With Azure AD B2B, When we want to collaborate with another Microsoft 365 tenant, or even a personal Microsoft account, everything just works out of the box. In this scenario the federation is already in place and the guest user account is provisioned and redeemed without issue. That’s great for a lot of businesses we collaborate with but what about users who don’t have a Microsoft account. In this case, there are various options made available through Azure AD B2B that we can consider. Over the next few posts I will be going through the different methods we have to ensure we can seamlessly collaborate with starting with how we can implement Google Federation to collaborate with Gmail users. Note that this is for public Gmail accounts and federation with GSuite users will be detailed in a further post.
How Federation with Google works
To get started, let’s look at how it all hangs together. We know that in a standard Microsoft B2B scenario the Guest user can redeem the invitation via their own Azure AD tenant and that will act as the IDP to authenticate the user going forward. There are actually a lot more nuances to the Guest user redemption flow than just Microsoft though as we can see in the below diagram from the Microsoft documentation.
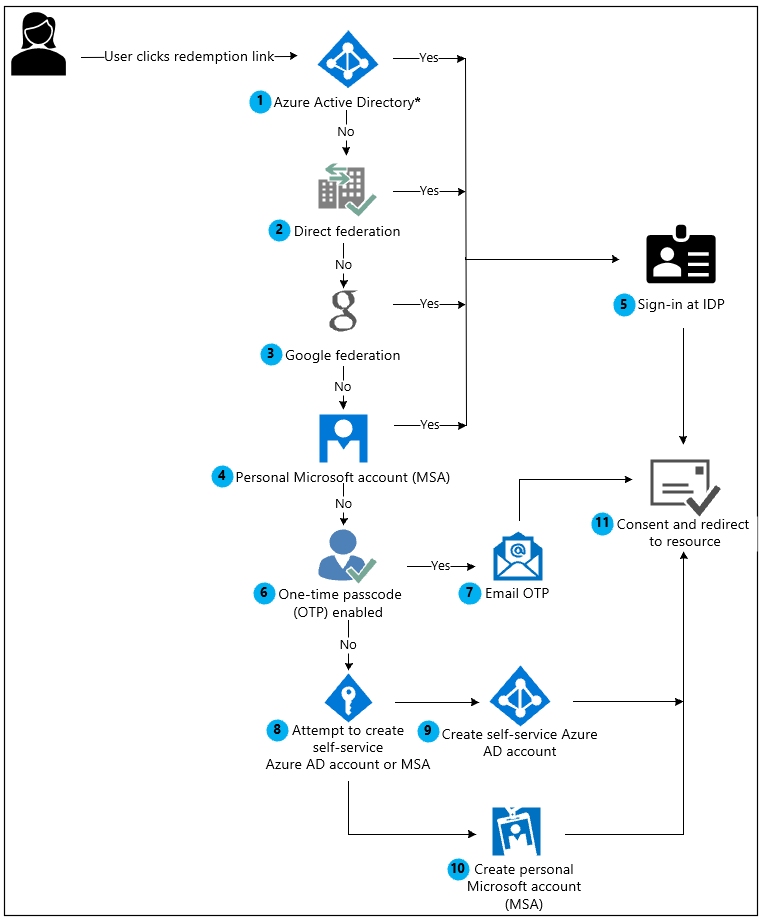
Here we can see there are multiple options for redemption and if we look specifically at Google Federation, we can invite and collaborate with public Gmail accounts as Guest users. We use the Google public cloud to authenticate our Guest users and from there, they can work away as normal.
Note: In the above diagram, step 8 – Self-Service Azure AD Account is being depreciated this year. I’ve covered that previously here.
Prepare for Enabling Google Federation
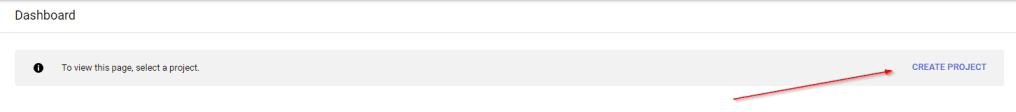
In order to enable Google Federation, we need to set up a Google Developer Account. Navigate to the Google developer console and select the option to “Create Project” from the Dashboard.
