This post is part of the overall MS-500 Exam Study Guide. Links to each topic as they are posted can be found here.
This post will cover the following exam topics listed under the “Monitor Microsoft 365 Security with Azure Sentinel” section:
- Plan and implement Azure Sentinel
Plan and Implement Azure Sentinel
Azure Sentinel is a cloud-based service, hosted in Azure which acts as a full security information event management (SIEM) solution. Sentinel collects data from a wide range of sources, including Microsoft 365, and uses Microsoft’s AI and analytics to detect and respond to potential threats rapidly.

Azure Sentinel is quite a large topic but for the MS-500 exam and this post, we will go through how we deploy Sentinel with a view to integrating Office 365 logs.
To deploy Sentinel, navigate to the Azure portal and in the search bar, search and open the “Azure Sentinel” option. On the Azure Sentinel page, click the “Create” button.

Next, we need to add a log analytics workspace, click “Connect workspace”.
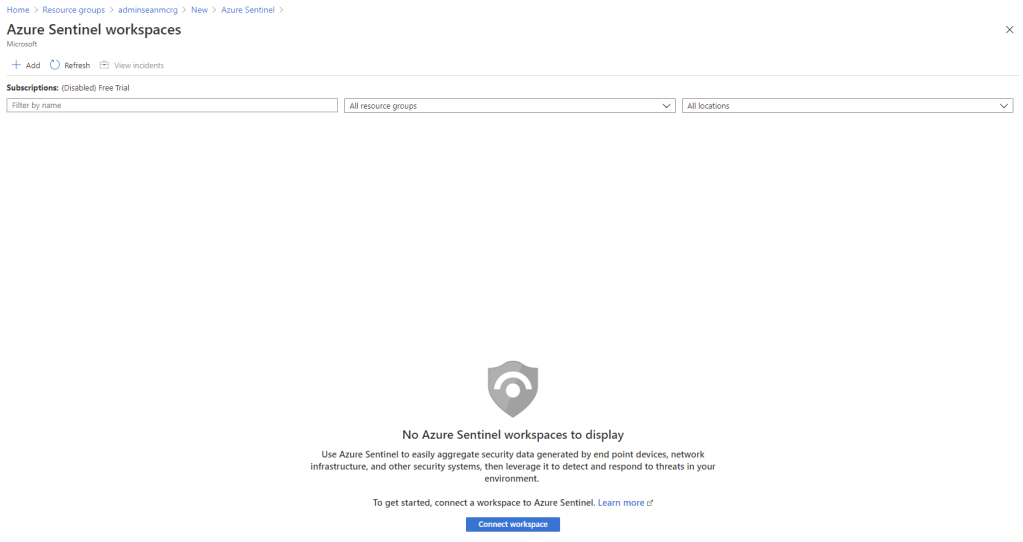
If there are no existing workspaces created, we can create a new one by clicking “create a new workspace”.

Enter the instance details, selecting Resource Group and Subscription and click “Review + Create”

Once the workspace is created, select it in the workspace page and click add.

