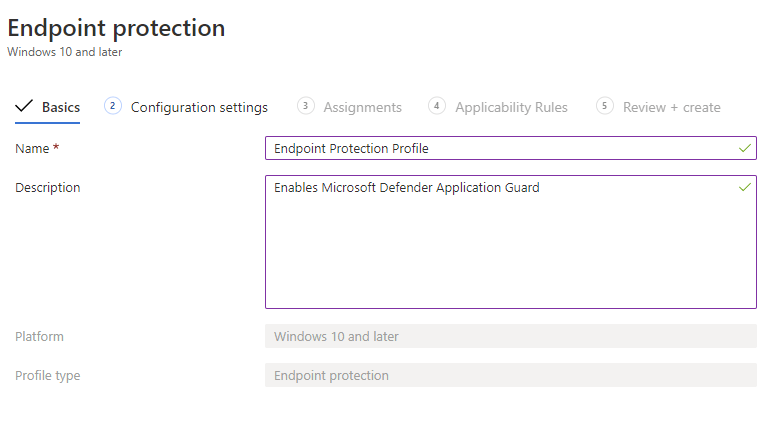
Fill out the basics and click next.
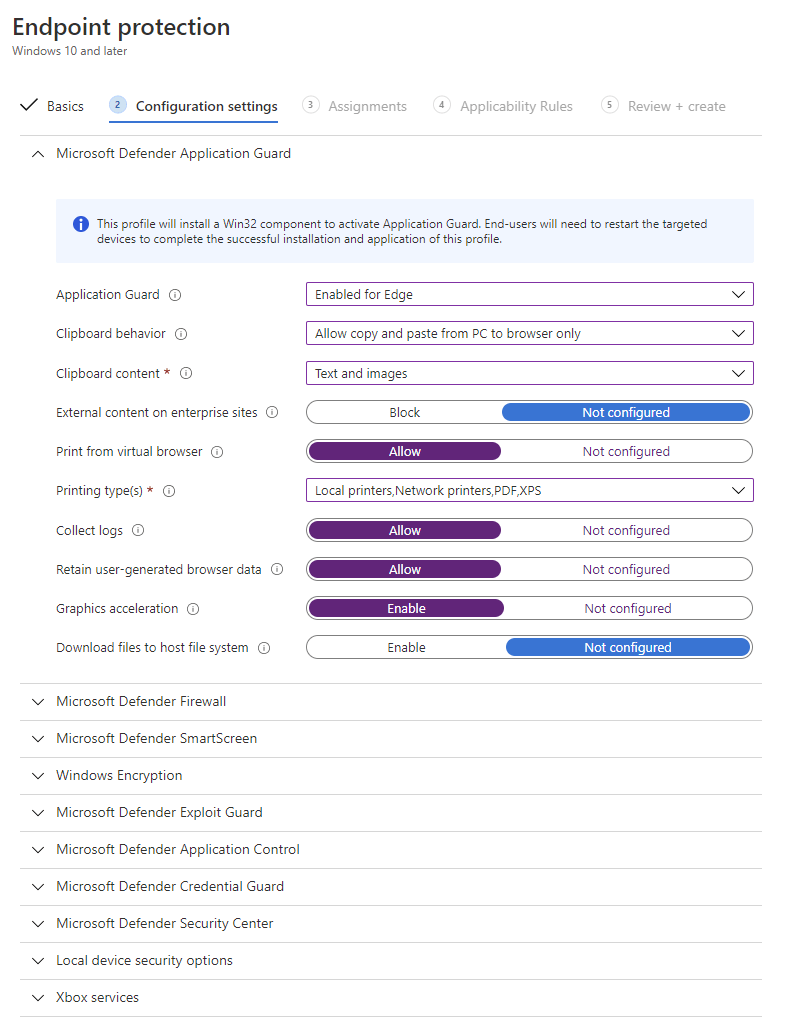
Under the configuration settings, expand out “Application guard” and configure the settings. The settings available are detailed below:
- Application Guard – Enable or not configure Application Guard
- Clipboard behaviour – Define if copy and pasting should be allowed between the container and the PC
- Clipboard Content – Define if Text, Images or both are allowed to be copied as per the previous setting
- External content on enterprise sites – Define if external content which is hosted on a trusted site is viewable
- Print from virtual browser – Should printing be allowed from the container
- Printing type(s) – Define what type of printing is allowed as per the above setting
- Collect logs – Log the events within the container
- Retain user-generated browser data – Should items such as favourites, cookies and saved passwords be saved from within the container
- Graphics acceleration – For graphics intensive sites, this allows a virtual GPU to be added to the container to help load complex pages and images faster
- Download files to host file system – Define if the user can download files from within the container to the host OS
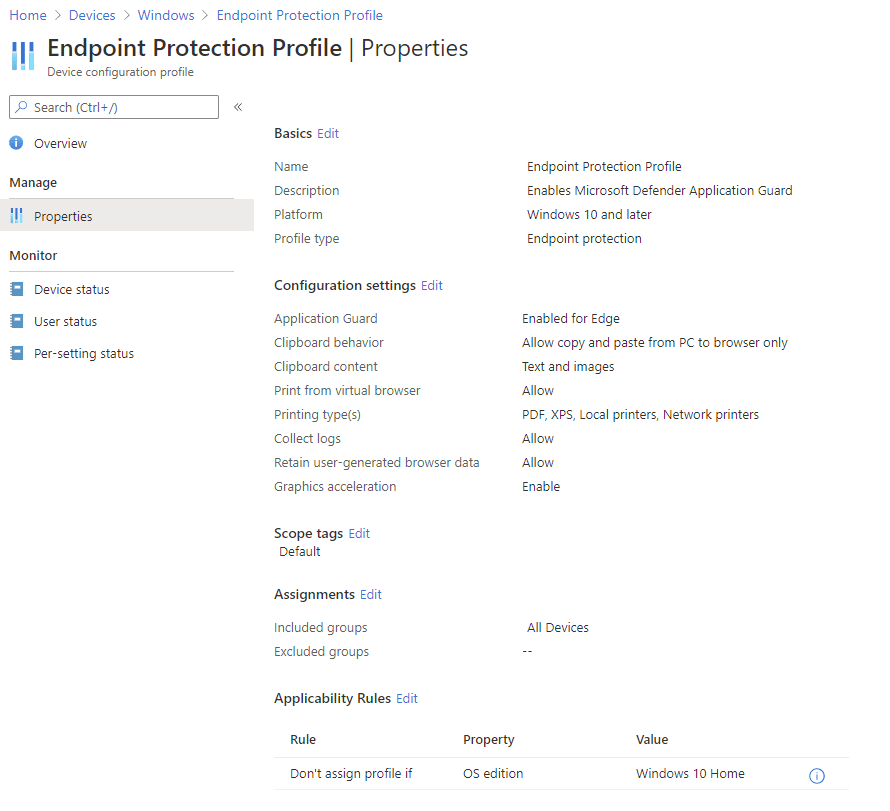
Once configured, we assign the policy to our devices. I’m assigning to all devices as there is only one enrolled.