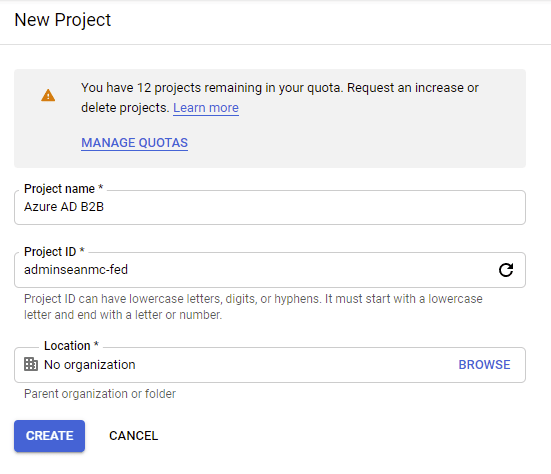
Give the project a name and optionally update the Project ID and Location then click “create”.
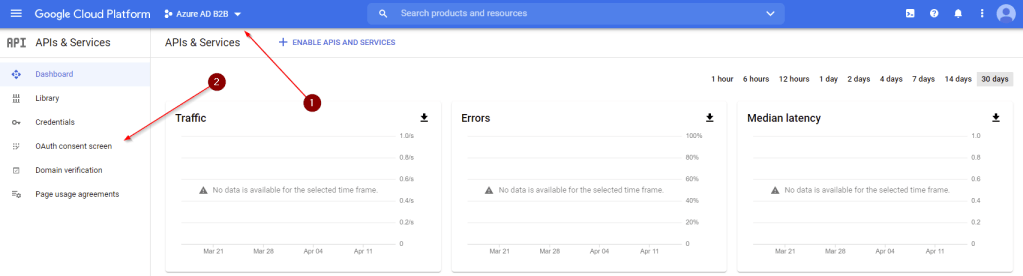
When the project is created, open up the the “API’s and Services” dashboard.
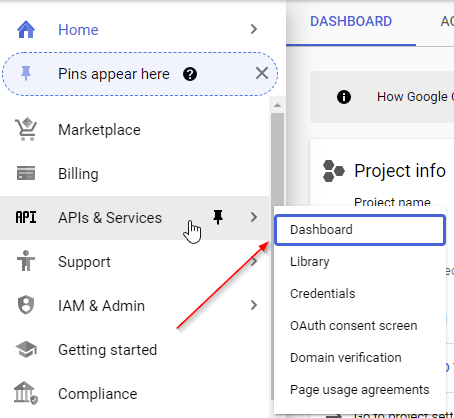
From here, make sure you have selected the correct project and select “OAuth Consent Screen”.
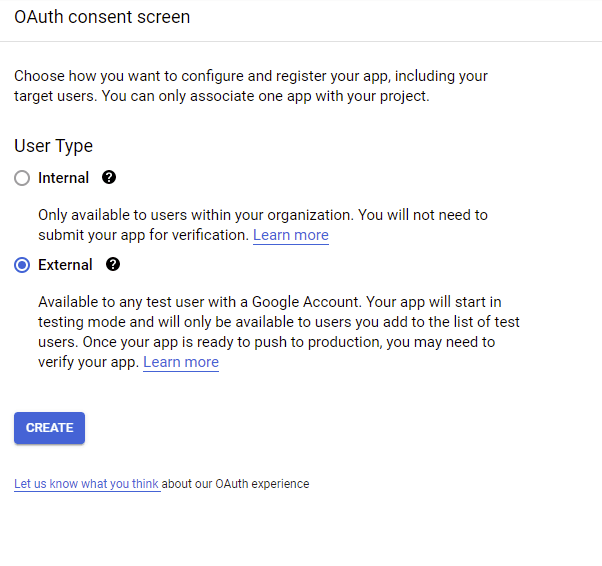
Select “External” for User Type and Click “Create”.
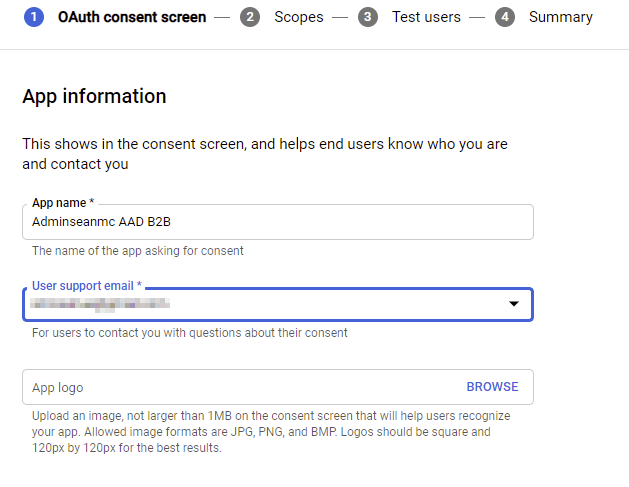
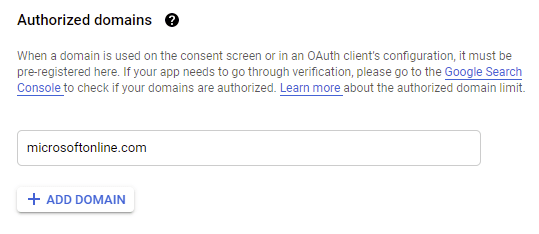
Give the App a name and support email then configure the Authorized Domain to add “microsoftonline.com”. When complete click “Save and Continue”
Next, navigate to the “Credentials” page within the APIs & Services Menu and click “Create Credentials”.