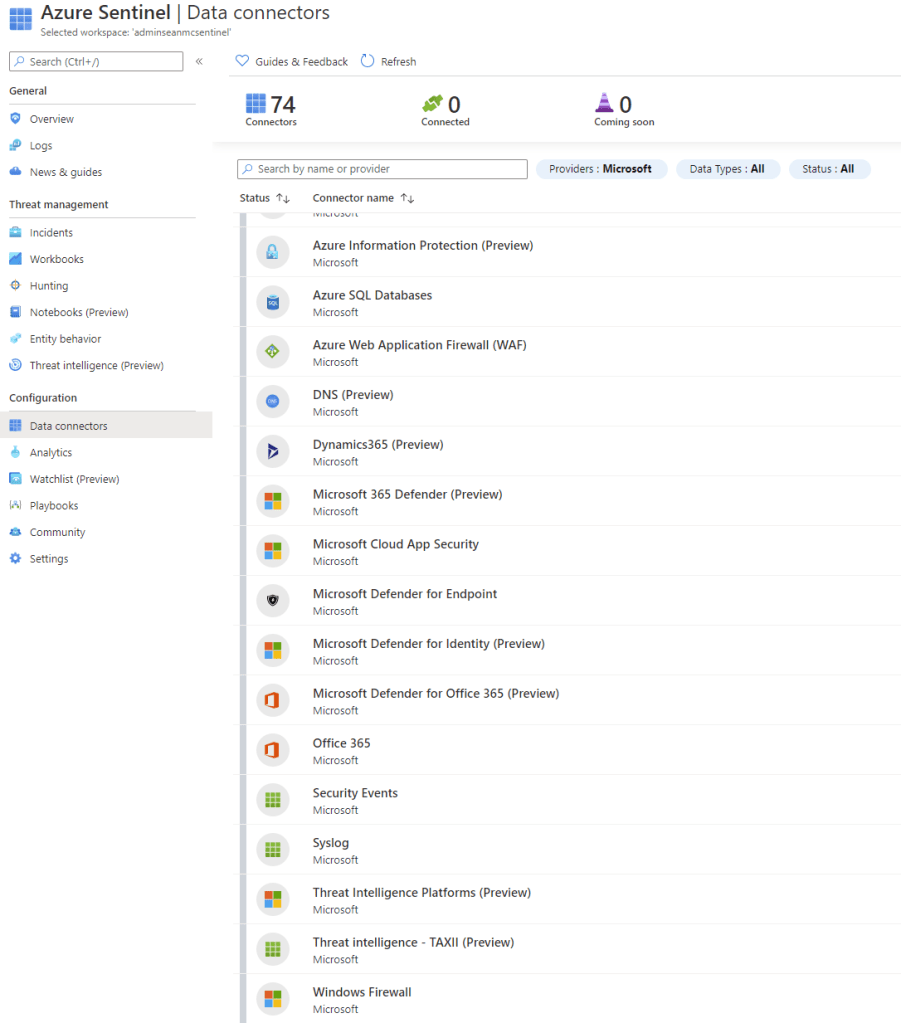
When the workspace is linked and Azure Sentinel is added we need to add our data connectors, on the main Azure Sentinel page, select “Data Connectors”. On this page we will see the list of supported connectors provided by Microsoft, the list is huge and most of it will be out of scope for this exam. If we filter by Microsoft, we can see a lot of the connectors we may be interested in.
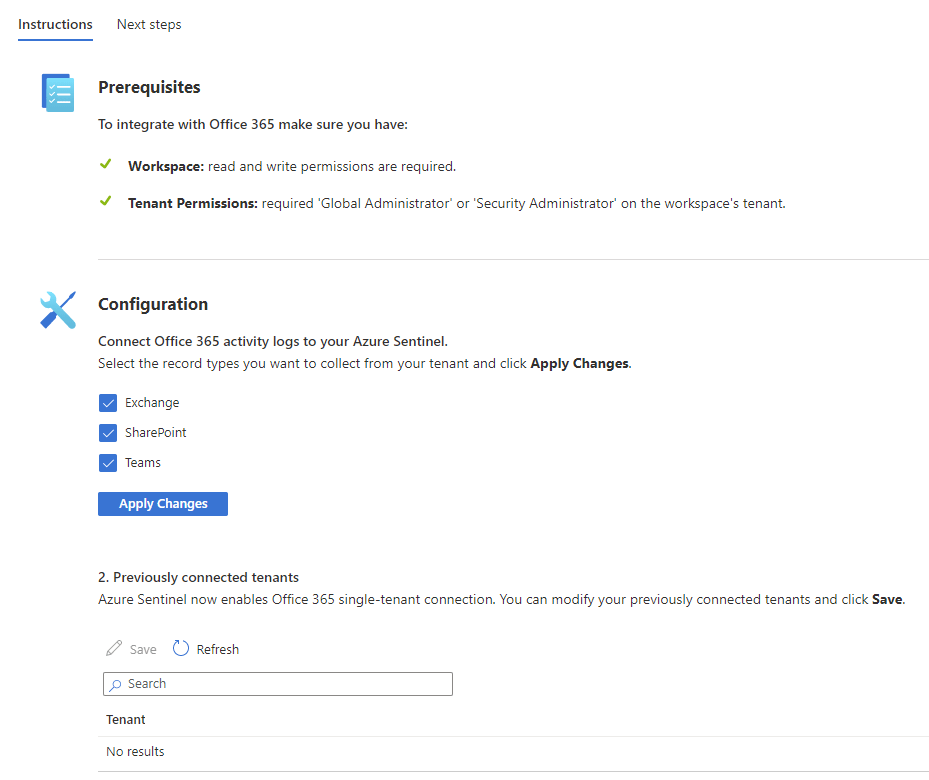
To get started, locate the Office 365 connector and click the button to “Open connector page”.
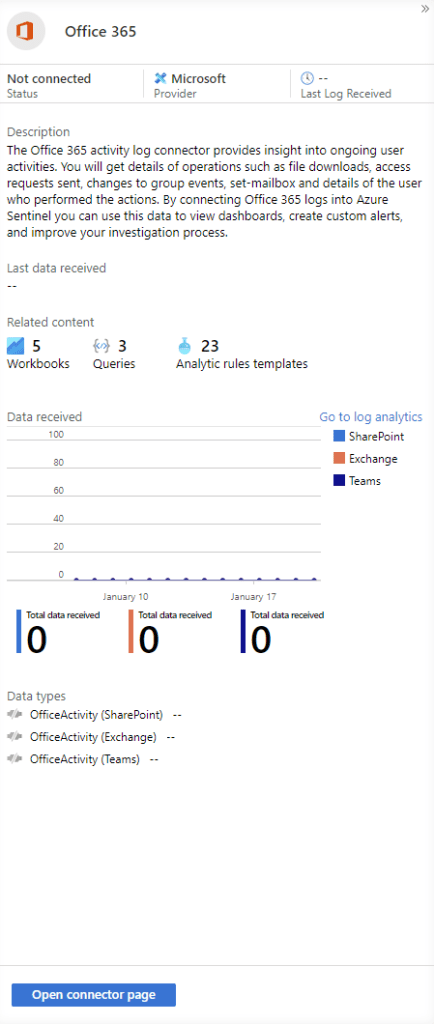
Select the Office 365 components to include (Exchange, SharePoint, Teams) and click apply changes.
We can also add more connectors while we are here. I’ve added the following connectors to help monitor our Microsoft 365 environment:
- Office 365
- Azure Active Directory
- Azure Active Directory Identity Protection
- Azure Information Protection (Preview)
- Microsoft Cloud App Security
- Microsoft Defender for Identity
- Microsoft Defender for Endpoint
- Microsoft Defender for Office 365 (Preview)
Details on how to add each connector are available here.
With our data source connected, let’s add a workbook to get some visualization in place. In the Sentinel page, open “Workbooks” and under “Templates” we can search for preconfigured workbook templates. We can also add new custom workbooks to Sentinel if we want. For now, let’s add the “Office 365” workbook template. Select Office 365 in the templates menu and click “View template” to check out a preview of what is available in the workbook. To add the workbook, click the save button.