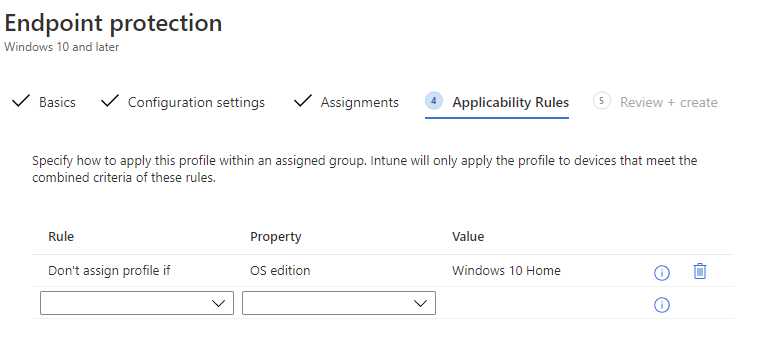
We could configure applicability rules to include or exclude devices based on OS version or Edition. For instance, below we are excluding Windows 10 Home devices from our policy.
Finally hit create to create our configuration profile.

We’ll test each of the policies at the end of the configuration so let’s move on to Application Control for now.
Configure and manage Microsoft Defender Application Control
Microsoft Defender Application Control protects your devices by limiting the applications that are allowed to run on the device. When using Application Control we can define an Application Control policy to limit the apps, scripts and processes which are allowed to run on our device. Application Control takes a significant amount of effort to set up and maintain, it’s important that detailed planning is carried out before implementing in production. Luckily, Microsoft have made extensive documentation available (Plan for WDAC policy management (Windows 10) – Windows security | Microsoft Docs) to help organizations plan, implement and maintain Application Control.
Before enabling Application Control on our machines, we need to ensure we have created a policy to apply. Microsoft have deployed default policies which can be used for reference at “C:\Windows\schemas\CodeIntegrity\ExamplePolicies“. Here we can see the policies Microsoft have published. To create our own policy using our machine as a base image, log on to the machine, and follow the steps outline here. The policy will take some time to catalogue your machine. You can also use the WDAC Wizard tool to help with this process. For the exam you will need to know the processes but I don’t believe you’ll need to be very in depth at this point, that’s just my opinion though.
If we want to deploy the default policies, we need to create an Endpoint Protection profile. Since we already have one created for Application Guard, we can open up our existing profile and edit the configuration settings.
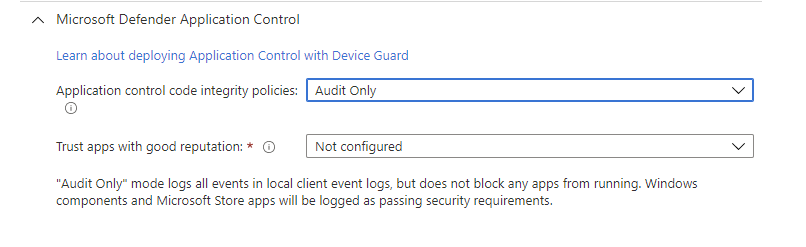
here we can expand out Microsoft Defender Application Control and configure the following settings:
- Application control code integrity policies – Define if application control should be turned off, configured to audit or enforced
- Trust apps with good reputation – Defines if trusted apps should be allowed to run, these apps are defined by Microsoft for the default policies
We can also deploy our own custom policies using a Custom OMA-URI Profile, that process is detailed here.
When configured, save the profile to commit the changes.
Testing the Policies
With our profiles applied, we can now test these policies on our device. In the Endpoint Manager portal we can see that our device is up to date and the profile we created has been applied:
Summary
There are a lot of new concepts in this section so I highly recommend testing each one out in a lab environment to get used to how they work. In the next post we will go through some more technologies we can use to secure our devices and applications.
Check out the below articles to read more about Application Guard and Application control:
Microsoft Defender Application Guard (Windows 10) – Windows security | Microsoft Docs
Application Control for Windows – Windows security | Microsoft Docs


Pingback: Study Guide Series: Exam MS-500 – Implement and Manage Device and Application Protection (Part 2) – Sean McAvinue
Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Study Guide Series: Exam MS-500 – Implement and Manage Device and Application Protection (Part 3) – Sean McAvinue