This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Implement and manage Office 365 ATP” section:
- Monitor Office 365 ATP
- Conduct simulated attacks using Attack Simulator
Note: Office 365 ATP has recently been renamed Microsoft Defender for Office 365. This post will refer to it using the new name but the exam may contain references to the older name. For any topics referencing Office 365 ATP, read as Microsoft Defender for Office 365.
Conduct Simulated Attacks Using Attack Simulator
In the previous post, we covered configuring Microsoft Defender for Office 365 in our environment. Before we look at monitoring, we will conduct some simulated attacks using the Attack Simulator.
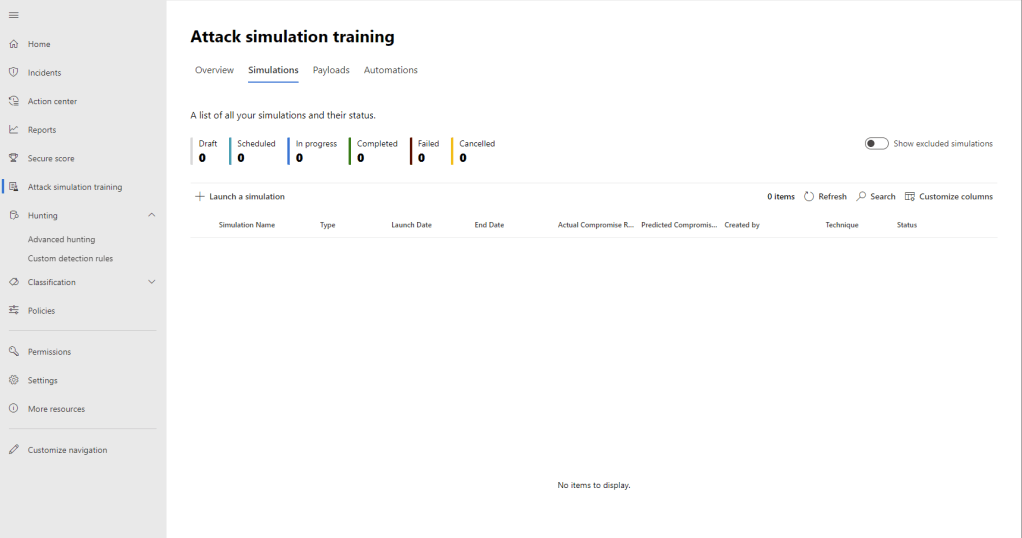
The attack simulator is available via the Microsoft 365 Security Center (https://security.microsoft.com). From here, we can access “Attack Simulation Training” in the navigation pane.
To run a new simulation, click the “Launch a simulation” option. We have several options available to us:
- Credential Harvest – “In this type of technique, a malicious actor creates a message, with a URL in the message. When the target clicks on the URL within the message, they are taken to a website, the website often shows input boxes for luring the target to submit their username and password. Typically, the page attempting to lure the target will be themed to represent a well-known website to build trust in the target.”
- Malware Attachment – “In this type of technique, a malicious actor creates a message, with an attachment added to the message. When the target opens the attachment, typically some arbitrary code such as a macro will execute in order to help the attacker install additional code on a target’s device, or further entrench themselves.”
- Link in Attachment – “In this type of technique, which is a hybrid of a Credential Harvest, a malicious actor creates a message, with a URL in an attachment, and then inserts the attachment into the message. When the target opens the attachment, they are represented with a URL in the actual attachment, if the target then clicks on that URL they are taken to a web site, the website often shows input boxes for luring the target to submit their username and password. Typically, the page attempting to lure the target will be themed to represent a well-known web page to build trust in the target.”
- Link to Malware – “In this type of technique, a malicious actor creates a message, with an attachment added to the message. However instead of directly inserting the attachment into the message, the malicious actor will host the attachment on a well-known file sharing site, (such as SharePoint, or Dropbox) and insert the URL to the attachment file path into the message. When the target clicks on the URL it will open the attachment, typically some arbitrary code such as a macro will execute in order to help the attacker install additional code on a target’s device, or further entrench themselves.”