When saving, select the region to save the workbook in.

Once saved, click “View saved workbook” to open it up.

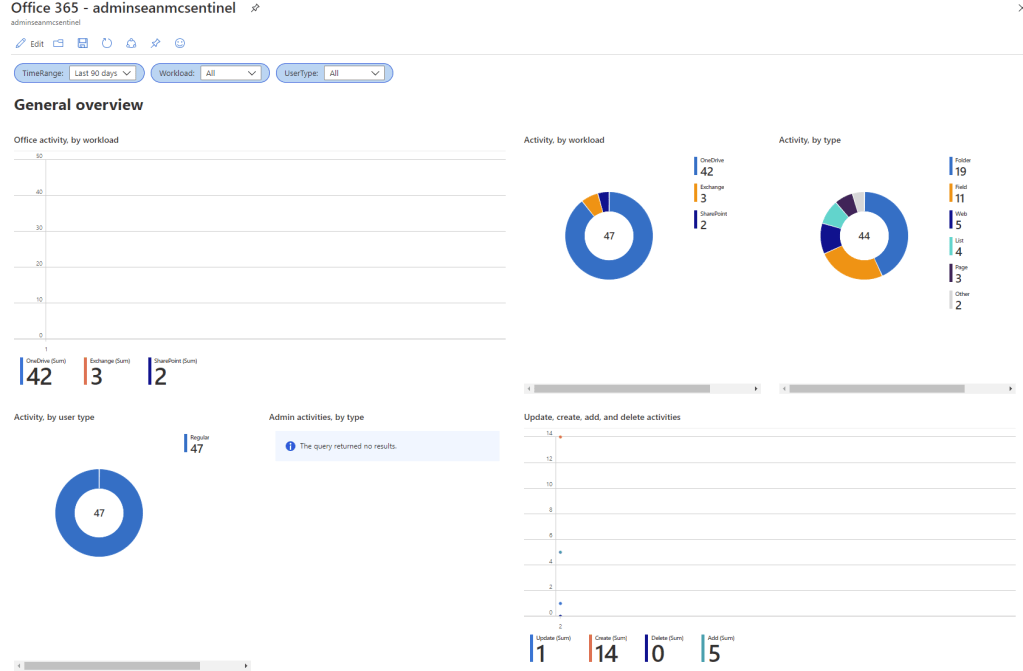
In the Office 365 workbook we can see a breakdown of activities in our Office 365 environment, we can filter by date, workload and user type if we like and event see all of the recent activity in our environment. If we like, we can modify the workbook with the “Edit” function to shift things around and add/remove items and queries to customise and prioritise the relevant data. (note: As this is a lab environment, there’s not a whole lot of data in my screenshots)

Summary
Now that we have Azure Sentinel set up and monitoring our Office 365 environment, in the next post we will dive deeper into how we can use Sentinel to detect, alert and remediate issues. If you are following along in your own environment, I highly recommend testing out the different data connectors and workbooks available and maybe even creating a custom workbook with specific data you may be interested in. You can also deploy data connectors for your non-Office 365 workloads to see the real power of an enterprise Azure Sentinel deployment. For more information on setting up Azure Sentinel and connecting data sources, check out the below links:
Quickstart: Onboard in Azure Sentinel | Microsoft Docs
Quickstart: Get started with Azure Sentinel | Microsoft Docs

Pingback: Study Guide Series – Exam MS-500: Microsoft 365 Security Administration – Sean McAvinue
Pingback: Study Guide Series: Exam MS-500 – Monitor Microsoft 365 Security with Azure Sentinel (Part 2) – Sean McAvinue