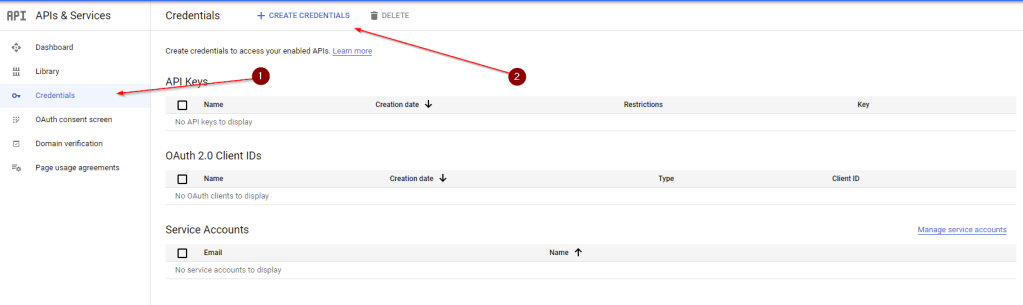
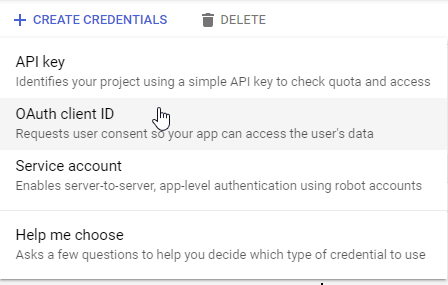
On the Create Credentials menu, select “OAuth Client ID”.
On the “Create OAuth Client ID” page, configure the following:
- Application Type – Web Application
- Name – A name for the application
- Authorized Redirect URIs – Add in “https://login.microsoftonline.com”
- Authorized Redirect URIs =- Add in “https://login.microsoftonline.com/te/<tenant ID>/oauth2/authresp” (tenantID) is the tenant/directory ID of your AAD tenant)
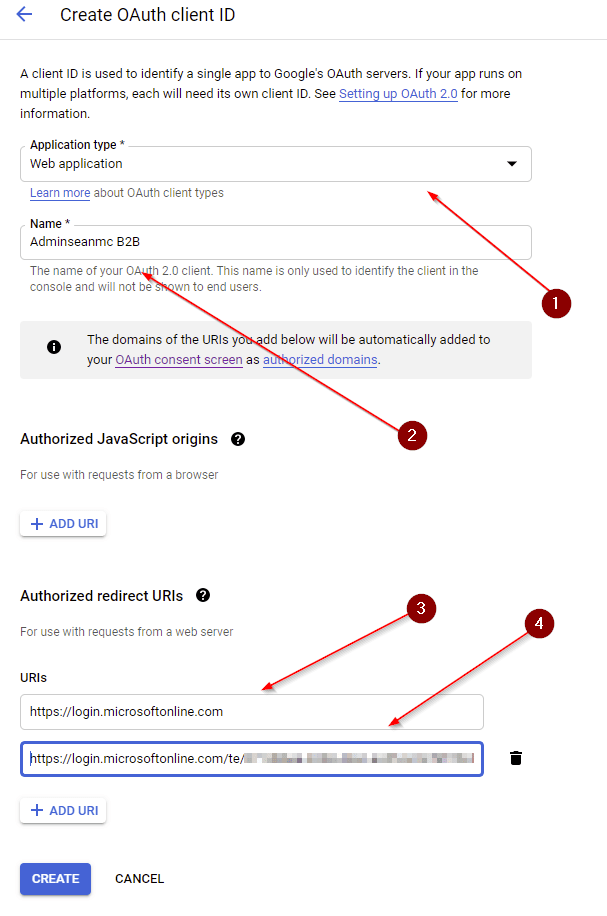
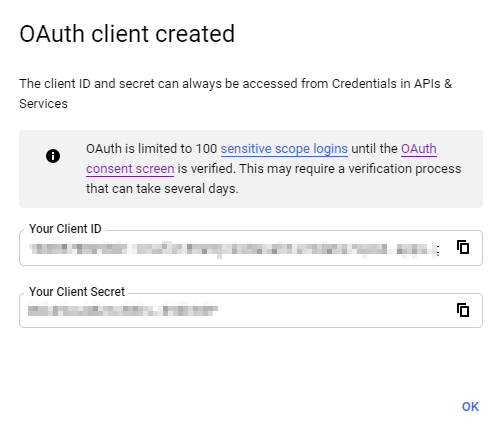
When done, click “Create” and you will receive a pop up with the Client ID and Secret, copy these values as we need them for the AAD confguration.