- Drive-by URL – “In this type of technique, a malicious actor creates a message, with a URL in the message. When the target clicks on the URL within the message, they are taken to a website, the site will then try and run some background code to gather information about the target or deploy arbitrary code to their device. Typically, the website attempting to lure the target will be a well-known website that has been compromised in some fashion, or a clone of a well-known website itself. This familiarity with the website builds trust in the target that it is safe to click, this is also sometimes known as a watering hole technique.”

To test an attack simulation, select one of the simulations and hit “next”. We will use “Credential Harvest in this example. Give the simulation a name and description and hit next.

Next we choose a payload for the attack, we can use the pre-created payloads or define our own.
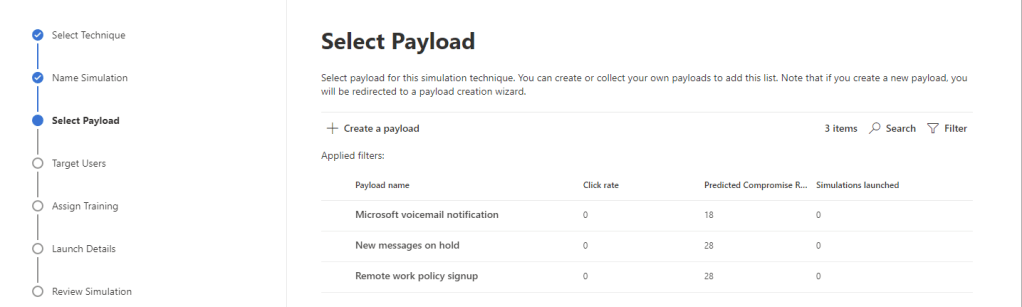
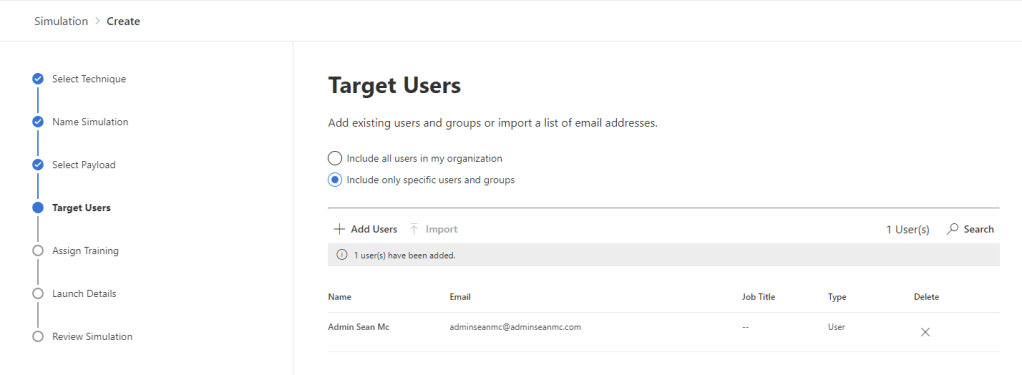
For this example, we’ll use the “Microsoft voicemail notification” to spoof a voicemail reminder. Select the desired payload and click next. On the next page, select all users or specific users to include. We can also customize the recipients based on location, role, department and how recently they have been targeted or if they are “repeat offenders”.
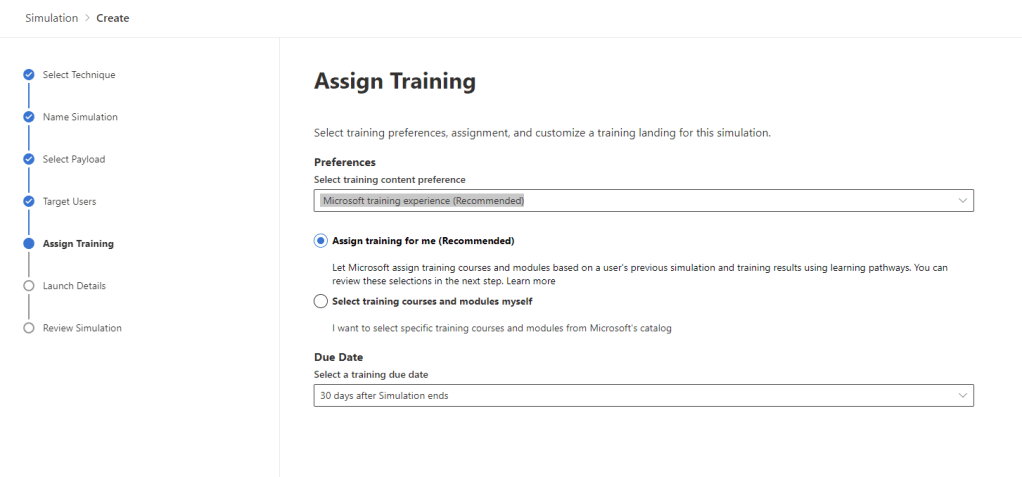
Next we assign training to educate users in being vigilant for malicious content. We can automatically assign training based on Microsoft recommendations or manually assign sessions from Microsoft’s catalogue. Users will be directed to training if they click on the malicious payload in the simulation.
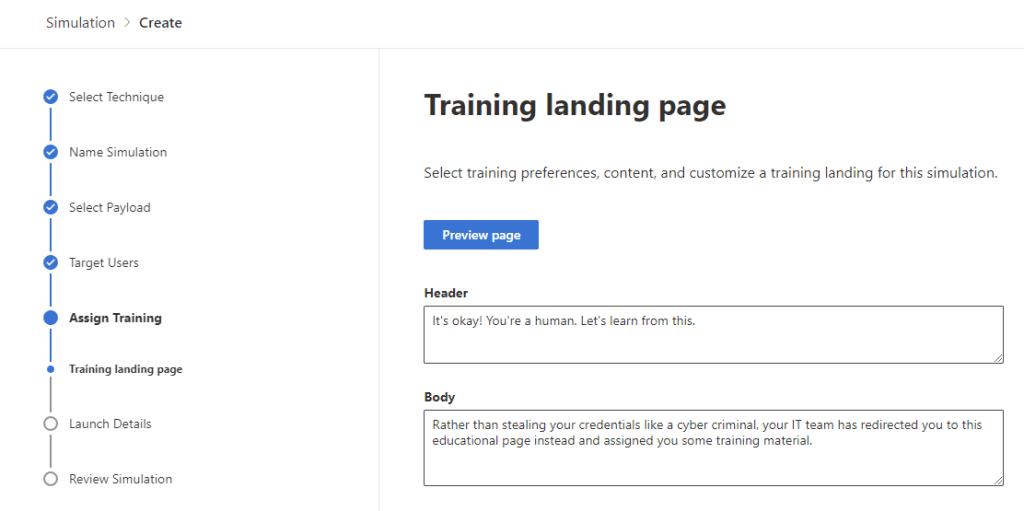
Next, we can customize the message that the users will see informing them of the simulation / training assignment. We can also preview the content. When ready, click next to continue.
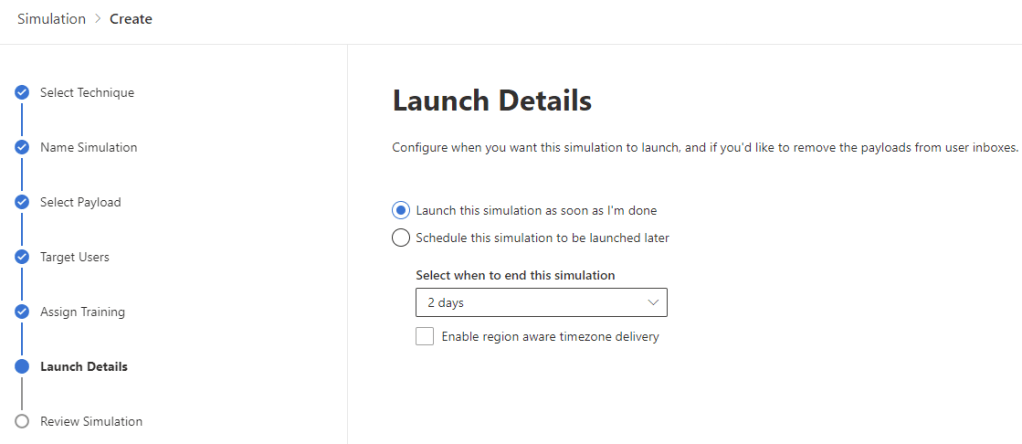
Now we schedule the simulation and select how long it will last.