Enable Google Federation
To finish the configuration of Google Federation, Open the Azure AD Portal and Navigate to “External Identities” -> “All Identity Providers”, then click “Google”.
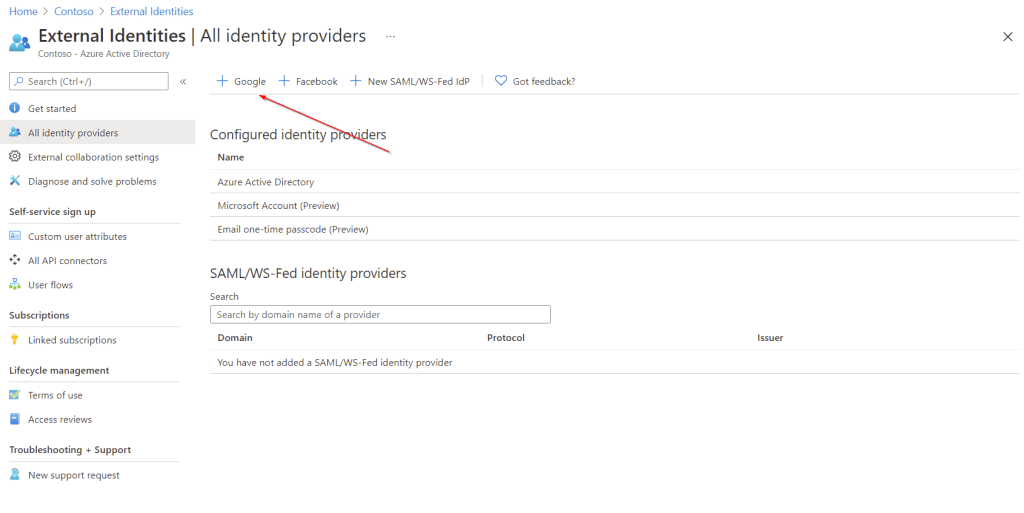
In the pop out window, enter the Client ID and Secret we copied previously and click “Save”.

Testing Google Federation
With everything in place for Google Federation, we can now test by sending a Guest Invitation to a Gmail account. We can do this a variety of ways but since we are already in the Azure AD Portal, we can open up the “Users” page and select “New Guest User”.
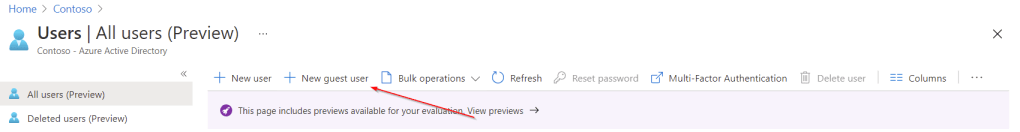
Select “Invite User” and add in a Gmail email address to invite and click “Invite”.