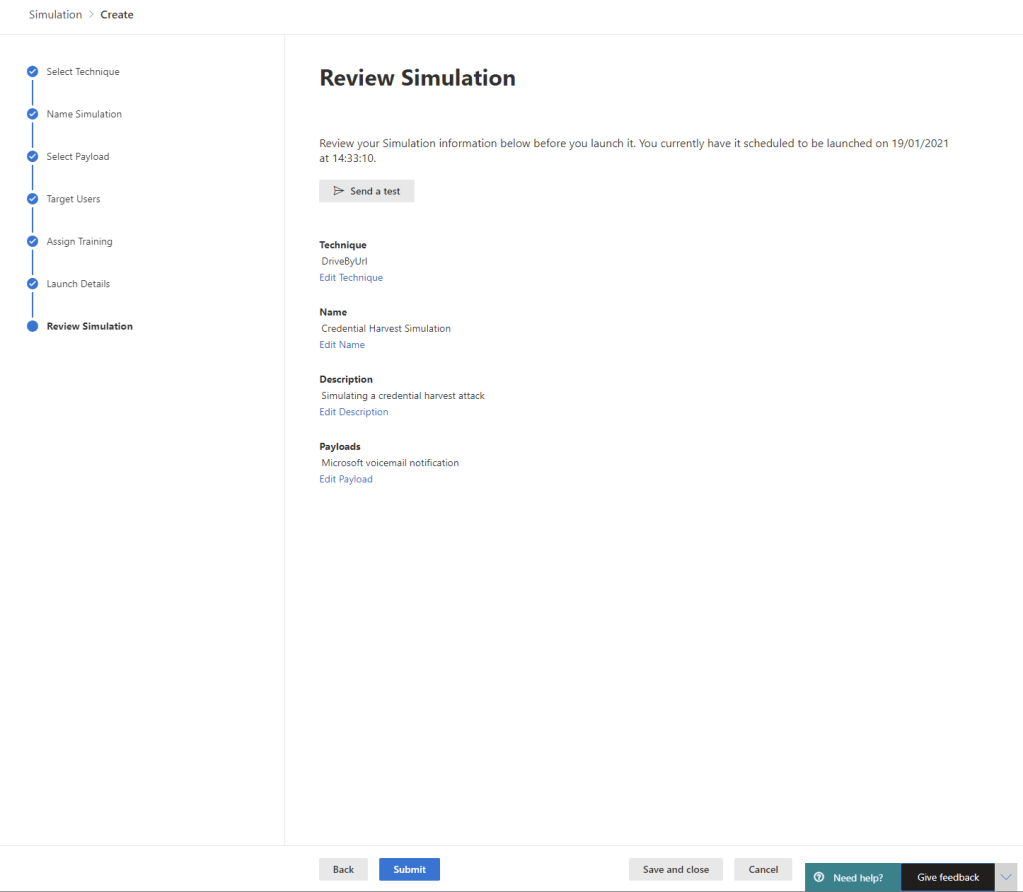
Finally, we can review and test our simulation before launching it using the “Submit” option.
Monitor Attack Simulation
To monitor the progress of our simulation, open the “Simulations” section from the “Attack Simulation Training” section of the Security portal, Click on the simulation to open it.
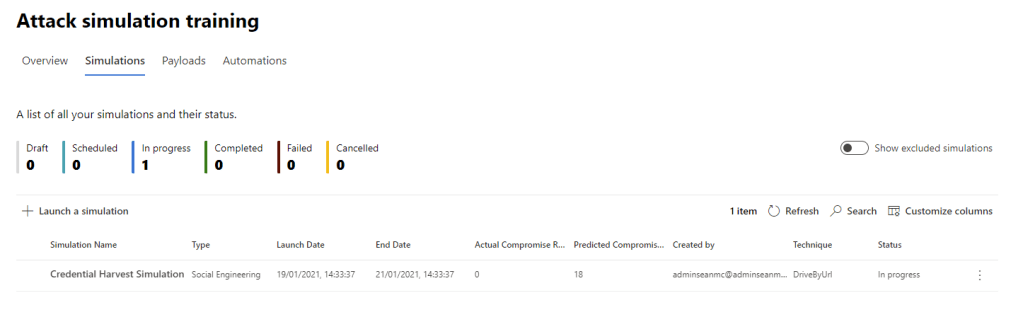
From here, we can see the details of the payload and monitor the progress of the simulation, along with any assigned training status.