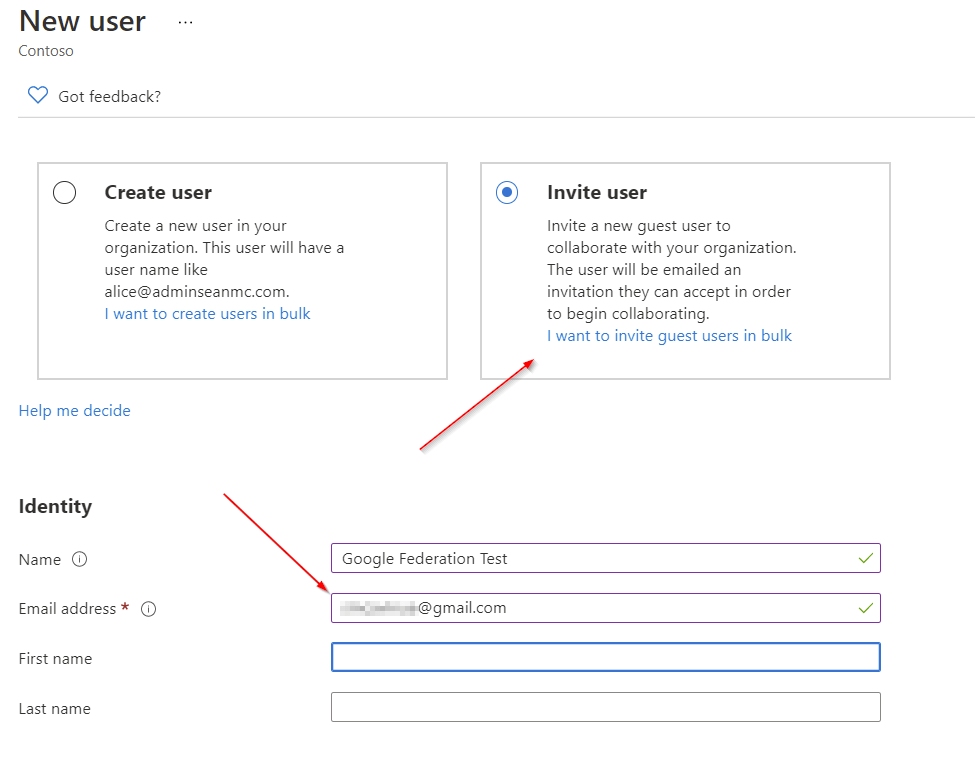
From the google account, we will receive the invitation by email as expected and we can click “Accept Invitation”.

On the next page we will see that we can authenticate to Google to redeem the invitation. Sign in here to continue.
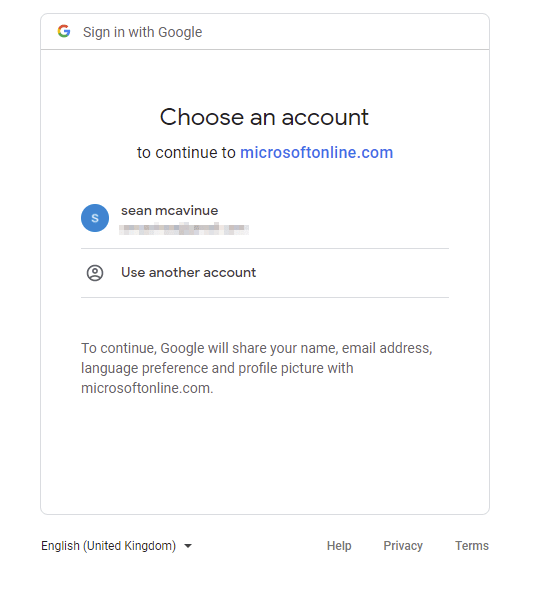
We then get prompted for permissions, click “Accept” to continue.
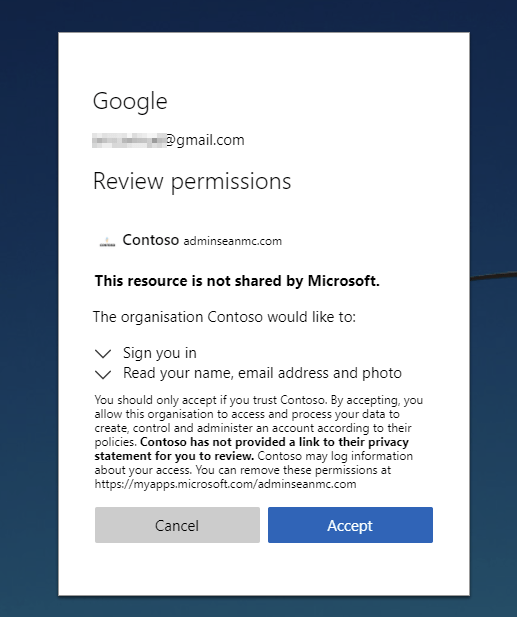
Once the permissions are accepted we will be redirected to the MyApps page where we will get any assigned applications.

That’s it! We can now successfully federate with Google for our B2B Guest user authentication! I will be posting on some of the other supported methods in the coming days/weeks but for now, more information on Google Federation is available at the below links.
Add Google as an identity provider for B2B – Azure AD | Microsoft Docs
Invitation redemption in B2B collaboration – Azure AD | Microsoft Docs