Monitor Office 365 ATP
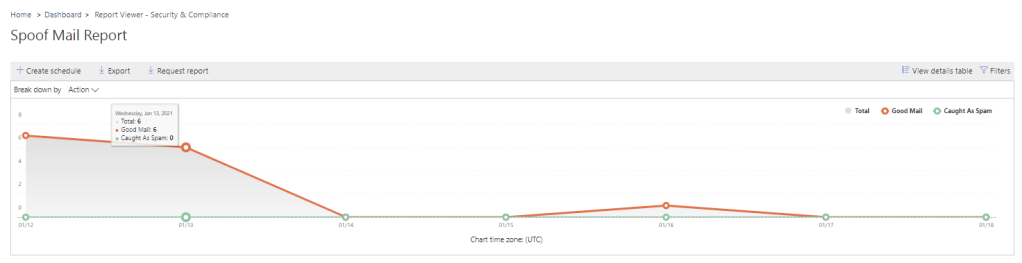
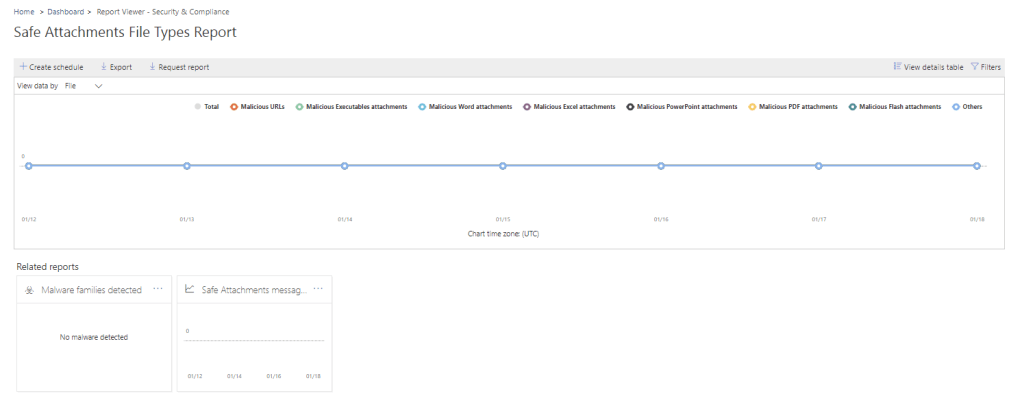
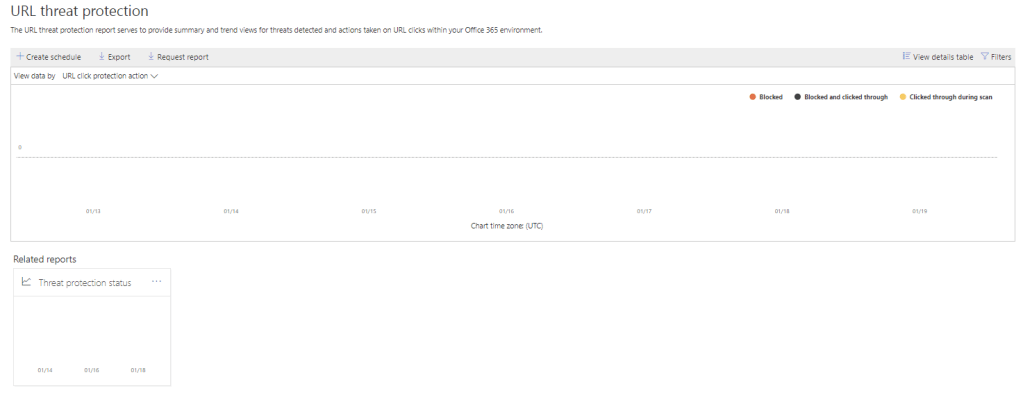
Once Defender is up and running, we can monitor the impact and performance of the configuration, this can help us to decide if we need to adjust our policies to meet our business requirements and to spot any trends or common attacks in our environment. From the Security & Compliance Center, we open up “Reports” -> “Dashboard” section and we will see a lot of information available to us. We can see reports related to Phishing Attempts, Safe Attachments, DLP, Safe Links, Spam Detections etc.
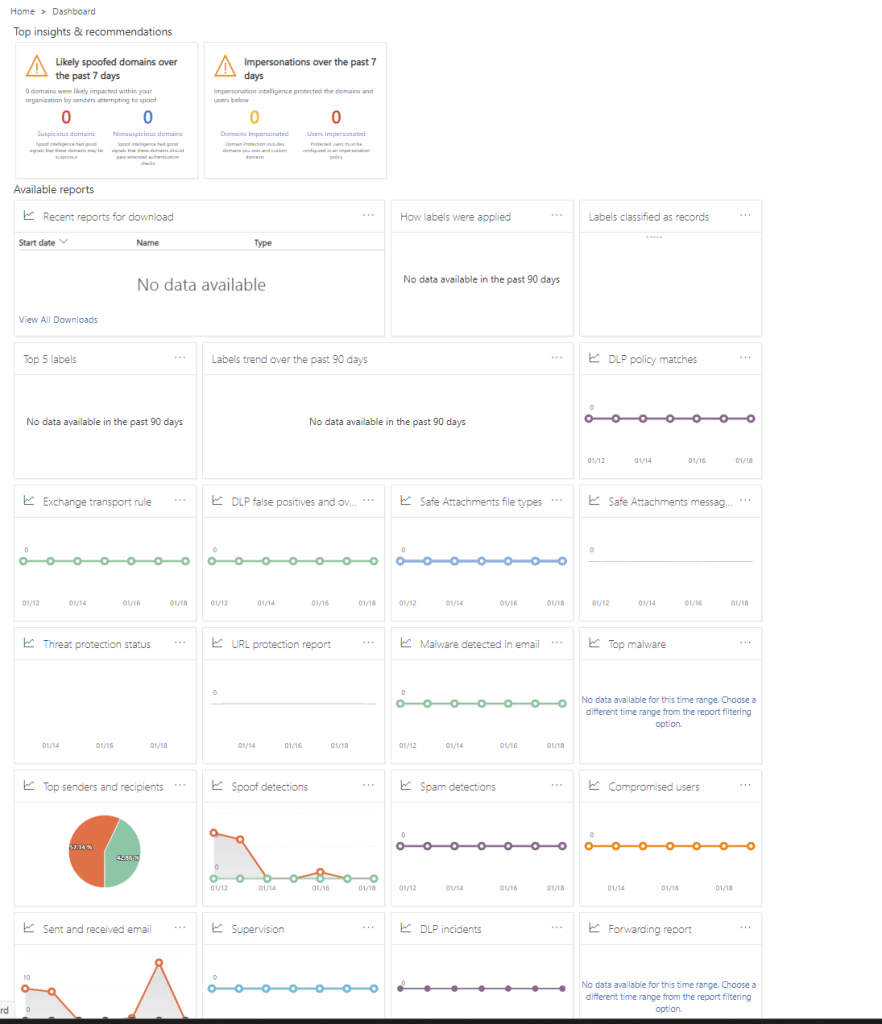
Clicking on any of these reports will open up the report viewer. From here we can export the underlying data and even schedule the report to be sent via email. Below are a few examples of reports that are available to us:
Summary
Over the last two posts we have looked at how we can use Microsoft Defender for Office 365 to help protect our organization from external and internal threats. There is a strong focus on email but this also extends to our SharePoint, Teams and OneDrive platforms. We can simulate attacks to assist with user training and we can monitor the performance of our Defender for Office 365 policies.
For more information on Microsoft Defender for Office 365, check out the below documentation:
Microsoft Defender for Office 365 – Office 365 | Microsoft Docs
Mail flow insights in the Mail flow dashboard – Office 365 | Microsoft Docs
Attack Simulator in Microsoft Defender for Office 365 – Office 365 | Microsoft Docs


Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Equipping Users to Combat Phishing Attacks in Office 365 – Sean McAvinue